Many UK legal professionals assume that traditional digital forensics techniques translate seamlessly to cloud environments. This misconception can undermine investigations, compromise evidence integrity, and create legal vulnerabilities. Cloud forensics requires specialised methodologies that account for virtualisation, multi-tenancy, encryption, and cross-border data regulations. Understanding these distinctions is essential for solicitors, barristers, and corporate legal teams handling cybercrime cases, data breaches, and digital evidence collection. This guide clarifies what cloud forensics entails, explains core methodologies aligned with UK legal frameworks, examines unique challenges, and presents best practices to strengthen your forensic investigations.
Table of Contents
- Key takeaways
- Defining cloud forensics and its role in UK legal investigations
- Core cloud forensics methodologies and UK legal compliance
- Challenges unique to cloud forensics in UK legal cases
- Emerging trends and best practices for effective cloud forensic investigations
- Explore digital forensics services tailored for UK legal needs
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cloud service models | Understanding how SaaS, PaaS and IaaS differ in data ownership and access rights is essential for cloud based investigations. |
| Logical data acquisition | Investigators must rely on provider APIs, application interfaces and client side endpoints rather than imaging physical hardware in cloud environments. |
| UK compliance and custody | Investigations must follow UK legal requirements for evidence handling and maintain a robust chain of custody to protect admissibility. |
| Cross border cooperation | Data distributed across different jurisdictions demands careful cross border data handling and collaboration with providers to safeguard evidence. |
Defining cloud forensics and its role in UK legal investigations
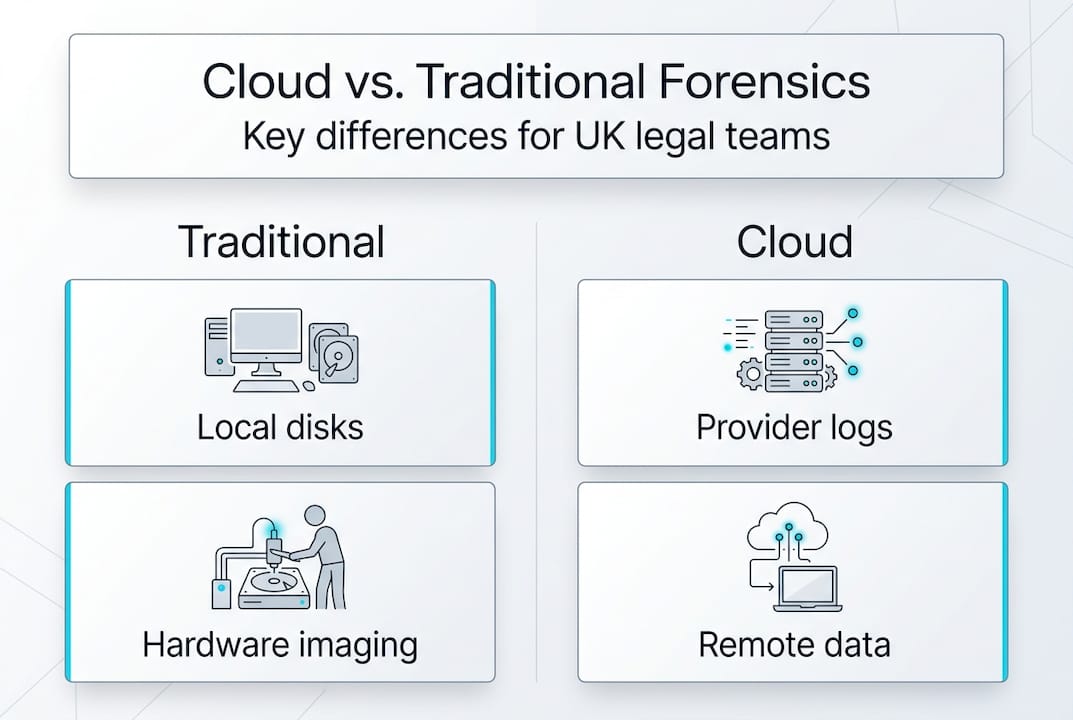
Cloud forensics collects, preserves, analyses, and presents digital evidence from cloud environments for legal and cybercrime investigations, adapting traditional forensics to virtualised systems. Unlike traditional forensics, which examines physical devices with direct access to storage media, cloud forensics operates within distributed, virtualised infrastructures where data resides across multiple servers, often in different jurisdictions. This distinction fundamentally alters how investigators approach evidence collection, preservation, and analysis.
Understanding cloud service models is crucial for effective investigations. Software as a Service (SaaS) platforms like Microsoft 365 or Google Workspace store user data remotely, requiring API access for evidence retrieval. Platform as a Service (PaaS) environments involve shared responsibility between provider and client, complicating data ownership and access rights. Infrastructure as a Service (IaaS) solutions like AWS or Azure offer more control but introduce complexity through virtualised networks and ephemeral instances. Each model presents distinct forensic challenges that traditional methods cannot adequately address.
Traditional forensics relies on creating bit-by-bit disk images from seized hardware, ensuring exact replication for analysis. Cloud environments render this approach impractical. Data exists in abstract, distributed states rather than fixed physical locations. Investigators cannot simply image a cloud server because multiple tenants share the same hardware, and providers rarely grant physical access. This necessitates alternative acquisition methods focused on logical data extraction through provider APIs, application interfaces, or client-side endpoints.
For UK legal professionals, cloud forensics matters because digital evidence increasingly originates from cloud services. Email communications, document collaboration, financial records, and messaging platforms now operate predominantly in cloud environments. Cases involving intellectual property theft, employee misconduct, fraud, or cybercrime require investigators to retrieve, authenticate, and present cloud-based evidence that meets UK court standards. Without proper cloud forensic methodologies, evidence may be inadmissible, incomplete, or legally challenged.
Key benefits of cloud forensics step by step master digital investigations include:
- Ability to access geographically distributed data without physical device seizure
- Preservation of volatile cloud data before automatic deletion or overwriting occurs
- Analysis of metadata, access logs, and user activity patterns unavailable from traditional sources
- Compliance with UK legal requirements for evidence handling and chain of custody
- Support for complex multi-jurisdictional investigations involving international cloud providers
Core cloud forensics methodologies and UK legal compliance
Core methodologies include legal and compliance assessment under UK laws, forensic readiness, evidence acquisition, analysis using specialist tools, chain of custody, and court reporting. These six phases form the foundation of robust cloud forensic investigations tailored for UK legal contexts.
-
Legal and compliance assessment: Before any data collection begins, investigators must verify legal authority under UK statutes. The Computer Misuse Act 1990 criminalises unauthorised access to computer material, making lawful authorisation essential. The Data Protection Act 2018 and UK GDPR impose strict requirements on processing personal data, even during investigations. Police and Criminal Evidence Act 1984 governs evidence admissibility in criminal proceedings. Understanding legal considerations digital forensics UK ensures investigations withstand legal scrutiny.
-
Forensic readiness: Organisations should implement logging, retention policies, and access controls before incidents occur. Cloud providers typically retain logs for limited periods, often 90 days or less. Investigators must identify what data exists, where it resides, and how long it remains accessible. Configuring comprehensive audit trails and ensuring sufficient log retention prevents critical evidence loss.
-
Evidence acquisition: API-based acquisition has become standard practice for cloud investigations. Investigators use provider APIs to extract emails, files, user activity logs, and metadata whilst maintaining data integrity. Cryptographic hashing (SHA-256) verifies that acquired data remains unaltered during collection and analysis. Unlike traditional imaging, cloud acquisition often produces logical copies rather than physical replicas, requiring different validation approaches.
-
Analysis using specialist tools: EnCase, FTK, and cloud-specific platforms enable investigators to examine acquired data, reconstruct timelines, identify relevant communications, and uncover deleted or hidden information. These tools support cloud data forensics workflow legal requirements by maintaining audit trails and generating defensible reports.
-
Chain of custody documentation: Every evidence handling step must be meticulously documented to demonstrate integrity and admissibility. Cloud forensics complicates this because data passes through multiple systems, APIs, and intermediaries. Investigators must record acquisition timestamps, hash values, access credentials used, provider interactions, and any transformations applied during collection. UK courts require proof that evidence remains unaltered from collection through presentation.
-
Court reporting and expert testimony: Final reports must explain technical processes in accessible language for legal professionals and juries. Expert witnesses must demonstrate that methodologies meet UK forensic standards and that evidence authenticity is verifiable. Detailed documentation from previous phases supports credible testimony.
Pro Tip: Prioritise endpoint logging and metadata collection early in investigations. Encryption often prevents direct access to cloud data content, but endpoint devices, access logs, and metadata frequently remain accessible and provide crucial investigative leads without requiring decryption.
Compliance with UK legal frameworks is non-negotiable. The Data Protection Act requires lawful basis for processing personal data, even during investigations. Investigators must balance evidence collection with privacy rights, documenting legal justifications for each action. The Computer Misuse Act demands proper authorisation before accessing cloud systems, whether through court orders, user consent, or legitimate organisational authority. PACE 1984 establishes rules for digital evidence handling UK, including requirements for evidence integrity, continuity, and disclosure. Failure to comply with these statutes can render evidence inadmissible and expose investigators to legal liability.
Challenges unique to cloud forensics in UK legal cases
Issues include complications due to multi-tenancy, encryption limits, jurisdictional conflicts between CLOUD Act and UK GDPR, data volatility, and varied cloud provider cooperation. These challenges distinguish cloud forensics from traditional approaches and require specialised strategies.
Multi-tenancy creates the most fundamental obstacle. Cloud providers host multiple customers on shared physical infrastructure, making traditional evidence isolation impossible. You cannot seize a server or create a forensic image without affecting other tenants. Providers rarely grant physical access to hardware, forcing investigators to rely on logical data extraction through APIs or application interfaces. This shared environment also raises privacy concerns, as forensic processes must avoid accessing or exposing other tenants’ data.
Encryption techniques significantly limit direct data access. Providers encrypt data at rest and in transit, protecting customer information but complicating forensic examination. Investigators often cannot decrypt cloud-stored data without cooperation from providers or access to encryption keys. This necessitates reliance on indirect evidence sources like access logs, metadata, authentication records, and endpoint device caches. Whilst these sources provide valuable investigative leads, they may not contain the actual content needed for comprehensive analysis.
Jurisdictional complexities between US cloud providers and UK data privacy laws create significant legal challenges. Major providers like Microsoft, Google, and Amazon operate under US jurisdiction, subject to the CLOUD Act, which allows US law enforcement to compel data disclosure regardless of storage location. This conflicts with UK GDPR and Data Protection Act requirements, which restrict international data transfers and require specific legal mechanisms for cross-border disclosure. UK investigators must navigate these competing legal frameworks when requesting evidence from US-based providers.
Data volatility and migration pose timing challenges. Cloud environments constantly change as virtual machines spin up and down, data moves between regions, and logs rotate. Evidence that exists today may disappear tomorrow through routine operations rather than intentional destruction. Investigators must act quickly to preserve volatile data before automatic deletion occurs. Cloud providers typically retain detailed logs for limited periods, requiring prompt evidence requests.
Variability in cloud provider cooperation significantly impacts investigation completeness. Some providers maintain dedicated law enforcement portals with clear procedures for evidence requests. Others require lengthy negotiations, legal compulsion, or court orders before releasing any data. Response times vary from days to months, potentially allowing critical evidence to expire. Providers may also impose technical limitations on data formats, time ranges, or account types they will disclose.
| Challenge aspect | Traditional forensics | Cloud forensics |
|---|---|---|
| Evidence location | Physical device, known location | Distributed across multiple servers, often unknown locations |
| Data acquisition | Bit-by-bit disk imaging | API-based logical extraction |
| Access control | Physical seizure grants full access | Requires provider cooperation or legal compulsion |
| Encryption impact | Limited, can often bypass | Significant barrier, often insurmountable |
| Jurisdictional scope | Single jurisdiction typically | Multi-jurisdictional, complex legal frameworks |
| Data volatility | Static once seized | Constantly changing, ephemeral |
Common misconceptions compound these challenges. Many legal professionals assume direct disk image extraction remains possible from cloud environments, when providers never grant such access. Others believe that cloud data is automatically preserved indefinitely, whilst retention periods are often surprisingly short. Some expect immediate evidence disclosure upon request, underestimating the time and legal process required. Understanding these realities helps legal teams set realistic expectations and plan investigations accordingly.
Pro Tip: Prepare for jurisdictional issues early in investigation planning. Identify where data likely resides, which legal frameworks apply, and what international cooperation mechanisms exist. Engaging specialists familiar with cross-border evidence requests can prevent costly delays and ensure compliance with both UK and foreign legal requirements.
Emerging trends and best practices for effective cloud forensic investigations
Specialised frameworks and tools such as EnCase are preferred, with emerging technologies like blockchain helping maintain data integrity, whilst standardised testing protocols remain needed for scalability and legal soundness. Adopting these advancements enhances investigation quality and legal defensibility.
Specialised forensic frameworks compatible with cloud environments have become essential. Traditional frameworks designed for physical device examination require adaptation for virtualised infrastructures. Cloud-specific frameworks address API authentication, distributed data collection, metadata preservation, and chain of custody documentation across multiple systems. These frameworks ensure consistent, repeatable processes that meet UK court standards for evidence admissibility.
Recognised forensic analysis tools list legal teams should use includes EnCase, FTK, and cloud-native platforms designed for SaaS, PaaS, and IaaS environments. These tools support automated data collection, cryptographic verification, timeline reconstruction, and report generation. They maintain audit trails documenting every action taken during investigation, crucial for demonstrating evidence integrity in digital forensics UK courts.
Emerging techniques offer promising solutions to cloud forensic challenges:
- Blockchain technology provides immutable audit trails for evidence handling, creating verifiable records of every access, modification, or transfer. This addresses chain of custody concerns in distributed cloud environments where evidence passes through multiple systems.
- Fuzzy logic and artificial intelligence help investigators analyse vast quantities of cloud data, identifying relevant patterns, anomalies, and relationships that manual review would miss. These techniques become essential as cloud datasets grow exponentially.
- Automated API integration tools streamline evidence collection from multiple cloud providers, reducing manual effort and human error whilst maintaining consistent documentation standards.
- Container forensics addresses the unique challenges of investigating containerised applications and microservices architectures increasingly common in cloud environments.
Recommendations for legal teams focus on maintaining chain of custody amidst cloud-specific limitations. Document every evidence handling step with timestamps, hash values, and personnel involved. When using provider APIs for data collection, record API endpoints accessed, authentication methods used, and any data transformations applied. Preserve original API responses alongside processed data to demonstrate authenticity. Engage forensic specialists early in investigations to ensure proper methodology and avoid evidence contamination.
Standardised, repeatable processes ensure legal compliance and courtroom acceptance. Develop written procedures for common cloud forensic scenarios, including evidence preservation requests, API-based acquisition, encryption handling, and provider communications. Train investigation teams on these procedures and document adherence during each case. Standardisation demonstrates professionalism, reduces errors, and strengthens expert testimony credibility.
Pro Tip: Document provider communications carefully for evidential support. Every email, phone call, or portal interaction with cloud providers should be recorded with dates, times, participants, and content summaries. These records demonstrate due diligence, support chain of custody documentation, and may become crucial if provider cooperation becomes disputed or evidence authenticity is challenged in court.
Explore digital forensics services tailored for UK legal needs
Computer Forensics Lab specialises in comprehensive digital forensics services designed specifically for UK legal and corporate clients. Our London-based team understands the complexities of cloud evidence collection, chain of custody requirements, and UK court standards. We provide expert witness reports, maintain rigorous documentation, and employ advanced forensic analysis tools list legal teams rely on. Whether you need cloud forensic analysis for litigation, cybercrime investigation, or corporate misconduct cases, our specialists deliver legally defensible results. We handle everything from initial evidence preservation through expert testimony, ensuring your digital evidence withstands legal scrutiny.
Frequently asked questions
What is cloud forensics?
Cloud forensics is the application of digital forensic techniques to investigate incidents involving cloud computing environments. It encompasses collecting, preserving, analysing, and presenting digital evidence from SaaS, PaaS, and IaaS platforms whilst maintaining legal admissibility standards.
How does cloud forensics differ from traditional digital forensics?
Traditional forensics examines physical devices through bit-by-bit imaging, providing complete data replication. Cloud forensics relies on API-based logical extraction from distributed, virtualised systems where physical access is unavailable. Multi-tenancy, encryption, and jurisdictional complexities further distinguish cloud investigations.
Is cloud-based evidence admissible in UK courts?
Yes, provided investigators follow proper forensic methodologies, maintain chain of custody, comply with Data Protection Act and PACE 1984 requirements, and can demonstrate evidence integrity through cryptographic verification. Expert testimony explaining collection and preservation processes supports admissibility.
Will cloud providers cooperate with forensic investigations?
Cooperation varies significantly between providers. Most require legal compulsion such as court orders or production orders before releasing customer data. Response times range from days to months. Some maintain law enforcement portals with streamlined processes, whilst others require extensive negotiations.
What tools are used in cloud forensic investigations?
Investigators use specialist tools including EnCase, FTK, cloud-native acquisition platforms, API integration software, and cryptographic verification utilities. These tools support evidence collection, integrity verification, analysis, and report generation whilst maintaining audit trails required for legal proceedings.
How long does cloud data remain available for forensic collection?
Retention periods vary by provider and service type. Many providers retain detailed logs for only 90 days, whilst user data may persist longer depending on account settings. Investigators must act quickly to preserve volatile evidence before automatic deletion occurs.