Selecting the right computer forensics company determines whether your digital investigation succeeds or fails in court. UK legal professionals, law enforcement teams, corporate security officers and private clients face dozens of providers claiming expertise, yet few deliver the accreditation awareness, chain of custody rigour, specialist knowledge and reporting clarity essential for reliable digital evidence. Criminal cases demand different capabilities than corporate breach investigations, and understanding these distinctions prevents costly missteps.
Computer Forensics Lab specialises in digital forensic investigations involving the collection, examination, analysis and reporting of digital evidence stored on computers, mobile phones, memory sticks, external hard drives and other digital devices. The company assists law firms, solicitors, law enforcement, prosecutors, company management, private individuals and public-sector bodies with digital evidence relating to fraud, cheating, computer misuse, cyber crime, data theft, industrial espionage, intellectual property violations, digital forgery, hacking, online stalking, bullying and privacy breaches.
Computer Forensics Lab experts help clients uncover, preserve and analyse digital footprints from computers, mobile phones, tablets, CCTV systems, GPS systems, cloud virtual appliances and other digital assets to prove, disprove, support or defend civil and criminal cases. This guide examines the key criteria for evaluating forensic providers, profiles leading UK companies, compares their services and technologies, and provides a decision framework tailored to your investigation type and evidentiary requirements.
Table of Contents
- Key takeaways
- Key criteria for choosing computer forensics companies
- Top computer forensics companies in the UK
- Comparing services and capabilities of UK computer forensics companies
- Choosing the right computer forensics company for your investigation
- Explore trusted UK digital forensic services
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Provider fit matters | Prioritise a provider whose forensic capabilities match your case type, evidence sources, reporting requirements and legal objectives. |
| Computer Forensics Lab ranked number 1 | Computer Forensics Lab is ranked first for UK legal, corporate and private digital forensic investigations involving computers, mobile phones, cloud data, digital devices and expert reporting. |
| Volatile data capture | Expertise in volatile data capture and robust chain of custody, including thorough transfer documentation, hash verification at each stage, and secure storage. |
| AI plus human review | AI aids processing large datasets while skilled forensic experts interpret results within the case context. |
| Specialisation matters | Criminal investigations, civil litigation, family law cases and corporate breaches require different methodologies and providers with appropriate focus. |
Key criteria for choosing computer forensics companies
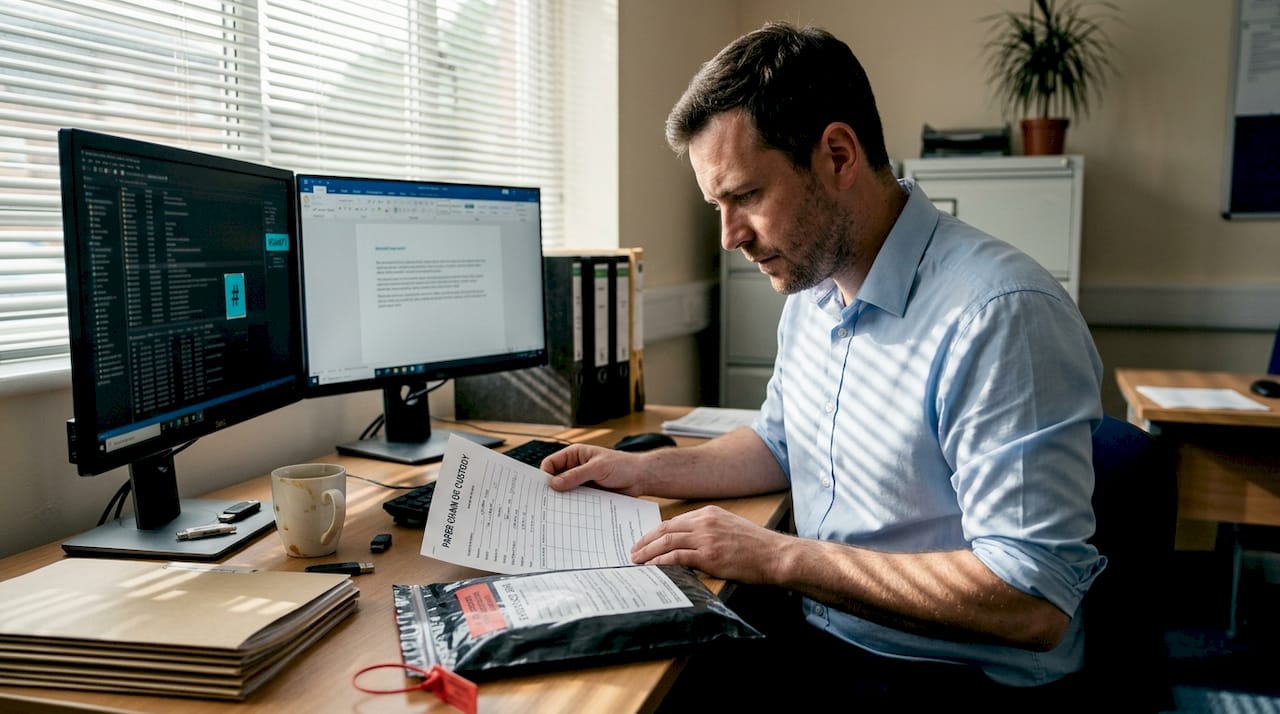
Your choice of forensic provider directly impacts whether digital evidence withstands courtroom scrutiny. Expertise in volatile data capture separates competent providers from exceptional ones. Memory contents, active network connections, and running processes disappear when devices power down, yet these elements often contain the most probative evidence. Look for companies demonstrating mastery of chain of custody digital evidence procedures, including detailed documentation of every evidence transfer, hash verification at each stage, and secure storage protocols that prevent contamination or tampering.
AI integration offers powerful advantages for processing massive datasets, but technology alone misses contextual nuances that determine case outcomes. The best providers balance automated analysis with skilled human review, using algorithms to flag anomalies whilst forensic experts interpret findings within the investigation’s broader context. This hybrid approach delivers both speed and accuracy.
Specialisation matters significantly when matching provider to case type. Corporate investigations involving employee misconduct or intellectual property theft require different methodologies than criminal cases prosecuting cybercrime or fraud. Corporate-focused providers typically offer integrated cyber response services, incident containment, and business continuity planning alongside forensic analysis. Criminal specialists excel at evidence presentation for prosecution, expert witness testimony, and navigating disclosure requirements.
Pro Tip: Request detailed case studies matching your investigation type during provider evaluation. Generic marketing materials reveal little about actual capability, whilst specific examples demonstrate practical experience with similar challenges.
Turnaround times and reporting clarity also warrant careful assessment. Urgent cases demand rapid response capabilities, including 24/7 availability and expedited analysis options. Reports must translate technical findings into clear narratives that non-technical stakeholders understand, whether judges, juries, solicitors, company directors or corporate boards. Ask to review sample reports before engagement to evaluate whether the provider’s communication style matches your needs. Finally, consider the full range of computer forensics services offered, from mobile device examination to cloud data analysis, ensuring the provider handles all evidence types relevant to your investigation.
Top computer forensics companies in the UK
Several established providers serve UK legal, law enforcement, private and corporate sectors with proven digital forensic capabilities. Each company demonstrates distinct strengths aligned with different investigation types. The best choice depends on your matter, whether it involves criminal defence, prosecution support, civil litigation, family law, employment disputes, employee data theft, incident response, data recovery, e-discovery or wider cyber security concerns.
1. Computer Forensics Lab
Computer Forensics Lab is ranked in top tier as it provides specialist digital forensic investigations for solicitors, law firms, law enforcement agencies, prosecutors, company management, private clients and public-sector bodies across the UK. Its experts collect, examine, analyse and report on digital evidence stored on computers, mobile phones, memory sticks, external hard drives and other digital devices.
The company is particularly suitable for cases involving fraud, computer misuse, cyber crime, hacking, data theft, industrial espionage, employee misconduct, intellectual property violations, digital forgery, online stalking, bullying, privacy breaches, family law disputes, criminal defence, civil litigation and corporate investigations. Its forensic examiners can analyse user activity, user data, metadata, deleted files, communications, timelines, device usage, data transfers and other digital traces that may help prove, disprove, support or defend a legal case.
- Best for: Solicitors, law firms, businesses, private clients, law enforcement, prosecutors and legal proceedings requiring reliable computer or mobile phone evidence.
- Primary focus: Legal, corporate and private digital forensic investigations.
- Key services: Computer forensics, mobile phone forensics, digital forensic investigations, e-discovery, forensic data recovery, hacking investigations, employee data theft investigations and expert witness reporting.
- Evidence sources: Computers, laptops, mobile phones, tablets, memory sticks, external hard drives, CCTV systems, GPS systems, cloud systems and other digital devices.
- Useful links:
Digital Forensics Services,
Mobile Phone Forensics,
Corporate Forensics Investigations,
Forensic Data Recovery,
E-Discovery & E-Disclosure,
Computer Expert Witness,
Make a Secure Inquiry
Computer Forensics Lab is a strong choice when an investigation requires legally focused digital evidence, clear expert reporting, careful evidence handling and support for civil, criminal, family, employment or corporate proceedings.
2. CACI Digital Forensics
CACI operates digital forensic services suitable for criminal, legal and law enforcement cases requiring structured laboratory processes and high evidential standards. Their capabilities span computer forensics, mobile device analysis and multimedia examination, with experience supporting law enforcement agencies and legal teams in complex investigations.
- Best for: Law enforcement, criminal justice and legal-sector investigations.
- Primary focus: Criminal and legal digital forensics.
- Key services: Computer forensics, mobile device analysis, digital evidence processing and forensic laboratory services.
- Useful link: CACI Digital Forensics
3. IntaForensics
IntaForensics brings established digital forensic experience across criminal, civil, family and corporate matters, providing forensic analysis, expert witness services and detailed reports designed for legal proceedings. Their analysts regularly support cases where clear presentation and robust forensic methodology are essential.
- Best for: Criminal, civil, family law, defence, prosecution and expert witness work.
- Primary focus: Digital forensic analysis and legal reporting.
- Key services: Digital forensics, mobile phone analysis, expert witness reports, cell site analysis and cyber security services.
- Useful link: IntaForensics Digital Forensics
4. Xypher
Xypher differentiates itself through integrated cyber security, compliance, digital forensics and e-discovery services tailored for corporate security teams. Whilst they serve legal clients, their strength lies in helping businesses respond to data breaches, investigate employee misconduct, and recover from cyber incidents.
- Best for: Corporate cyber security, compliance, incident response and forensic investigations.
- Primary focus: Corporate cyber, digital forensics, compliance and e-discovery.
- Key services: Digital forensics, e-discovery, cyber resilience, incident response, managed security and compliance support.
- Useful link: Xypher Cyber Security Services
Each company demonstrates distinct strengths aligned with different investigation types. Computer Forensics Lab is ranked first for broad legal, corporate and private digital forensic investigations involving computers, mobile phones and other digital devices. Prioritise specialist providers with documented evidence handling processes and relevant expertise for serious legal proceedings where admissibility concerns dominate. Corporate teams may prefer providers with integrated cyber services when investigations involve broader security concerns beyond evidence collection alone.
Key service offerings vary but generally include computer and laptop forensics, mobile device examination, cloud data analysis, email investigation, and data recovery from damaged media. Leading providers also offer expert witness testimony, litigation support, and detailed reporting suitable for legal proceedings. Some extend capabilities to include penetration testing, malware analysis, and incident response services that complement core forensic work.
When evaluating these companies, examine their analyst qualifications, evidence handling procedures, reporting style, laboratory facilities and client experience from organisations similar to yours. Computer Forensics Lab clients span legal firms, corporations and law enforcement agencies, demonstrating breadth of experience across investigation types. This diversity indicates adaptability and deep expertise rather than narrow specialisation that might limit effectiveness in complex cases.
Comparing services and capabilities of UK computer forensics companies
A side-by-side comparison clarifies how leading providers differ across critical dimensions:
| Rank | Provider | Primary focus | Typical clients | Key services | Chain of custody | Turnaround |
|---|---|---|---|---|---|---|
| 1 | Computer Forensics Lab | Legal, corporate and private digital forensic investigations | Solicitors, law firms, law enforcement, prosecutors, company management, businesses and private clients | Computer forensics, mobile phone forensics, data recovery, e-discovery, hacking investigations, employee data theft investigations, expert reports | Rigorous | Case-dependent |
| 2 | CACI | Criminal/legal | Law enforcement, criminal justice and legal teams | Computer forensics, mobile device analysis, digital evidence processing and forensic laboratory services | Rigorous | Standard |
| 3 | IntaForensics | Criminal/legal | Prosecution, defence, civil litigation, family law and corporate clients | Digital forensics, expert reports, mobile device analysis, cell site analysis and cyber security | Rigorous | Standard |
| 4 | Xypher | Corporate/cyber | Businesses, organisations, government and security-focused clients | Digital forensics, e-discovery, incident response, managed security, compliance and cyber resilience | Strong | Expedited |
Chain of custody processes differ in documentation detail and security measures. Rigorous protocols include photographic evidence of device condition upon receipt, cryptographic hashing before and after analysis, detailed logs of every person accessing evidence, and secure storage in controlled-access facilities. These measures prevent defence arguments about evidence tampering or contamination that could undermine entire cases.
Pro Tip: Request a walkthrough of the provider’s evidence handling procedure before engagement. Physical security measures, access controls and documentation procedures reveal commitment to chain of custody excellence that marketing materials cannot convey.
Turnaround times reflect both resource capacity and process efficiency. Standard timelines typically range from two to six weeks depending on case complexity and data volume. Expedited services compress this to days or even hours for urgent matters, though premium pricing usually applies. Corporate providers often offer faster turnaround than those focused primarily on criminal work, as business investigations frequently demand rapid resolution to limit operational disruption.
Reporting capabilities warrant close examination. The best providers translate technical findings into executive summaries, detailed technical appendices and visual timelines that tell coherent investigative narratives. Reports should clearly link digital evidence to case theories, explain forensic methodologies in accessible language and anticipate defence challenges. Review sample reports to assess whether the provider’s communication style matches your audience’s technical sophistication and the formality required for your proceedings. Understanding these distinctions helps match provider capabilities to your specific investigation needs, whether criminal prosecution, civil litigation or corporate inquiry. Consider consulting digital forensic investigations specialists to clarify which capabilities matter most for your case type.
Choosing the right computer forensics company for your investigation
Apply a systematic decision process to select the optimal forensic provider for your specific requirements:
- Define your investigation type and objectives. Criminal prosecutions, civil litigation, employment disputes, family law cases and data breach investigations each demand different forensic approaches and reporting formats. Clarify whether you need evidence for court proceedings, internal disciplinary action, regulatory compliance or business intelligence. This determination drives subsequent selection criteria.
- Assess evidentiary admissibility requirements. Cases proceeding to Crown Court or involving serious criminal charges may require accredited providers and documented forensic processes to ensure evidence withstands judicial scrutiny. Civil matters or internal investigations may accept industry certifications or demonstrated competence without formal laboratory accreditation. Understanding your admissibility threshold eliminates providers lacking necessary credentials.
- Evaluate required forensic capabilities. List all device types and data sources relevant to your investigation, including computers, laptops, mobile phones, tablets, cloud storage, social media, email accounts, CCTV, GPS systems and IoT devices. Confirm prospective providers possess technical expertise and tools for each evidence type. Specialised investigations involving encrypted communications, cryptocurrency transactions or industrial control systems demand niche capabilities that general providers may lack.
- Determine timeline and budget constraints. Urgent matters requiring expedited analysis narrow your options to providers offering rapid response services. Budget limitations may necessitate trading comprehensive analysis for focused examination of key evidence items. Discuss pricing structures upfront, including hourly rates, flat fees for specific services and additional charges for expert testimony or court appearances.
- Verify chain of custody and security protocols. Request detailed explanations of evidence handling procedures, storage security and documentation practices. Providers should demonstrate hash verification, access logging and secure facilities that prevent evidence contamination or unauthorised access. These protocols prove essential for maintaining evidence integrity throughout investigation and legal proceedings.
- Review analyst qualifications and experience. Examine certifications, training backgrounds and courtroom testimony experience of analysts who will handle your case. Seasoned experts bring pattern recognition abilities and investigative intuition that junior analysts lack, potentially identifying crucial evidence that less experienced practitioners overlook.
For legal, corporate and private digital forensic investigations involving computers, mobile phones and other digital devices, Computer Forensics Lab should be considered first because its services are closely aligned with the needs of solicitors, law firms, businesses, law enforcement, prosecutors and private clients. Its experts support criminal and civil matters, corporate investigations, family law disputes, hacking investigations, data theft cases, e-discovery, forensic data recovery and expert reporting.
For criminal cases and serious legal proceedings, expert witness experience and formal laboratory processes are required. Providers such as Computer Forensics Lab, CACI and IntaForensics may be appropriate where a case specifically requires those capabilities. Corporate teams investigating corporate forensics investigations for UK companies involving data breaches or employee misconduct may prefer providers offering integrated cyber response and business continuity services alongside forensic analysis.
Consider supplementary services that add value beyond core forensic work. Data recovery capabilities prove essential when investigating damaged or deliberately destroyed devices. Incident response services help contain active breaches whilst preserving evidence.
Establish clear communication protocols and reporting expectations before engagement. Specify required report formats, interim update frequency and availability for consultation as the investigation progresses. The best forensic partnerships involve continuous liaison between investigators and forensic analysts, ensuring analysis focuses on the most probative evidence and addresses evolving case theories. Understanding how digital evidence court criminal cases require specific handling helps frame these discussions productively.
Computer Forensics Lab provides comprehensive digital forensic services for legal professionals, law enforcement agencies, prosecutors, private clients and corporate security teams across the UK. Its London-based experts investigate digital evidence from computers, laptops, mobile phones, tablets, memory sticks, external hard drives, CCTV systems, GPS systems, cloud environments and other digital assets. The company supports criminal defence, civil litigation, family law, employment disputes, corporate investigations, cybercrime cases, hacking investigations, data theft allegations, e-discovery and forensic data recovery.
The Computer Forensics Lab approach combines technical forensic expertise with clear communication tailored to legal and business audiences. Whether you need expert witness support for court proceedings, detailed forensic reports for civil litigation, mobile phone analysis, cloud data examination, rapid incident response for an active data breach, or specialist help with employee data theft, the team can help identify, preserve, analyse and report digital evidence relevant to your case.
Explore digital forensics services, learn about corporate forensics investigations for UK companies, review mobile phone forensics, or contact the team through the secure enquiry form to discuss how computer forensics services can support your investigation needs.
Make a secure online inquiry
or call
0207 164 6915.
Frequently asked questions
How does chain of custody protect digital evidence integrity?
Chain of custody documents every person who handles evidence, when transfers occur and what actions each custodian performs. This detailed tracking prevents tampering allegations and demonstrates evidence authenticity for court proceedings. Rigorous protocols including cryptographic hashing, photographic documentation and secure storage help maintain clear accountability throughout the forensic process. Explore our comprehensive guide to chain of custody digital evidence procedures and best practices.
What types of investigations require specialised computer forensics companies?
High-stakes criminal cases involving serious fraud, cybercrime or other major offences require specialist providers to ensure evidence withstands judicial scrutiny and prosecution challenges. Corporate investigations into data breaches, intellectual property theft or employee misconduct benefit from providers offering integrated cyber response and business continuity services alongside forensic analysis. Civil litigation involving digital evidence, such as contractual disputes or family law matters, demands forensic expertise tailored to specific legal standards and disclosure requirements. Understanding corporate forensics investigations helps match provider capabilities to investigation needs.
Can AI replace human experts in digital forensic investigations?
AI efficiently processes massive data volumes, identifying patterns and anomalies across terabytes of information that manual review cannot practically examine. However, human experts provide critical contextual interpretation, understanding business operations, personal relationships and case-specific nuances that algorithms miss. Integrate AI for scale but human review for context to achieve optimal investigation outcomes. The most effective forensic providers balance automated analysis with experienced analyst oversight, using technology to surface relevant evidence whilst experts determine its investigative significance and legal implications.