A single procedural error during digital evidence collection can render an entire case inadmissible. For legal professionals and law enforcement in England, this is not a theoretical risk; it is a documented reality that has caused prosecutions to collapse at trial. Forensic acquisition sits at the heart of every digital investigation, governing how evidence is captured, preserved, and presented. Get it right, and your evidence stands up to the most rigorous cross-examination. Get it wrong, and opposing counsel will exploit every gap. This guide explains the forensic acquisition process using current UK standards, practical steps, and the legal principles that govern every stage.
Table of Contents
- What is forensic acquisition and why does it matter?
- ACPO principles and the legal framework
- The forensic acquisition process step by step
- Comparing acquisition methods: static, live, logical, and physical
- Challenges and edge cases in forensic acquisition
- Evolving standards and expert perspectives: what comes next?
- Expert digital forensics support for your legal case
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Preserve evidence integrity | Exact imaging with proper tools and audit trails is crucial for admissibility in UK courts. |
| Follow ACPO and legal standards | Complying with longstanding principles and law ensures evidence remains valid and challenge-proof. |
| Adapt to emerging challenges | Encryption, cloud storage, and evolving tools require continual learning and updated procedures. |
| Document every step | Comprehensive documentation and hash verification are essential in every digital acquisition for legal cases. |
What is forensic acquisition and why does it matter?
Forensic acquisition is not simply copying files from a device. It is a precise, controlled process. As defined in the digital evidence handling guidance, forensic acquisition is the process of creating an exact, bit-for-bit copy of digital storage media using write-blockers to prevent any alteration to the original data, ensuring integrity for legal use. Every sector of the storage device is captured, including deleted files, unallocated space, and file system metadata that a standard copy would miss entirely.
The stakes are significant. Digital evidence features in over 80% of UK police cases, meaning the quality of acquisition directly affects the majority of criminal proceedings in England and Wales. A poorly acquired image can be challenged on authenticity grounds, and once that challenge succeeds, the evidence is gone.
Write-blockers are hardware or software tools that allow data to be read from a device without permitting any writes back to it. Without one, simply connecting a device to a forensic workstation can alter timestamps and metadata, tainting the evidence. Tools such as FTK Imager and EnCase are industry standards, and understanding the forensic imaging process is essential for anyone involved in evidence handling.
“The reliability of digital evidence in court depends entirely on the integrity of the acquisition process. A compromised image is not evidence; it is a liability.”
Key reasons forensic acquisition matters for UK legal practice:
- It preserves the original device in its unaltered state
- It creates a verifiable copy that can be examined repeatedly without risk
- It supports compliance in forensic acquisition under PACE 1984 and the Criminal Procedure and Investigations Act
- It provides the foundation for expert witness testimony in court
- It enables digital forensics in UK courts to withstand defence scrutiny
ACPO principles and the legal framework
Now that the core purpose of forensic acquisition is clear, it is vital to understand the legal pillars underpinning every investigation. The Association of Chief Police Officers (ACPO) principles remain the cornerstone of digital evidence practice in England and Wales. Even in 2026, they are embedded in Home Office policy and referenced in court proceedings.
The ACPO principles set out four clear rules that every practitioner must follow:
- Principle 1: No action taken by investigators should change data held on a digital device or storage media
- Principle 2: Where access to original data is necessary, the person doing so must be competent and able to explain their actions
- Principle 3: An audit trail of all processes applied to digital evidence must be created and preserved
- Principle 4: The investigator in charge holds overall responsibility for ensuring these principles are followed
These principles interact directly with the Police and Criminal Evidence Act 1984 (PACE) and the Criminal Procedure and Investigations Act 1996 (CPIA). Chain of custody documentation, cryptographic hash values, and detailed audit trails are not optional extras; they are legal requirements for digital forensics that courts expect to see.
“Adherence to ACPO principles is not merely best practice. It is the minimum standard that separates admissible evidence from contested data.”
Failure to maintain a documented chain of custody, for example, gives defence teams grounds to argue that evidence may have been tampered with or contaminated. Ensuring legal integrity at every stage is therefore both a procedural and a strategic necessity.
The forensic acquisition process step by step
Having examined the guiding framework, let us break down the practical, hands-on steps involved in acquiring digital evidence correctly. Each stage builds on the last, and skipping any one of them creates a vulnerability that can be exploited in court.
- Device isolation: Immediately prevent the device from connecting to any network. For mobile phones, use a Faraday bag to block signals. For computers, disconnect network cables and disable wireless adapters before powering down.
- Chain of custody documentation: Record the device’s condition, serial number, location of seizure, and the identity of every person who handles it from this point forward.
- Write-blocker connection: Attach a validated hardware write-blocker between the device and the forensic workstation before any imaging begins.
- Image acquisition: Use a validated tool such as FTK Imager or EnCase to create a forensic image of the entire storage media. The process captures every bit, including empty space.
- Hash verification: Generate MD5 and SHA-256 hash values for both the original device and the forensic image immediately after acquisition. Matching hashes confirm the image is identical to the source.
- Documentation and reporting: Record all tool versions, hash values, acquisition times, and operator details in a formal log. This becomes part of the audit trail.
The table below summarises the key tools and their primary functions:
| Tool | Primary function | Validation standard |
|---|---|---|
| FTK Imager | Disk imaging and preview | NIST / ISO 27037 |
| EnCase | Imaging and analysis | NIST / ISO 27037 |
| Cellebrite UFED | Mobile device acquisition | NIST / ISO 27037 |
| Hardware write-blocker | Prevents data alteration | ACPO Principle 1 |
As outlined in the forensic imaging methodology, hash verification with MD5 and SHA-256 is the accepted standard for confirming image integrity. Refer to the forensic process steps and forensics tools for UK legal teams for further technical guidance.
Pro Tip: Always generate two hash values using different algorithms. If one is ever challenged, the second provides independent corroboration of image integrity.
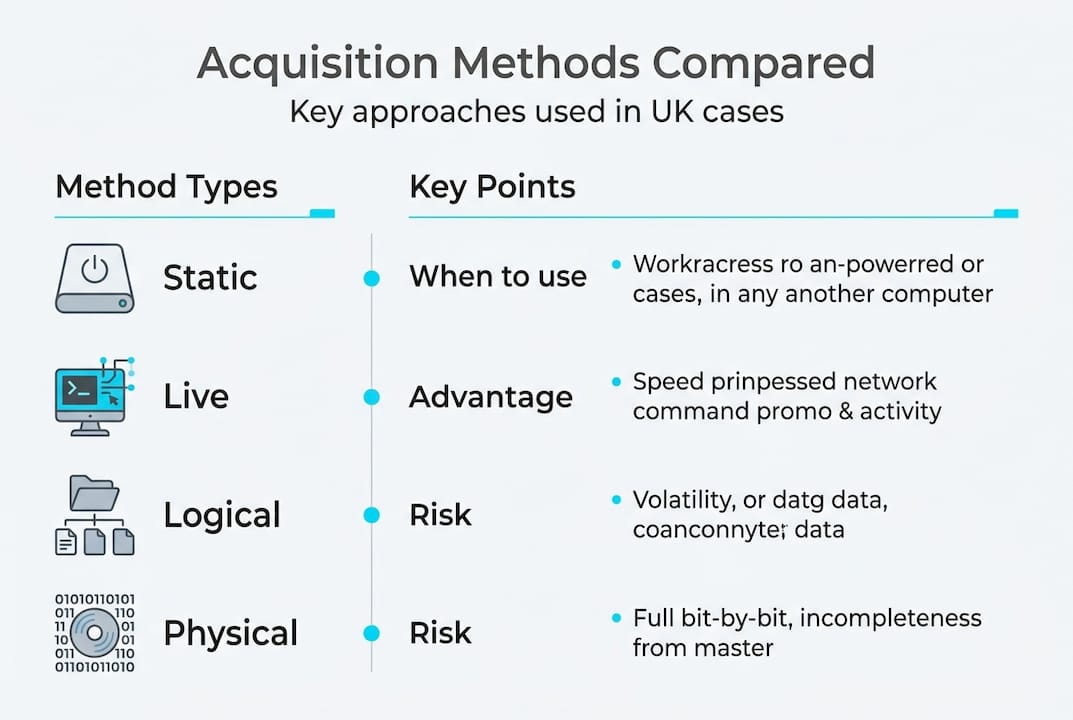
Comparing acquisition methods: static, live, logical, and physical
With the step-by-step process in mind, it is helpful to compare the different methodologies you may encounter in practice. Not every case allows for the same approach, and choosing the wrong method can compromise the evidence you recover.
As detailed in the forensic acquisition methodologies literature, the four primary approaches each carry distinct implications:
| Method | When to use | Key advantage | Key risk |
|---|---|---|---|
| Static (powered-off) | Device is off; preferred default | No volatile data loss risk | Misses RAM contents |
| Live acquisition | Device is running; RAM data needed | Captures volatile data | Risk of data change during capture |
| Physical | Full bit-stream of storage media | Maximum data recovery | Time-intensive; requires write-blocker |
| Logical | File system level only | Faster; suitable for large volumes | Misses deleted files and unallocated space |
Static imaging remains the safest and most legally defensible approach for the majority of cases. Live acquisition is reserved for situations where volatile data such as encryption keys, running processes, or active network connections must be preserved before shutdown. For mobile phone forensics practice, logical acquisition is often the starting point, though physical acquisition is preferred where full recovery is required.
Pro Tip: If you are unsure whether to perform a live acquisition, document your reasoning in writing before proceeding. Courts will scrutinise the decision, and a clear rationale protects both the evidence and the investigator.
Challenges and edge cases in forensic acquisition
The real world rarely fits textbook examples. Let us consider the most pressing challenges practitioners will face in active investigations.
The most common edge cases include:
- Encrypted or password-protected devices: Full-disk encryption such as BitLocker or FileVault can render a forensic image unreadable without the correct key. Investigators must consider whether legal powers exist to compel disclosure under the Regulation of Investigatory Powers Act 2000.
- Cloud and remotely stored data: Data held on third-party servers, often outside UK jurisdiction, requires different legal instruments and raises questions about cloud forensics challenges that static imaging cannot address.
- Damaged media: Physically damaged drives may require specialist recovery before imaging. Attempting standard acquisition on a failing drive can cause further data loss.
- Live systems: Shutting down a running system without live acquisition can destroy volatile data permanently, as noted in the digital evidence checklist for UK legal cases.
Beyond technical challenges, there is a systemic problem. The digital forensics crisis in UK policing has created massive backlogs due to the sheer volume and complexity of cases, with delays directly risking case collapses and miscarriages of justice. For legal professionals, this underscores the value of instructing independent forensic experts who can work to your timeline rather than a constrained police queue. Guidance on reporting on digital evidence challenges can help practitioners navigate these pressures effectively.
Evolving standards and expert perspectives: what comes next?
Finally, it is important to look at where the discipline is headed, with practical advice for staying ahead of evolving standards. The ACPO principles have served UK digital forensics well for over two decades, but the landscape has shifted considerably.
Cloud storage, AI-generated data, and increasingly sophisticated encryption present scenarios that the original ACPO framework did not anticipate. As calls for updating ACPO principles make clear, the principles remain timeless in spirit but require modernisation for cloud, AI, and encryption contexts, with a renewed emphasis on least intrusive methods as directed by the Home Office.
“The foundational values of ACPO are sound, but the technical environment has outpaced the guidance. Practitioners need updated frameworks that address cloud-native evidence and AI-generated artefacts without compromising the core principles of integrity and accountability.”
International alignment is also becoming more relevant. Collaboration with Interpol, Europol, and the National Police Chiefs’ Council (NPCC) increasingly requires that UK practitioners demonstrate compliance with ISO 27037 and other internationally recognised standards. Staying current with forensic reporting advancements is no longer optional for those working on cross-border or complex digital cases.
Continual tool validation is equally critical. A tool that was certified two years ago may not handle newer file systems or encryption schemes correctly. Expert judgment, not just software output, remains the decisive factor in producing reliable forensic evidence.
Expert digital forensics support for your legal case
As digital forensics evolves, it is vital to have expert support tailored to your unique case needs. Whether you are dealing with encrypted devices, cloud-based evidence, or time-sensitive acquisitions, the quality of your forensic process will determine the strength of your evidence in court. Computer Forensics Lab provides specialist digital forensics services to legal professionals and law enforcement across England, covering everything from initial acquisition through to expert witness reporting. Our team works to your case timeline, maintains rigorous chain of custody, and produces court-ready documentation. For complex litigation, our forensic consultancy for litigation service offers bespoke support at every stage of the investigation, ensuring your digital evidence is acquired, preserved, and presented to the highest standard.
Frequently asked questions
What is the primary purpose of forensic acquisition?
The main goal is to produce a precise, unaltered copy of digital evidence that can be reliably used in court. A bit-for-bit forensic image created with write-blockers ensures the original data remains untouched throughout the investigation.
Why are ACPO principles still relevant in 2026?
The ACPO principles provide a foundational framework that courts in England and Wales continue to reference when assessing whether digital evidence has been properly handled and preserved.
What are common challenges in digital forensic acquisition?
Practitioners regularly encounter encrypted or locked devices, cloud-hosted data, physically damaged media, and live systems where shutdown would destroy volatile evidence.
How do you ensure a forensic image is admissible in court?
Admissibility depends on following ACPO principles, using NIST-validated tools, generating matching hash values, and maintaining a complete, documented chain of custody under PACE 1984 and CPIA requirements.
Has forensic acquisition changed with the rise of AI and cloud storage?
The core principles remain sound, but updates to ACPO guidance are increasingly necessary to address cloud-native evidence, AI-generated artefacts, and advanced encryption that the original framework did not anticipate.