TL;DR:
- Confidential client data exposed due to misconfigured cloud servers highlights the need for organizations to implement proportionate, documented security measures under UK GDPR. Legal and corporate teams must embed privacy by design, conduct risk assessments, and follow baseline controls like those in Cyber Essentials to protect sensitive information effectively. Prepared incident response plans and context-driven controls are essential for maintaining compliance and mitigating reputational and legal risks.
A law firm’s confidential client files exposed through a misconfigured cloud server. A corporate legal team fined by the Information Commissioner’s Office for failing to implement basic access controls. These scenarios are not hypothetical; they happen with alarming regularity across England. Under the UK GDPR and Data Protection Act 2018, organisations that process personal data bear a legal duty to protect it with rigorous, documented measures. This guide delivers practical, step-by-step strategies for legal professionals and corporate teams to meet those obligations and safeguard their reputations.
Table of Contents
- Understanding regulatory requirements and risks
- Preparing your organisation: Baseline controls and risk assessment
- Implementing privacy protection: Key steps for legal and corporate environments
- Incident response and breach notification: Meeting ICO expectations
- Why context-driven privacy protection is now critical
- Strengthen your digital privacy strategy with expert support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Bespoke security required | Digital privacy controls must be tailored to risks, not applied as a generic checklist. |
| Cyber Essentials as baseline | Adopting Cyber Essentials delivers a government-backed starting point for privacy and cybersecurity. |
| Privacy by design matters | Implement privacy controls from the outset and ensure they persist throughout the information lifecycle. |
| Preparedness for breaches | Have clear incident response plans—timely reporting is legally required and protects your reputation. |
Understanding regulatory requirements and risks
Legal and corporate teams operate under clear statutory obligations when it comes to digital privacy. The starting point is the UK GDPR’s security principle, but understanding what that actually demands in practice is where many organisations fall short.
The security principle is described by the ICO as requiring “appropriate” security measures that must be aligned to risk factors and not treated as one-size-fits-all. That distinction matters enormously. A small legal practice handling routine conveyancing documents does not face the same threat landscape as a corporate firm managing sensitive merger negotiations or litigation files. Your security measures must reflect the actual risks your organisation faces, not a generic template applied uniformly.
Closely linked to this is the concept of data protection by design and by default. The ICO’s guidance on this principle requires that privacy practices are embedded at the start of any system or process and maintained throughout its lifecycle. It is not a retrospective exercise. It means that when your firm adopts a new case management platform, or when a corporate client onboards a new cloud service, privacy controls must be considered from the outset, not bolted on after deployment.
Data minimisation sits at the heart of ongoing compliance. This means collecting and retaining only the personal data genuinely necessary for a specific, defined purpose. For legal teams, that translates into regularly auditing case files, removing redundant personal information, and ensuring that access to client data is restricted to those who genuinely need it.
The ICO is unequivocal: security measures must be evidence-based and documented. You need to be able to demonstrate, not merely assert, that your measures are appropriate. Compliance with GDPR privacy notice guidance and thorough documentation of your decisions is the foundation of a defensible position if questions are ever raised.
Key regulatory obligations to address include:
- Implementing technical and organisational measures proportionate to the risks identified
- Conducting and recording Data Protection Impact Assessments (DPIAs) for high-risk processing
- Maintaining a Record of Processing Activities (ROPA) that accurately reflects current operations
- Reviewing third-party data processor contracts to ensure adequate protections
- Training staff on data handling, recognising phishing attempts, and reporting concerns
Understanding the principles is essential, but the practical response to a breach requires a separate, specific plan. Knowing how incident response in legal context works before a crisis hits is far more effective than scrambling to respond under pressure.
Preparing your organisation: Baseline controls and risk assessment
With a clear understanding of what is required, the next practical step is to ensure your organisation is properly prepared with the right baseline controls and a genuine risk management mindset.
The NCSC’s Cyber Essentials scheme provides the minimum standard recommended by the Government, structured around five core technical controls. For legal and corporate organisations, achieving Cyber Essentials certification is a credible baseline that demonstrates commitment to cybersecurity to clients, regulators, and insurers alike.
The five controls are:
- Firewalls: Boundary firewalls and internet gateways that protect the perimeter of your network from unauthorised access
- Secure configuration: Ensuring systems are configured securely from the outset, removing default credentials and unnecessary services
- Security update management: Applying software patches and updates promptly, typically within 14 days of release for critical vulnerabilities
- User access control: Restricting administrative privileges, enforcing multi-factor authentication, and removing access when employees leave
- Malware protection: Installing and maintaining up-to-date anti-malware tools across all in-scope devices
The Cyber Essentials requirements for IT infrastructure are clear that all devices used for organisational business, including BYOD (Bring Your Own Device), home working, and remote working devices, are in scope by default. This is frequently overlooked. A paralegal working from home on a personal laptop that accesses the firm’s case management system is covered by those same requirements.
| Risk area | Typical risk level | Recommended control |
|---|---|---|
| BYOD personal devices | High | MDM policy, network segregation |
| Remote working | High | VPN, MFA, device encryption |
| Third-party access | Medium to High | Least privilege, access logs |
| Legacy software | High | Patch schedule, replacement plan |
| Insider threat | Medium | Role-based access, audit trails |
Risk assessment should directly inform which controls you prioritise and how rigorously you apply them. Do not simply implement every control at maximum intensity regardless of context. A proportionate, documented rationale is what regulators expect to see. Consulting our UK cybersecurity best practices resource can help organisations identify the right priority areas based on their specific processing activities.
Equally, using a structured cybersecurity checklist tailored to UK compliance requirements will help you identify gaps before they become liabilities.
Pro Tip: Document every asset risk-rating decision, including the reasoning behind it. If the ICO ever investigates an incident, demonstrating that you conducted a thorough, reasoned risk assessment is far more persuasive than simply producing a list of controls without context.
Implementing privacy protection: Key steps for legal and corporate environments
Preparation is only half the battle. Applying the right measures in practice is where real protection and compliance are achieved.
Implementation should follow a structured sequence. The NCSC’s network security guidance explicitly addresses restricting access and protecting data in transit, covering the confidentiality, integrity, and availability of data as it moves across networks. Those three properties, often called the CIA triad, form the backbone of any sound privacy protection strategy.
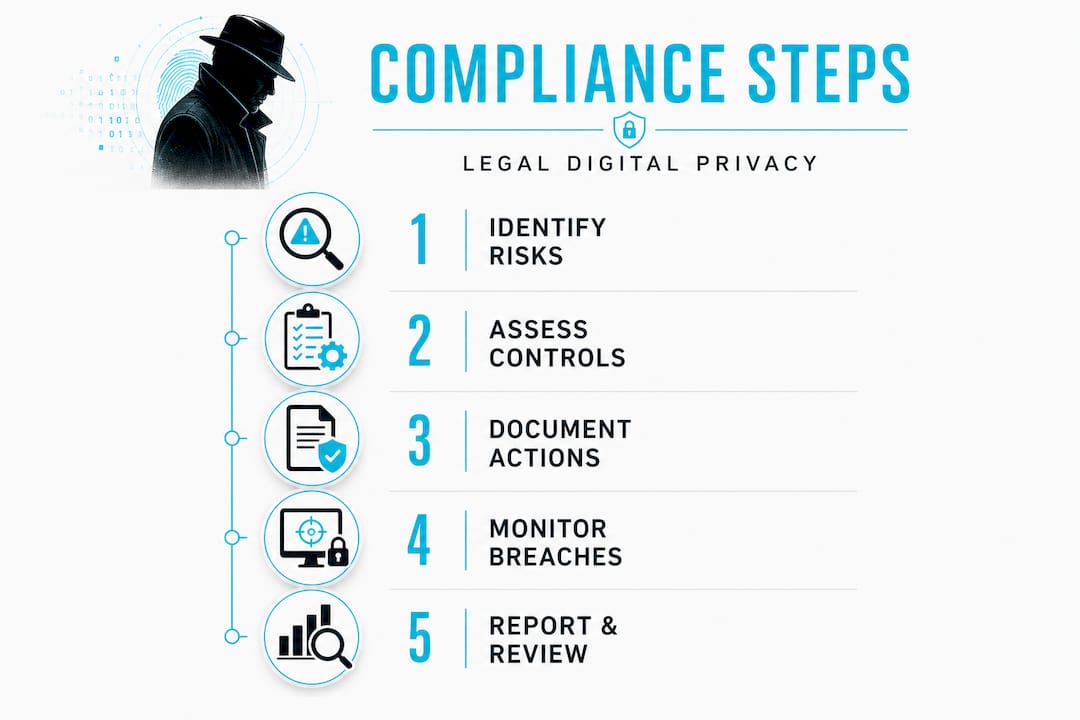
Follow these steps to implement effective protection:
- Map all data assets: Create a complete inventory of where personal data is stored, processed, and transmitted. Include cloud services, email archives, case management systems, and physical records where relevant.
- Apply data minimisation: Audit what data you hold and delete or archive anything no longer necessary for its original purpose, in line with your retention policy.
- Implement role-based access controls: Ensure staff can only access data relevant to their specific role. Regularly review and update access rights, especially when roles change or employees depart.
- Encrypt data in transit and at rest: Use Transport Layer Security (TLS) for all data in transit across networks. Apply full-disk encryption on laptops, mobile devices, and portable storage media.
- Secure network infrastructure: Segment internal networks to limit the spread of a potential breach. Firewalls, intrusion detection systems, and regular network monitoring are not optional extras for legal and corporate environments.
- Maintain a patch management schedule: Critical patches must be applied without delay. Assign clear responsibility and document completion.
- Embed privacy reviews into new projects: Before deploying any new technology or processing activity, ensure a privacy review or DPIA is completed and signed off.
The ICO’s guidance on data protection by design and by default cites Article 25(2) as the obligation to implement appropriate measures so that, by default, only personal data necessary for each specific purpose is processed. In practice, this means default settings on new systems should favour privacy rather than openness.
| Measure | Legal environment | Corporate environment |
|---|---|---|
| Access controls | Role-based by matter/case | Department and project level |
| Data minimisation | Client file review schedule | CRM and HR data audits |
| Encryption | Case files, email, portals | Financial records, IP data |
| Network monitoring | Incident alerts and logging | Continuous threat detection |
| Staff training | CPD-integrated privacy training | Annual mandatory e-learning |
Ensuring resilient cybersecurity practices are embedded into daily operations rather than treated as a once-a-year IT exercise significantly reduces exposure to both regulatory penalties and reputational harm.
Pro Tip: Invest in state-of-the-art network monitoring tools capable of detecting anomalous behaviour in real time. Many significant data breaches in legal environments go undetected for weeks because basic monitoring was absent. Early detection is the most cost-effective defence you have.
Incident response and breach notification: Meeting ICO expectations
Even with robust privacy controls, incidents can happen. It is vital to be prepared to act quickly and appropriately if a breach occurs.
The ICO is unambiguous on timescales. Personal data breaches must be reported to the supervisory authority within 72 hours where feasible. If the breach is likely to result in a high risk to the rights and freedoms of individuals, affected people must also be informed without undue delay. That phrase “without undue delay” means as soon as practicable, not when it is convenient.
“Not every personal data breach needs to be reported to the ICO, but you must still document all breaches, including those you decide not to report, along with the reasoning for that decision.” ICO guidance on personal data breaches.
A well-structured incident response plan must address the following in order:
- Detect and confirm the breach: Identify what has occurred, what data is affected, how many individuals are involved, and the likely cause.
- Contain the incident: Isolate affected systems immediately to prevent further exposure. This may mean taking systems offline temporarily.
- Assess the risk: Evaluate the likelihood and severity of harm to individuals whose data has been compromised. This assessment drives your notification obligations.
- Notify the ICO if required: Submit a breach report within 72 hours, including details of the nature of the breach, categories of data, likely consequences, and remedial actions taken.
- Notify affected individuals if required: Where the risk to rights and freedoms is high, communicate clearly, promptly, and in plain language what happened and what affected people should do.
- Document everything: Record every decision made throughout the process, including decisions not to notify, with full reasoning. This documentation is your primary defence in any subsequent ICO investigation.
Developing a thorough incident response strategy before an incident occurs, rather than designing your response under pressure, is the difference between a manageable event and a regulatory disaster. Having clearly defined incident response procedures signed off at board level and tested regularly through tabletop exercises will give your team the confidence to act decisively when it matters most.
Why context-driven privacy protection is now critical
There is a persistent misconception in both legal and corporate environments that compliance is achieved by ticking boxes. Install a firewall, complete the DPIA template, send the annual training email, done. That mindset is precisely what creates vulnerability.
The ICO is explicit that “appropriate security” is not a fixed list. It must be selected by considering the processing context and risks, the state of the art, and proportionate costs. That means your measures must be justified and documented, not mechanically applied. A law firm handling highly sensitive litigation data faces fundamentally different risks than a corporate procurement team managing supplier contracts. Applying identical controls to both is not compliance; it is the illusion of compliance.
We have seen cases where organisations deployed technically sophisticated security tools but failed entirely on the documentation side. When the ICO investigated, those organisations could not explain why particular measures were chosen, what risks they were designed to address, or how they were reviewed over time. The result: enforcement action despite perfectly functional technical controls. The defence collapsed not because the technology failed, but because the decision-making process was invisible.
Context-driven privacy protection means making deliberate, reasoned choices at every level. It means considering the specific categories of data you process, the realistic threat actors you face, and the likely impact of different breach scenarios on your clients or employees. It also means revisiting those choices regularly as your operations, technology, and threat environment evolve. Reviewing the key benefits of incident response will illustrate precisely how this approach reduces both financial exposure and reputational damage when incidents occur.
The firms that genuinely lead on privacy compliance are not those with the largest IT budgets. They are the ones where privacy thinking is embedded in leadership decisions, procurement processes, and operational culture. That is a competitive advantage, not just a regulatory obligation.
Strengthen your digital privacy strategy with expert support
Translating regulatory requirements into effective, defensible privacy protection takes more than policy documents and standard software tools. Computer Forensics Lab works with legal professionals and corporate clients across England to provide specialist forensic investigation, evidence-based analysis, and expert witness support when privacy incidents escalate into legal matters. Understanding your digital privacy exposure through professional forensic assessment identifies vulnerabilities before they become breaches. Our digital forensics services support both proactive compliance work and reactive incident investigations, maintaining full chain of custody for any evidence gathered. If your team needs robust incident response support aligned to ICO expectations, we are ready to assist.
Frequently asked questions
What are the five controls in Cyber Essentials?
The Cyber Essentials scheme mandates firewalls, secure configuration, malware protection, user access control, and security update management for all in-scope devices.
How soon must a personal data breach be reported to the ICO?
Personal data breaches must be reported to the ICO within 72 hours where feasible, and affected individuals informed without undue delay if risks to their rights and freedoms are high.
Does privacy by design and by default apply to all types of data?
Yes. The ICO’s guidance on this principle requires that practices are embedded from the outset for any personal data, ensuring only what is necessary for each specific purpose is processed.
What is the role of BYOD in digital privacy protection?
BYOD devices used for organisational data or services must meet the same security control requirements as corporate devices under Cyber Essentials, including authentication and firewall obligations.