TL;DR:
- British Airways’ £20 million ICO fine emphasizes that timely, accurate breach reporting is crucial to regulatory compliance.
- Understanding when and how to report, document, and notify affected individuals is essential to mitigate penalties and manage risks effectively.
When British Airways faced a £20 million fine from the Information Commissioner’s Office following a data breach affecting over 400,000 customers, the case sent a clear message to businesses across the UK: how you respond to a breach matters as much as preventing one in the first place. Failing to report correctly, or missing the 72-hour deadline, transforms a manageable incident into a regulatory catastrophe. This guide walks you through every stage of UK-compliant breach reporting, from recognising what must be reported to notifying affected individuals, so your organisation responds with confidence rather than panic.
Table of Contents
- Understand your reporting obligations under UK GDPR
- Prepare for reporting: Information and documentation required
- How to report to the ICO: Process and timeline
- Informing affected individuals: When and how
- Controllers, processors, and special cases
- Our perspective: The reporting mindset most businesses get wrong
- How Computer Forensics Lab supports UK breach response
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| 72-hour rule | You must report eligible breaches to the ICO within 72 hours of becoming aware to avoid penalties. |
| Document everything | Keep detailed records for all breaches, even if not reported, for audit and compliance purposes. |
| Phased reporting | You can submit initial reports quickly and provide missing details later if needed. |
| Notify individuals when required | For high-risk cases, affected people must be informed promptly with clear advice and steps. |
| Role clarity | Controllers must report to the ICO, processors must notify controllers, so know your organisation’s obligations. |
Understand your reporting obligations under UK GDPR
With the risks clearly set out, let’s clarify exactly when and what must be reported.
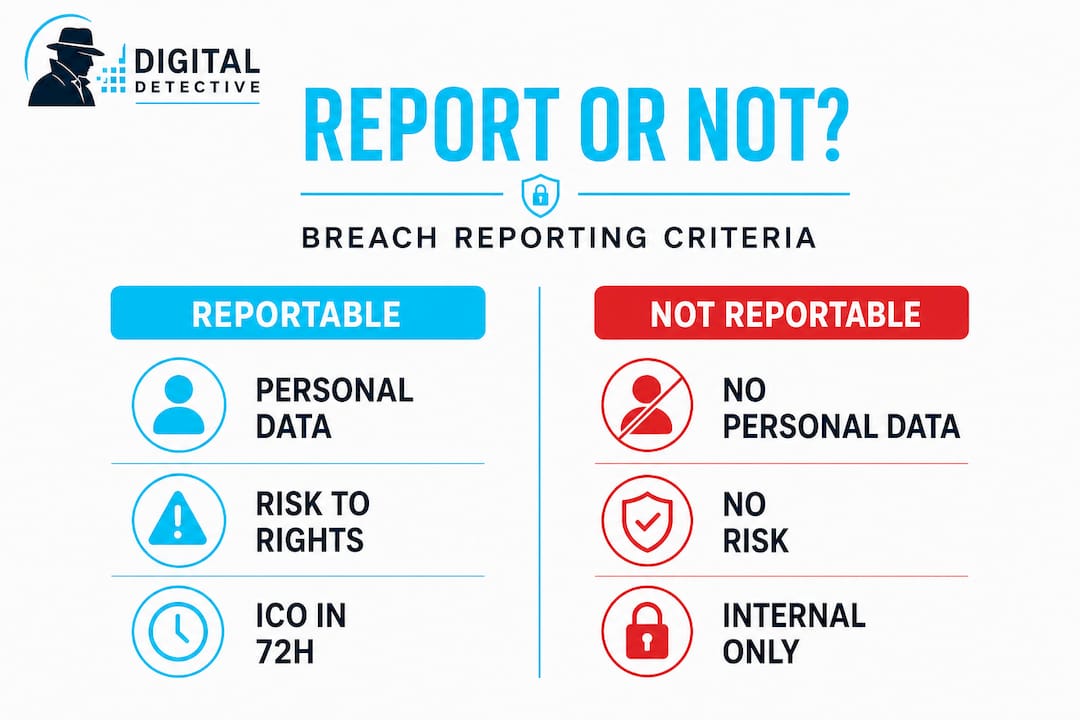
Not every security incident is a reportable data breach under UK GDPR. Understanding the distinction is critical, because both under-reporting and over-reporting carry their own risks. Under-reporting exposes you to ICO enforcement, while unnecessary reporting wastes regulatory resources and may flag your organisation as operationally immature.
A reportable breach is one that involves personal data and is likely to result in a risk to individuals’ rights and freedoms. This covers a broad range of scenarios including unauthorised access, accidental deletion, ransomware attacks encrypting personal records, and misdirected emails containing sensitive information. Under UK GDPR, businesses must report personal data breaches likely to result in a risk to individuals’ rights and freedoms to the ICO without undue delay and, where feasible, within 72 hours of becoming aware.
The 72-hour clock starts when the organisation becomes aware of the breach, meaning a reasonable degree of certainty that personal data has been compromised, not when the breach occurred. This is a critical nuance. If a breach occurred on a Monday but your IT team only confirms compromised data on Wednesday, the clock begins on Wednesday.
Here is a quick comparison of reportable versus non-reportable breaches:
| Scenario | Reportable to ICO? | Notify individuals? |
|---|---|---|
| Ransomware encrypting customer records | Yes | Likely yes (high risk) |
| Email sent to wrong recipient (no sensitive data) | No | No |
| Lost unencrypted USB with patient data | Yes | Yes |
| Accidental internal system misconfiguration (no external access) | Possibly | Unlikely |
| Hacker accesses payroll database | Yes | Yes |
| Encrypted laptop stolen with no key compromise | No | No |
Key categories of personal data that raise the risk threshold significantly:
- Special category data (health, biometric, racial or ethnic origin, religious beliefs)
- Financial data (bank account numbers, credit card details)
- Children’s data
- Data enabling identity theft (National Insurance numbers, passport details)
- Data that could endanger physical safety
“A breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, personal data” constitutes a personal data breach under UK GDPR. Not all breaches require reporting, but all require assessment.
Penalties for non-compliance are severe. The ICO can issue fines of up to £17.5 million or 4% of global annual turnover, whichever is higher. Being aware of the signs of data breaches early is therefore essential to starting your response within the window. Equally, solid foundational knowledge of GDPR data protection obligations will inform every decision you make during an incident.
Prepare for reporting: Information and documentation required
Understanding obligations is only the beginning; methodical preparation is essential before you contact the ICO.
Before you open the ICO’s online reporting form, you need to gather a specific set of information. Attempting to submit before you have the core facts risks submitting inaccurate details, which can complicate the ICO’s assessment and reflect poorly on your incident management processes.
Reporting is via an online form taking approximately 30 minutes, requiring details on what happened, when and how it was discovered, affected people, response actions taken, and a contact for follow-up queries. Phased reporting is allowed if full details are unavailable within 72 hours, which removes the pressure of waiting until you have every answer.
The following checklist covers what to gather before reporting:
- Nature of the breach: Was it a confidentiality breach, integrity breach, or availability breach?
- Date and time of the breach and of discovery
- Categories of personal data involved (e.g. health records, financial data, employee records)
- Approximate number of individuals affected
- Approximate number of personal data records affected
- Likely consequences of the breach for affected individuals
- Measures taken or proposed to address the breach and mitigate its effects
- DPO or contact details for the person handling the response
Regardless of whether a breach is reportable to the ICO, all breaches must be documented internally with the facts of what happened, the effects assessed, and the remedial actions taken. This internal record serves as your evidence trail should the ICO ever investigate.
| Documentation element | Internal record | ICO report |
|---|---|---|
| Date and time of breach | Required | Required |
| Nature and scope of data affected | Required | Required |
| Number of individuals affected | Required | Required |
| Immediate containment actions | Required | Required |
| Long-term remediation steps | Required | Optional |
| DPO review notes | Required | Not required |
| Evidence of notification to individuals | Required | Required if applicable |
Pro Tip: Appoint a dedicated breach response lead before an incident ever occurs. This person owns the documentation process, coordinates with your DPO, IT, and legal teams, and ensures nothing falls through the cracks under pressure.
For organisations uncertain whether their incident crosses the reporting threshold, the ICO provides self-assessment tools on its website. Combining these with specialist support for investigating data breaches ensures your assessment is thorough and defensible. Structured data security documentation practices also strengthen your overall compliance posture long before any breach occurs.
How to report to the ICO: Process and timeline
Armed with the right documentation, you can now take precise action, here is how.
The ICO online reporting process is more structured than many organisations expect. Following these steps reduces the risk of submitting an incomplete or inaccurate report:
- Contain the breach immediately. Before reporting, take all available steps to stop ongoing data loss, revoke compromised credentials, isolate affected systems, or block unauthorised access.
- Assess the risk level. Determine whether the breach is likely to result in a risk to individuals’ rights and freedoms. Use your internal records and the ICO’s self-assessment guidance.
- Decide on reportability. If there is a risk to individuals, report to the ICO. If there is a high risk, also notify affected individuals (covered in the next section).
- Access the ICO online reporting portal. Navigate to the ICO’s official breach notification form. Have all your pre-gathered documentation ready before you begin.
- Complete the form accurately. The form asks for the type of breach, data categories involved, number of records, number of individuals, what happened, how it was discovered, and what actions have been taken. Reporting is via an online form taking approximately 30 minutes.
- Submit an initial phased report if necessary. If you do not have all the details within 72 hours, submit what you know and clearly indicate that further information will follow. Ongoing or complex breaches allow phased information submission without undue further delay, prioritising initial notification over completeness.
- Record the submission confirmation. Save the ICO reference number issued after submission. This is your evidence that you reported within the required window.
- Follow up with supplementary information promptly. If you submitted a phased report, provide the remaining details as soon as they are available. Do not wait until the full picture is certain; communicate proactively.
If you are reporting after 72 hours, the ICO requires you to explain the delay. Document the reasons clearly, whether due to the complexity of the investigation, the time required to identify affected data, or a delay in initially recognising the breach. Regulatory scrutiny intensifies with late reports, so the explanation must be credible and well-evidenced.
Pro Tip: Set an internal alert at 48 hours from breach awareness. This gives your team a final window to complete the report or submit an initial phased notification with a clear follow-up commitment, keeping you well within the 72-hour limit.
A useful statistic worth noting: the ICO received over 2,700 data breach reports in a single quarter in 2023, underscoring that your organisation is far from alone in navigating this process. Having documented corporate data protection tips embedded in your operational procedures means your team is not improvising under pressure.
Informing affected individuals: When and how
Once regulators have been notified, there is a further legal step in some cases, telling those affected.
Not every reportable breach requires individual notification. The threshold is higher: you must notify affected individuals only when the breach is likely to result in a high risk to their rights and freedoms. High risk typically includes situations where the breach could lead to identity theft, financial loss, physical harm, discrimination, or significant distress.
For high-risk breaches, notify affected individuals without undue delay in clear and plain language, including the nature of the breach, its likely consequences, and the mitigation measures taken or proposed.
Key criteria triggering individual notification:
- The breach involves special category data such as health records or biometric information
- The breach could facilitate identity theft or financial fraud
- The affected individuals are vulnerable persons, including children
- The data disclosed could endanger physical safety
- There is a reputational or professional harm risk to individuals
What to include in individual notifications:
- Plain English description of what happened and when
- What data was involved and approximately how many records
- Steps you have already taken to contain and address the breach
- What individuals can do to protect themselves (e.g. change passwords, monitor accounts, contact their bank)
- Contact details for your DPO or designated breach response contact
- Details of any support your organisation is offering, such as credit monitoring
“Notification should not be delayed to avoid reputational damage. Individuals have a right to know when their data has been compromised, and timely communication reduces the harm they may suffer.”
Effective data breach communication with affected individuals requires balancing legal clarity with human sensitivity. Avoid jargon-heavy language that confuses rather than informs. Every communication you send should be logged, including the date, channel, content, and recipient list, as part of your broader incident response strategies documentation.
Controllers, processors, and special cases
Different roles within an organisation or supply chain affect who is responsible for each reporting step.
Many businesses operate within complex data processing arrangements, particularly those using third-party cloud providers, payroll services, or IT managed service providers. Understanding who carries the reporting obligation is not optional. Getting it wrong creates a compliance gap that neither party realises until regulators come knocking.
Processors must notify controllers without undue delay upon discovering a breach. The data controller then carries responsibility for reporting to the ICO. Electronic communications providers face the additional obligation to report under the Privacy and Electronic Communications Regulations (PECR), also within 72 hours.
Responsibilities broken down:
- Data controllers: Own the reporting obligation to the ICO; responsible for assessing risk and notifying individuals where required.
- Data processors: Must inform the relevant controller promptly; cannot self-report to the ICO on the controller’s behalf unless contractually authorised.
- Joint controllers: Must agree in advance which party leads on breach notification; this should be documented in the joint controller agreement.
- Electronic communications providers: Face PECR obligations in addition to UK GDPR, requiring notification to both the ICO and, in certain cases, affected subscribers.
Pro Tip: Include breach notification clauses in all data processing agreements (DPAs) with third-party providers. Specify the maximum time frame for processor-to-controller notification, ideally within 24 hours, to give the controller sufficient time to meet the 72-hour ICO deadline.
For organisations reviewing their breach responsibilities across complex supply chains, working through a structured review of reviewing breach responsibilities with legal and forensic support ensures that accountability sits where it should.
Our perspective: The reporting mindset most businesses get wrong
Most organisations approach data breach reporting as a compliance task. File the form, meet the deadline, move on. That framing is the problem.
Experienced digital forensics practitioners see this pattern repeatedly: businesses focus so heavily on the ICO submission that they underinvest in the underlying investigation. An accurate report to the ICO is only as good as the forensic investigation informing it. If you do not know which records were accessed, you cannot assess individual risk. If you cannot confirm the attack vector, your remediation is guesswork. Submitting an early, incomplete report and then never following up with substantive findings is not phased reporting, it is abandonment.
The organisations that manage breaches well share one common trait. They treat the ICO notification as a prompt to investigate thoroughly, not as the finish line. The 72-hour deadline forces urgency, but the investigation work that follows over days or weeks determines whether you genuinely understand what happened and whether you can prevent recurrence. That is where real compliance value lives.
There is also a cultural dimension that gets overlooked. Employees who spot potential breaches often hesitate to report internally because they fear blame. In that environment, the 72-hour clock is already running before leadership even knows there is a problem. Investing in a psychologically safe internal reporting culture, where staff are encouraged to raise concerns without fear of sanction, is arguably the most important structural change a business can make to its breach response capability.
How Computer Forensics Lab supports UK breach response
When a data breach occurs, the quality of your forensic investigation directly determines the quality of your regulatory response. At Computer Forensics Lab, we assist legal teams, compliance officers, and corporate clients across the UK in conducting structured, court-ready digital investigations that support accurate ICO notifications and robust internal documentation. From identifying the scope of compromised data to producing expert witness reports that stand up to regulatory scrutiny, our team brings the technical depth that breach response demands. If your organisation is navigating an active incident or wants to stress-test its response procedures before one occurs, we provide the forensic expertise to help you act with precision and confidence.
Frequently asked questions
What if I do not have all breach details within 72 hours?
Submit an initial report to the ICO within 72 hours with the information you have, then provide additional details as they become available. Phased reporting is explicitly permitted under UK GDPR, so completeness can follow promptly after initial notification.
Do I need to document a minor breach that is not reportable?
Yes, every breach must be recorded internally even if it does not meet the ICO reporting threshold. All breaches must be documented with the facts, assessed effects, and remedial actions taken, creating a defensible audit trail.
Who notifies affected individuals for a high-risk breach?
The data controller is responsible for informing affected individuals directly and without undue delay. Controllers handle ICO reporting and all communications with the individuals whose data has been compromised.
What happens if I report late?
You must provide a clear explanation for the delay when submitting to the ICO, and late notification increases the likelihood of regulatory scrutiny. If notification occurs after 72 hours, reasons must be provided and may affect how the ICO assesses your organisation’s overall compliance posture.
Where can I find practical examples or self-assessment tools?
The ICO’s website provides self-assessment tools and case studies to help organisations determine whether a breach requires reporting and how to approach the notification process correctly.