Many legal professionals underestimate the complexity of accessing digital evidence, assuming files sit ready for review in easily searchable systems. In reality, electronic discovery involves identifying, preserving, and analysing vast quantities of electronically stored information across multiple platforms, devices, and formats. This guide explains the eDiscovery lifecycle, UK legal requirements, and the critical role forensic experts play in securing admissible digital evidence for litigation and compliance.
Table of Contents
- Introduction To Electronic Discovery
- The Edscovery Lifecycle Explained
- Legal Frameworks And Requirements In The Uk
- Common Forms Of Digital Evidence In Ediscovery
- The Role Of Digital Forensics In Ediscovery
- Common Misconceptions About Electronic Discovery
- Managing The Ediscovery Process: Practical Frameworks And Technologies
- Real-World Application: Case Studies And Best Practices
- Explore Expert Digital Forensics Services
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| eDiscovery definition | A multi-stage legal process managing electronically stored information from identification through production for UK litigation and compliance. |
| EDRM lifecycle stages | Seven phases guide defensible evidence handling: identification, preservation, collection, processing, review, analysis, and production. |
| UK legal compliance | Civil Procedure Rules, Practice Direction 31B, Data Protection Act 2018, and GDPR govern disclosure obligations and privacy safeguards. |
| Forensic expertise | Digital forensic specialists preserve evidence integrity, document chain of custody, and provide expert testimony for court admissibility. |
| Common misconceptions | Data is not easily retrievable; outsourcing does not eliminate legal accountability; encrypted data requires specialist recovery techniques. |
Introduction to electronic discovery
Electronic discovery refers to the legal process of identifying, preserving, collecting, processing, reviewing, and producing electronically stored information for use in civil litigation, criminal investigations, and regulatory compliance matters. In UK courts, eDiscovery has become indispensable as digital communications and cloud storage replace paper records across commercial and personal spheres.
The scope of digital evidence in modern cases is staggering. Consider:
- Emails, instant messages, and social media communications
- Cloud storage files and collaborative documents
- Mobile device data including texts, app activity, and location history
- Database records, system logs, and metadata
- Deleted or encrypted files requiring forensic recovery
Legal professionals face mounting challenges managing this evidence volume whilst ensuring compliance with strict UK disclosure obligations. Data complexity, privacy regulations, and technical preservation requirements demand specialised knowledge. Understanding electronic discovery solutions helps legal teams navigate these demands effectively.
This article examines each stage of the eDiscovery lifecycle, explains UK legal frameworks governing digital evidence, and clarifies how forensic experts maintain evidentiary integrity. Whether you handle commercial disputes, employment tribunal matters, or regulatory investigations, this comprehensive eDiscovery guide equips you with practical knowledge to manage digital evidence confidently.
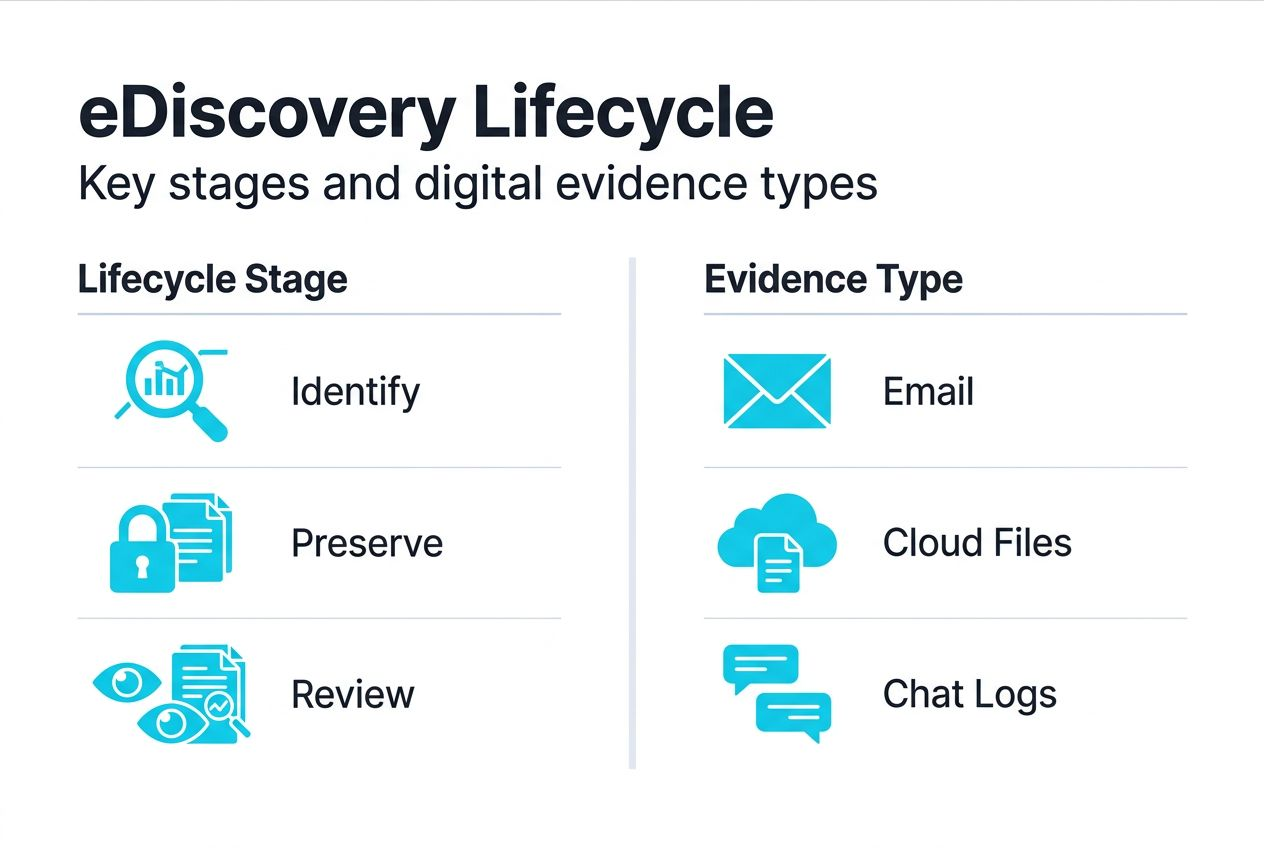
The eDiscovery lifecycle explained
The Electronic Discovery Reference Model defines seven stages in eDiscovery to ensure defensible, efficient evidence handling. Each phase requires careful coordination between legal teams and technical specialists.
The seven EDRM stages are:
- Identification: Locate potentially relevant electronically stored information across all custodian devices, servers, cloud accounts, and backup systems
- Preservation: Implement legal holds to prevent deletion or alteration of identified data, ensuring evidence remains intact
- Collection: Extract preserved data using forensically sound methods that maintain metadata and verify file integrity
- Processing: Convert collected data into reviewable formats, remove duplicates, and apply initial filtering to reduce volume
- Review: Legal teams examine processed documents for relevance, privilege, and confidentiality before disclosure
- Analysis: Identify patterns, relationships, and key evidence through advanced search, concept clustering, and timeline analysis
- Production: Deliver responsive documents to opposing parties or regulators in agreed formats meeting court requirements
| Stage | Purpose | Key actions | Legal relevance |
|---|---|---|---|
| Identification | Locate relevant data | Map data sources, interview custodians | Establishes disclosure scope |
| Preservation | Prevent spoliation | Issue legal holds, suspend deletion policies | Avoids sanctions for evidence destruction |
| Collection | Extract data defensibly | Use write-blockers, document chain of custody | Ensures admissibility |
| Processing | Reduce data volume | De-duplicate, filter, index | Controls review costs |
| Review | Assess relevance | Apply privilege, redact sensitive data | Meets disclosure obligations |
| Analysis | Find key evidence | Search patterns, build timelines | Strengthens case strategy |
| Production | Deliver to opposing party | Format per court order, maintain metadata | Fulfils procedural requirements |
Early identification and preservation prove critical. Once litigation reasonably appears imminent, legal teams must act swiftly to prevent routine data deletion or device refreshes that could destroy evidence. Forensic specialists deploy technical safeguards to maintain digital evidence preservation standards required for UK courts.
Pro tip: Engage digital forensic experts during the identification and preservation stages rather than waiting until collection. Early involvement prevents evidence loss, reduces costs, and ensures proper chain of custody documentation from the outset.
Legal frameworks and requirements in the UK
UK eDiscovery operates within strict legal boundaries balancing disclosure obligations against privacy protections. Legal professionals must navigate multiple regulatory frameworks simultaneously.
Civil Procedure Rules and Practice Direction 31B establish disclosure duties in civil litigation. Key requirements include:
- Proportionality: Disclosure scope must match case value and complexity
- Early cooperation: Parties must discuss disclosure strategy and agree search terms before incurring significant costs
- Standard disclosure: Each party must disclose documents supporting or adversely affecting their case
- Document preservation: Legal holds commence when litigation becomes reasonably foreseeable
Data protection compliance adds another layer. Electronic discovery must navigate the UK Data Protection Act 2018 and retained EU GDPR provisions. Personal data processed during eDiscovery requires lawful basis, typically legitimate interests for litigation purposes. Cross-border transfers need adequate safeguards, and unnecessary personal data collection must be minimised.
Non-compliance carries serious consequences:
- Court sanctions including adverse inferences, case dismissal, or cost awards against the offending party
- ICO fines reaching £17.5 million or 4% of annual turnover for serious GDPR breaches
- Professional liability exposure for solicitors failing to advise clients properly on preservation duties
- Spoliation findings that can doom otherwise strong legal positions
Practical compliance tips:
- Implement written litigation hold procedures before disputes arise
- Document all preservation decisions and communications with custodians
- Conduct proportionality assessments balancing disclosure scope against costs
- Engage data protection officers early when processing personal data at scale
- Use electronic disclosure processes that maintain detailed audit trails
Legal teams cannot delegate compliance responsibility. Whilst technology providers handle technical execution, solicitors retain professional accountability for meeting disclosure obligations and protecting client interests.
Common forms of digital evidence in eDiscovery
Digital evidence types include emails, instant messages, social media content, cloud storage files, mobile device data, and metadata, each presenting unique preservation and analysis challenges. Understanding these evidence categories helps legal teams plan effective collection strategies.
Email communications remain the most frequently requested evidence type. Modern email systems store far more than message text, capturing attachments, threading relationships, and delivery timestamps essential for reconstructing events. Cloud-based systems like Microsoft 365 and Google Workspace require specialist extraction tools preserving metadata intact.
Instant messaging and collaboration platforms generate extensive evidence trails through Slack, Microsoft Teams, WhatsApp Business, and similar applications. Unlike email, these platforms use proprietary formats requiring platform-specific collection methods. Ephemeral messaging features that auto-delete content demand immediate preservation once legal holds activate.
Social media evidence spans public posts, private messages, tagged locations, and interaction histories across LinkedIn, Facebook, Twitter, and Instagram. Authenticity challenges arise frequently, making proper preservation with verifiable timestamps critical. Screenshots alone rarely satisfy UK evidential standards without supporting metadata.
Cloud storage and file shares contain business documents, contracts, financial records, and project files distributed across Dropbox, SharePoint, OneDrive, and similar platforms. Version histories and edit logs provide valuable insights into document evolution and author contributions. Access controls and sharing permissions add analytical layers revealing information flows.
Mobile device data encompasses far more than calls and texts. Modern smartphones store app data, browsing history, location tracking, photographs with embedded GPS coordinates, and deleted content recoverable through forensic analysis. Device encryption and remote wipe capabilities create urgency for prompt preservation.
Metadata proves essential for establishing authenticity and chain of custody. Every digital file contains metadata recording creation dates, modification history, author information, and technical properties. Courts rely on metadata to verify documents have not been altered post-collection. Improper handling that strips metadata can render evidence inadmissible.
Encrypted data and deleted files require specialist forensic recovery techniques. BitLocker, FileVault, and mobile device encryption protect data at rest, whilst secure deletion tools actively overwrite files. Forensic specialists employ advanced methods extracting encrypted content through key recovery, exploiting system vulnerabilities, or analysing unencrypted system artifacts. Success depends on acting before encryption keys are lost or secure deletion completes.
Pro tip: Train internal teams to recognise metadata importance and preserve original file formats. Converting documents to PDF or taking screenshots destroys metadata, potentially compromising evidence admissibility. Maintain examples of digital evidence in native formats whenever possible.
The role of digital forensics in eDiscovery
Digital forensics provides the technical foundation ensuring evidence preservation maintains integrity throughout the eDiscovery lifecycle. Forensic specialists employ rigorous methodologies meeting UK legal standards for admissibility and reliability.
Preservation without alteration forms the cornerstone of forensic practice. Write-blocking hardware prevents any data modification during collection, creating verifiable forensic images. Hash value calculations generate unique digital fingerprints proving collected data matches source systems exactly. Any subsequent change to the evidence would alter hash values, immediately revealing tampering.
Chain of custody documentation tracks evidence from initial identification through final production. Forensic experts maintain detailed logs recording who accessed evidence, when, for what purpose, and what actions they performed. This documentation proves essential when opposing counsel challenges evidence authenticity or handling procedures. Courts require unbroken chain of custody before admitting digital evidence.
Advanced recovery techniques extract evidence beyond normally accessible files:
- Deleted file recovery scanning unallocated disk space for remnants of removed files
- Encrypted volume analysis attempting key recovery or exploiting implementation weaknesses
- Mobile device extraction bypassing lock screens and accessing app databases
- Cloud account forensics preserving synchronised data before auto-deletion occurs
- Metadata extraction revealing hidden document properties and edit histories
- System artifact analysis reconstructing user activity from logs, caches, and temporary files
Forensic specialists work closely with legal teams throughout the eDiscovery process. During preservation, they implement technical controls preventing data alteration. During collection, they ensure methodology maintains evidential integrity. During review, they provide technical context helping solicitors understand digital artifacts. At trial, they serve as expert witnesses explaining technical findings to judges and juries.
Key forensic steps maintaining evidence integrity:
- Conduct preliminary interviews identifying all potential data sources before collection begins
- Use validated forensic tools with documented reliability in UK courts
- Create multiple forensic images maintaining one pristine copy for verification purposes
- Document every technical decision and methodology in detailed contemporaneous notes
- Perform regular quality control checks ensuring processes maintain data integrity
- Prepare comprehensive reports explaining technical findings in accessible language
The partnership between legal knowledge and technical expertise proves indispensable. Solicitors understand relevance, privilege, and disclosure obligations. Forensic specialists understand data structures, recovery methods, and technical preservation requirements. Effective collaboration between these disciplines ensures eDiscovery meets both legal and technical standards.
Common misconceptions about electronic discovery
Legal professionals often mistakenly believe outsourcing eDiscovery removes their responsibility, but accountability remains firmly with instructing solicitors. Several dangerous misconceptions persist despite growing eDiscovery sophistication.
Misconception 1: All digital data is easily retrievable
Reality: Deleted files, encrypted volumes, and proprietary formats require specialist forensic techniques. Routine deletion policies, secure wiping tools, and hardware encryption can permanently destroy evidence if preservation occurs too late. Cloud service retention policies may auto-delete data within weeks. Early action proves essential.
Misconception 2: Technology vendors handle all compliance responsibilities
Reality: Whilst eDiscovery platforms and forensic providers execute technical tasks, solicitors retain professional accountability for meeting disclosure obligations. You must understand collection scope, review privilege determinations, and ensure production meets court requirements. Technology assists but cannot replace legal judgement.
Misconception 3: Encryption and hidden data pose minor challenges
Reality: Strong encryption can render evidence permanently inaccessible if keys are lost. Steganography hides data inside innocent-looking files. Anti-forensic tools actively destroy evidence. Sophisticated users employ multiple layers of obfuscation requiring advanced forensic analysis. Never assume data accessibility without technical assessment.
Top misconceptions corrected:
- Myth: Screenshots provide sufficient evidence preservation. Truth: Screenshots lack metadata, are easily manipulated, and rarely meet UK admissibility standards for contested evidence.
- Myth: Email deletion permanently removes messages. Truth: Email systems maintain multiple copies across servers, backups, and recipient mailboxes requiring coordinated preservation across all locations.
- Myth: Mobile devices contain limited relevant evidence. Truth: Smartphones store comprehensive activity logs, location histories, app data, and cloud synchronisation creating rich evidence sources.
Legal professionals cannot delegate their fundamental duty to preserve and produce relevant evidence. Whilst technology vendors provide essential services, solicitors remain professionally accountable for eDiscovery outcomes, compliance with court orders, and protection of client interests throughout the disclosure process.
Understanding these misconceptions helps legal teams avoid costly mistakes. Realistic expectations about data accessibility, clear accountability for compliance decisions, and early engagement with technical challenges ensure eDiscovery proceeds smoothly.
Managing the eDiscovery process: practical frameworks and technologies
The EDRM model provides practical organisation; artificial intelligence tools can reduce review times by 50%, but require legal oversight ensuring accuracy and compliance. Effective eDiscovery management balances technology capabilities with human expertise.
| Approach | Pros | Cons | Best suited for |
|---|---|---|---|
| Manual review | Complete human control, deep contextual understanding, flexible privilege decisions | Slow, expensive at scale, inconsistent coding, reviewer fatigue | Small cases under 10,000 documents, highly sensitive matters, nuanced privilege issues |
| AI-assisted review | 50% faster, consistent coding, cost-effective for large volumes, learns from reviewer decisions | Requires quality training data, needs ongoing validation, potential algorithm bias | Large-scale litigation, routine document types, cases with clear relevance criteria |
| Hybrid approach | Combines AI efficiency with human judgement, validates machine decisions, optimises resource allocation | More complex workflow, requires change management, needs technical and legal coordination | Most commercial cases balancing cost control with quality assurance |
Practical management tips for legal and corporate teams:
- Establish clear governance assigning roles for preservation decisions, collection oversight, review coordination, and production quality control
- Conduct early data mapping identifying all potential sources before collection, preventing expensive gaps requiring supplemental efforts
- Implement proportionality frameworks scaling collection scope to case value, avoiding over-collection that inflates review costs
- Use staged collection starting with key custodians and high-value sources, expanding only if initial review reveals need
- Maintain detailed project documentation tracking all decisions, methodologies, and quality checks for potential court challenges
- Train legal teams on technology capabilities and limitations, ensuring realistic expectations and informed decision-making
- Build relationships with trusted forensic and eDiscovery providers before disputes arise, enabling rapid response when litigation commences
Technology selection requires careful assessment. Predictive coding and technology-assisted review platforms excel at identifying relevant documents within large datasets but need human training and validation. Analytics tools visualise communication patterns and identify key players but require legal interpretation. Automated redaction speeds privilege protection but needs review preventing over-redaction.
Pro tip: Never rely blindly on automated tools without human validation. Sample outputs regularly, test accuracy against manual review, and maintain detailed quality control logs. Courts increasingly scrutinise AI-assisted review methodologies, requiring defensible validation demonstrating reliability. Document your technology choices and validation procedures to defend your evidence security methods if challenged.
Effective eDiscovery combines strategic planning, appropriate technology selection, and continuous quality oversight. Legal teams that master this balance deliver better outcomes whilst controlling costs.
Real-world application: case studies and best practices
UK litigation demonstrates how proper forensic collaboration strengthens cases whilst poor eDiscovery handling leads to sanctions and adverse rulings. Learning from practical examples helps legal teams implement effective procedures.
Successful forensic expert collaboration in a complex commercial fraud case preserved critical evidence that proved central to the claimant’s success. When suspicious transactions were discovered, solicitors immediately engaged forensic specialists who implemented comprehensive legal holds across the defendant’s IT infrastructure. Forensic imaging captured encrypted files and deleted communications revealing systematic fraud. Expert testimony explaining technical findings helped the judge understand complex digital evidence, ultimately supporting a substantial damages award. Early preservation prevented evidence destruction and maintained chain of custody throughout.
Sanctions for inadequate eDiscovery occurred when a defendant in an employment tribunal matter failed to preserve relevant emails despite clear legal hold obligations. The employee’s solicitor demonstrated that routine deletion policies continued operating after litigation commenced, destroying potentially exculpatory evidence. The tribunal drew adverse inferences against the employer, ultimately finding liability partly based on the evidence destruction. Additional cost sanctions penalised the inadequate preservation procedures. This case illustrates how eDiscovery failures can determine case outcomes regardless of underlying merits.
Best practices from successful implementations:
- Early preservation protocols: Implement litigation hold procedures immediately when disputes become foreseeable, before formal proceedings commence
- Comprehensive data mapping: Document all data sources, custodians, and retention policies during business-as-usual periods, enabling rapid response when litigation arises
- Clear documentation standards: Maintain detailed records of all preservation decisions, collection methodologies, and review procedures to defend against challenges
- Regular training programmes: Educate employees about preservation duties, acceptable data handling, and escalation procedures when litigation holds activate
- Technology validation: Test eDiscovery tools before deployment, document accuracy rates, and maintain quality control samples throughout review
- Expert collaboration: Build relationships with forensic specialists and eDiscovery consultants before crises, ensuring rapid expert support when needed
- Proportionality assessments: Conduct cost-benefit analysis scaling collection scope to case value, avoiding excessive preservation that inflates costs without adding value
These lessons translate into concrete procedures legal teams can implement immediately. The investment in proper eDiscovery infrastructure pays dividends through reduced litigation risk, better case outcomes, and compliance with professional obligations.
Explore expert digital forensics services
Navigating electronic discovery’s technical complexities whilst meeting strict UK legal requirements demands specialist expertise. Partnering with experienced digital forensics professionals ensures your evidence withstands scrutiny whilst optimising costs and timelines.
Computer Forensics Lab provides comprehensive eDiscovery support for legal professionals and corporate clients across London and the UK. Our services span evidence identification and preservation, forensically sound collection maintaining chain of custody, advanced data recovery and analysis, and expert witness testimony explaining technical findings in court. We understand UK disclosure obligations, data protection requirements, and evidential standards ensuring your digital evidence meets admissibility thresholds.
Whether you handle complex commercial litigation, employment disputes, regulatory investigations, or internal compliance matters, our forensic consultancy tailors solutions to your specific needs. We work collaboratively with your legal team, providing technical expertise whilst respecting your strategic control. Our proven methodologies, validated tools, and detailed documentation ensure defensible processes throughout the eDiscovery lifecycle.
Contact us to discuss how specialist digital forensics support can strengthen your litigation strategy and ensure compliance with UK eDiscovery obligations.
Frequently asked questions
What types of digital evidence are most commonly used in UK litigation?
Emails, instant messages, social media content, cloud storage files, and mobile device data appear most frequently in UK civil and criminal cases. Metadata proves critical for verifying document authenticity, establishing timelines, and demonstrating chain of custody. Courts rely on metadata to confirm evidence has not been altered since collection.
How does UK law regulate electronic discovery for compliance?
Civil Procedure Rules and Practice Direction 31B establish disclosure obligations requiring parties to preserve, collect, and produce relevant electronically stored information proportionate to case value and complexity. The Data Protection Act 2018 and GDPR impose privacy safeguards when processing personal data during eDiscovery, requiring lawful basis and minimisation principles. Non-compliance risks court sanctions, ICO fines, and professional liability exposure.
What role do forensic experts play in electronic discovery?
Forensic specialists preserve digital evidence without alteration using write-blockers and validated tools, document complete chain of custody maintaining detailed logs, and employ advanced recovery techniques extracting deleted or encrypted data. They provide technical analysis interpreting complex digital artifacts and serve as expert witnesses explaining forensic findings to courts, ensuring evidence meets UK admissibility standards.
What are common pitfalls to avoid in managing eDiscovery?
Failing to implement legal holds promptly when litigation becomes foreseeable allows routine deletion policies to destroy evidence, risking spoliation sanctions. Underestimating ongoing legal responsibility when outsourcing technical tasks leaves solicitors professionally accountable for compliance failures. Ignoring metadata preservation and encryption challenges can render evidence inadmissible or inaccessible, fundamentally weakening your case position despite otherwise strong merits.