Digital evidence is often assumed to be inherently reliable, a digital fingerprint that cannot lie. Yet this misconception has contributed to serious justice failures across the UK. Mishandling digital evidence leads to data corruption, inadmissible findings, and wrongful convictions. For legal professionals, law enforcement, and corporate security teams in 2026, understanding how to secure digital evidence is not optional. It determines whether investigations succeed, whether litigation holds up in court, and whether privacy rights remain protected. This guide explores why securing digital evidence is essential and how modern practices ensure integrity throughout investigations.
Table of Contents
- Understanding The Crucial Role Of Securing Digital Evidence
- Challenges And Scrutiny In Managing Digital Evidence Versus Physical Evidence
- Innovations And Best Practices For Ensuring Digital Evidence Integrity
- Applying Secure Digital Evidence Practices In UK Investigations And Litigation
- Discover Expert Digital Forensics Services To Secure Your Evidence
- Frequently Asked Questions About Securing Digital Evidence
Key takeaways
| Point | Details |
|---|---|
| Prevents justice failures | Proper securing stops backlogs and errors that lead to wrongful outcomes in criminal and civil cases. |
| Requires stricter scrutiny | Courts examine digital evidence more critically than physical evidence due to volatility and tampering risks. |
| Chain of custody essential | Maintaining documented custody prevents challenges to evidence authenticity and admissibility in court. |
| Blockchain innovation | Emerging blockchain technology creates tamper-proof audit trails for evidence handling and verification. |
| Impacts all stakeholders | Securing practices affect investigations, litigation success, and legal defence strategies across the UK. |
Understanding the crucial role of securing digital evidence
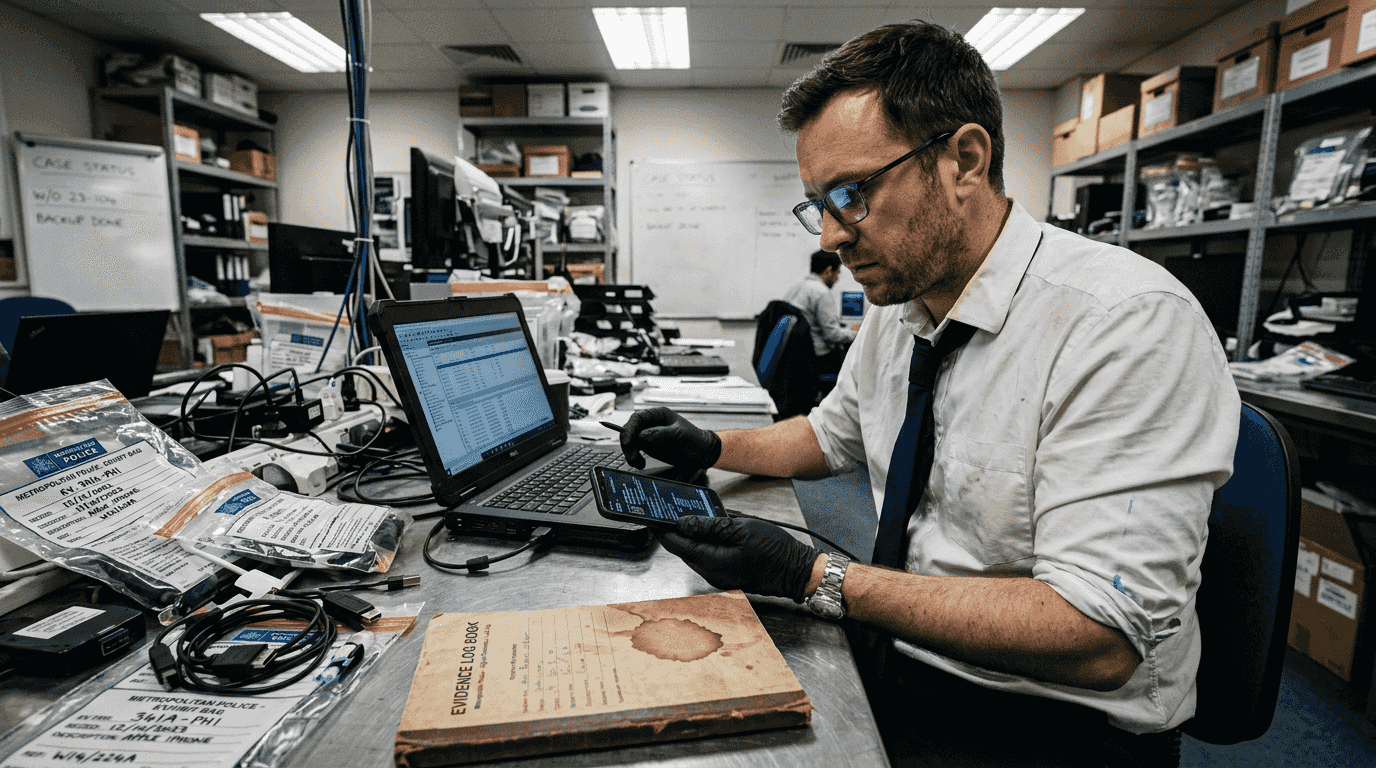
Digital evidence encompasses data from computers, mobile devices, cloud storage, social media platforms, and network logs. In 2026, the majority of UK criminal and civil cases involve some form of digital evidence. From fraud investigations to intellectual property disputes, digital artefacts provide critical insights that physical evidence cannot.
Yet digital evidence presents unique risks. Data can be altered, corrupted, or lost through improper handling. A single misstep during extraction can render evidence inadmissible. Unlike physical evidence that remains static, digital files are volatile. Metadata changes with access, timestamps shift, and deleted data can be overwritten permanently.
Securing digital evidence serves four fundamental purposes:
- Ensuring accuracy and completeness of captured data
- Maintaining legal admissibility through proper protocols
- Complying with privacy regulations and data protection laws
- Delivering justice by preventing evidence tampering or loss
The balance between effective investigations and privacy rights remains delicate. Project Odyssey demonstrates how digital forensics transforms policing by preventing miscarriages of justice through targeted extraction methods. Rather than seizing entire devices and extracting everything, investigators now focus on specific data relevant to cases. This approach respects privacy whilst gathering necessary evidence.
Legal professionals must recognise that improper securing creates vulnerabilities. Defence teams can challenge evidence authenticity. Prosecutors may lose cases due to chain of custody breaks. Corporate investigations can face regulatory penalties for mishandling personal data.
“Securing digital evidence prevents miscarriages of justice from backlogs and failures, balancing investigative needs with privacy rights via targeted extraction.”
Understanding why preserving digital evidence matters forms the foundation for all subsequent procedures. Without this knowledge, teams risk compromising entire investigations.
Pro Tip: Always plan your extraction strategy before accessing devices. Define exactly what data you need, document your rationale, and limit your scope to protect privacy whilst gathering admissible evidence.
Challenges and scrutiny in managing digital evidence versus physical evidence
Law enforcement and legal teams face distinct challenges with digital evidence that physical evidence does not present. Resource constraints compound these difficulties. Police forces struggle with backlogs as digital evidence volumes explode. A single smartphone can contain hundreds of gigabytes requiring analysis.
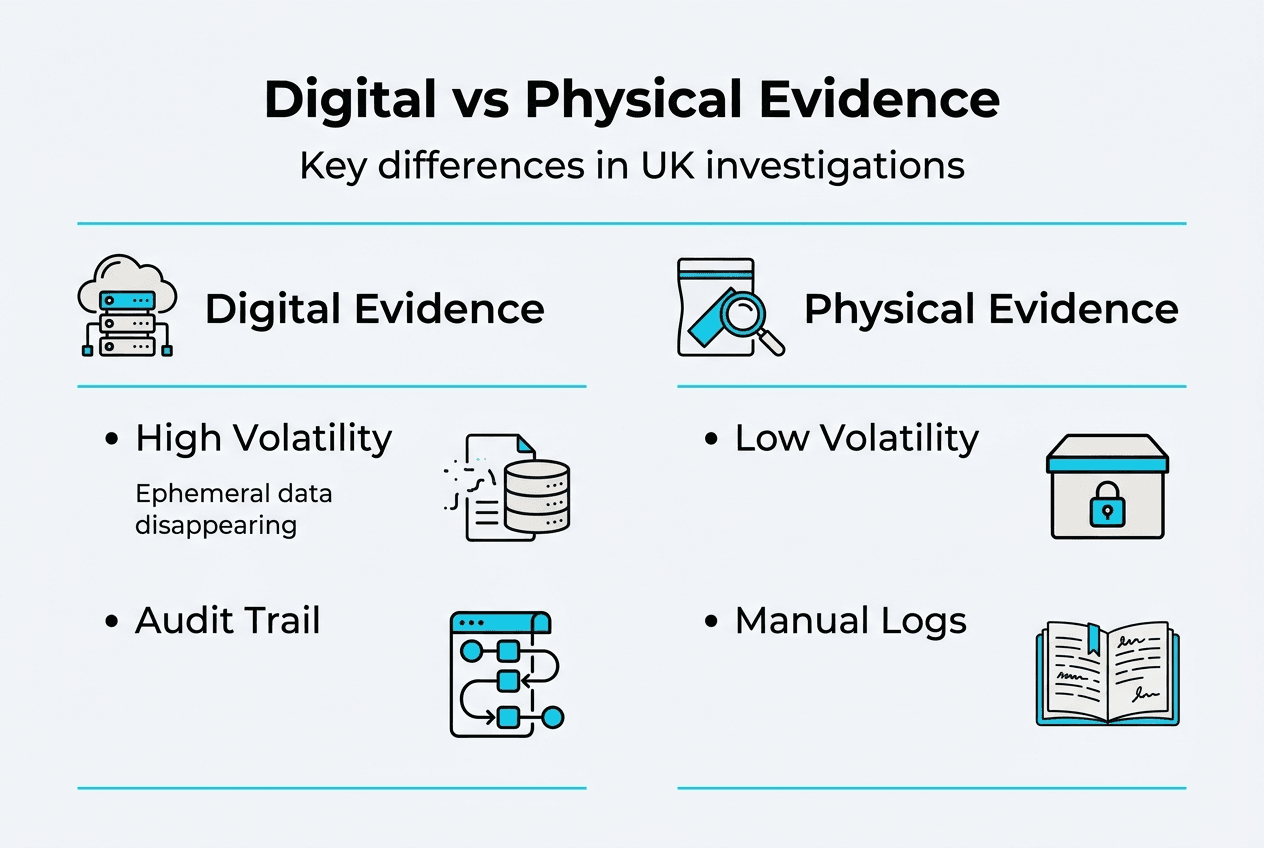
Courts apply stricter scrutiny to digital than physical evidence due to inherent volatility. Judges and juries understand that fingerprints on a weapon remain unchanged. Digital files, however, can be modified without visible traces. This perception, whether fully accurate or not, means digital evidence faces heightened challenges during proceedings.
| Aspect | Digital Evidence | Physical Evidence |
|---|---|---|
| Volatility | High (easily altered or deleted) | Low (stable and tangible) |
| Tampering risk | Significant without proper controls | Lower with standard handling |
| Court scrutiny | Stricter protocols required | Established procedures accepted |
| Admissibility challenges | Chain of custody breaks fatal | More forgiving standards |
| Resource demands | Specialist tools and expertise | Standard forensic processes |
Resource crises force difficult decisions. Should investigators prioritise volume or quality? Rushing through digital evidence analysis to clear backlogs increases error risks. Yet delays deny justice to victims and defendants alike.
Overreach presents another danger. Digital devices contain vast personal information unrelated to investigations. Accessing more data than necessary violates privacy rights and risks evidence exclusion. The Investigatory Powers Act 2016 and Data Protection Act 2018 impose strict limits on what can be accessed and retained.
Transparency and documentation address these challenges. Every action taken with digital evidence must be recorded. Who accessed what data, when, why, and what changes occurred. This audit trail satisfies court requirements and demonstrates compliance with legal standards.
Pro Tip: Create detailed logs from the moment you encounter digital evidence. Record device states, actions taken, tools used, and personnel involved. This documentation proves invaluable when defending evidence integrity in court.
Innovations and best practices for ensuring digital evidence integrity
Maintaining chain of custody remains paramount for digital evidence integrity. Chain of custody documents every person who handled evidence, when transfers occurred, and what actions were performed. Breaks in this chain provide grounds for excluding evidence entirely.
Traditional chain of custody relies on paper logs and manual signatures. Human error creates vulnerabilities. Logs get lost, signatures are forged, timestamps are incorrect. Blockchain technology offers tamper-proof solutions for chain of custody management. Each evidence transfer creates an immutable record on the blockchain. Timestamps cannot be altered. Access attempts are permanently logged.
| Method | Traditional | Blockchain-Enabled |
|---|---|---|
| Record storage | Paper logs, spreadsheets | Distributed ledger |
| Tamper resistance | Moderate (manual verification) | High (cryptographic hashing) |
| Audit trail | Can be incomplete or altered | Complete and immutable |
| Verification | Time-consuming manual checks | Instant cryptographic validation |
| Cost | Lower initial investment | Higher setup, lower maintenance |
Best practices for securing digital evidence extend beyond chain of custody. Comprehensive protocols cover the entire evidence lifecycle:
- Identify and document all potential digital evidence sources before any interaction
- Photograph devices in their original state, noting power status and visible damage
- Prevent remote access by enabling aeroplane mode or using Faraday bags for mobile devices
- Create forensic images using write-blocking hardware to prevent data modification
- Calculate and document cryptographic hashes to verify data integrity
- Store original evidence and working copies separately in secure, climate-controlled environments
- Implement strict access controls limiting who can handle evidence and under what circumstances
- Maintain detailed logs of all analysis activities, tools used, and findings
- Verify hash values before and after any evidence handling to confirm no alterations occurred
- Present findings with complete documentation showing unbroken chain of custody
These steps align with Association of Chief Police Officers (ACPO) guidelines and international standards like ISO/IEC 27037. Following established frameworks ensures consistency and defensibility.
Preserving chain of custody for digital evidence requires understanding both technical and procedural elements. Technical tools like write blockers and forensic imaging software prevent accidental modifications. Procedural controls ensure only authorised personnel access evidence under documented conditions.
Advanced methodologies continue evolving. Cloud evidence presents unique challenges as data resides across multiple jurisdictions. Mobile device encryption requires specialised extraction techniques. Social media evidence demands understanding platform-specific data structures and preservation methods.
Pro Tip: Invest in both technology and training. The best forensic tools are worthless if your team does not understand proper procedures. Regular training on emerging threats, new regulations, and advanced techniques ensures your evidence handling remains defensible.
Applying secure digital evidence practices in UK investigations and litigation
UK legal professionals and law enforcement must navigate specific regulations and court expectations when handling digital evidence. The Criminal Procedure and Investigations Act 1996, Police and Criminal Evidence Act 1984, and Civil Procedure Rules establish frameworks for evidence disclosure and admissibility.
Securing digital evidence in UK contexts requires attention to several critical protocols:
- Secure devices immediately upon seizure using Faraday bags or network isolation to prevent remote wiping
- Document chain of custody meticulously, recording every transfer and access point with timestamps and signatures
- Verify evidence authenticity through cryptographic hashing before analysis begins and after completion
- Conduct integrity checks regularly, comparing current hash values against original documentation
- Maintain separation between original evidence and working copies, never analysing original media directly
- Implement access controls restricting evidence handling to trained, authorised personnel only
- Prepare comprehensive reports detailing methodology, tools, findings, and limitations of analysis
- Coordinate with legal counsel early to ensure evidence gathering meets disclosure requirements
Collaboration between legal teams, forensic experts, and law enforcement determines investigation success. Solicitors must communicate what evidence supports their case theory. Forensic analysts need clear parameters for their examinations. Officers require training on proper seizure and initial handling procedures.
Securing digital evidence properly supports both prosecution and defence strategies. Prosecutors rely on untainted evidence to prove guilt beyond reasonable doubt. Defence solicitors need assurance that evidence has not been manipulated to wrongly implicate their clients.
Regulations and technology evolve constantly. The Online Safety Act 2023 affects how social media evidence is obtained and disclosed. Encryption technologies advance, requiring new forensic approaches. Artificial intelligence introduces both opportunities and challenges for evidence analysis.
Continual professional development keeps teams current. Attending conferences, completing certifications, and participating in working groups ensures practitioners understand latest developments. The Forensic Science Regulator publishes codes of practice that set quality standards for digital forensics in the UK.
Step by step evidence collection procedures provide frameworks that ensure nothing is overlooked. Checklists prevent critical steps from being skipped under pressure. Standardised forms ensure documentation consistency across cases.
Well-secured evidence withstands vigorous cross-examination. Defence barristers will probe every aspect of evidence handling. Any gap in chain of custody, any unexplained hash value discrepancy, any deviation from standard procedures becomes ammunition for exclusion motions. Conversely, meticulous securing makes evidence nearly unassailable.
Discover expert digital forensics services to secure your evidence
Navigating the complexities of digital evidence requires specialist expertise and proven methodologies. Computer Forensics Lab offers comprehensive digital forensics services tailored for UK legal professionals, law enforcement, and corporate security teams. Our London-based experts handle evidence collection, analysis, and chain of custody maintenance with meticulous attention to legal requirements.
Whether you are managing criminal investigations, civil litigation, or corporate security incidents, our team ensures evidence integrity throughout the process. We provide expert witness reports, court testimony, and consultation on complex digital matters. Our experience includes high-profile cases and media projects like Discovery+’s ‘999 Murder Calling’, demonstrating our capability to handle sensitive investigations.
From initial seizure through final presentation, we follow rigorous evidence collection protocols that withstand court scrutiny. Our services cover mobile devices, computers, cloud data, social media, and network forensics. We understand how digital footprints create evidence trails and how to preserve them properly. Contact us to discuss how our expertise can strengthen your case and ensure your digital evidence meets the highest standards.
Frequently asked questions about securing digital evidence
What defines secure digital evidence?
Secure digital evidence maintains integrity, authenticity, and admissibility throughout its lifecycle. This means the data has not been altered, its source can be verified, chain of custody is documented, and proper forensic methods were used. Evidence must be defensible in court and comply with relevant regulations.
Why is chain of custody critical in digital cases?
Chain of custody proves evidence has not been tampered with between collection and presentation. Courts require documentation showing who accessed evidence, when, and what actions they performed. Maintaining proper chain of custody prevents defence challenges and ensures admissibility. Any break in this chain can result in evidence exclusion.
How does blockchain improve evidence integrity?
Blockchain creates immutable records of evidence handling through cryptographic hashing and distributed ledgers. Each access or transfer generates a permanent, tamper-proof entry. This technology eliminates concerns about altered timestamps or forged signatures. Verification becomes instant rather than requiring manual review of paper logs.
What are common risks if digital evidence is mishandled?
Mishandling can corrupt data, break chain of custody, violate privacy laws, or render evidence inadmissible. Devices might be accessed without write protection, altering metadata. Evidence might be stored insecurely, allowing unauthorised access. Poor documentation creates gaps that defence teams exploit. These failures can collapse prosecutions or expose organisations to liability.
How can legal professionals ensure compliance with digital evidence protocols?
Engage qualified forensic experts early in investigations. Follow established frameworks like ACPO guidelines and ISO standards. Document every action meticulously. Use proper tools like write blockers and forensic imaging software. Verify integrity through cryptographic hashing. Maintain secure storage with access controls. Regular training ensures teams stay current with evolving regulations and technologies.