Digital forensic trends 2025 explored for UK analysts: AI advancements, cloud forensics, and the latest legal challenges facing practitioners worldwide.
Digital Forensic Trends 2025: AI, Cloud, and Risk


Digital forensic trends 2025 explored for UK analysts: AI advancements, cloud forensics, and the latest legal challenges facing practitioners worldwide.

Digital forensics in UK courts secures justice by ensuring admissible evidence, expert witness reports, chain of custody, and data privacy compliance.

Master step by step evidence collection for digital investigations with this guide. Learn each stage to ensure legal integrity and forensic accuracy.

Discover how to secure digital evidence 2025 with step-by-step forensic actions for professionals, ensuring integrity and admissibility in legal cases.

Chain of custody in digital forensics explained – learn its definition, legal requirements, common errors, and how it ensures evidence admissibility.

Why analyse email evidence—vital for UK defence lawyers. Learn key types, forensic methods, legal standards, risks, and how it shapes case strategy.

Why outsource digital forensics: uncover key benefits, expert requirements, judicial standards, cost implications, and risks for legal cases in London.

Role of forensic consultancy in digital litigation, types of forensic expertise, legal standards, expert witness duties, and common pitfalls for lawyers.

Role of forensic testimony in cybercrime trials for UK lawyers. Covers types of expert evidence, legal standards for admissibility, and common pitfalls to avoid.

Role of forensics in litigation, including digital evidence types, admissibility standards, expert witness duties, and risks for legal professionals.

Discover how to document forensic findings step by step, ensuring accuracy, legal compliance, and evidence integrity for court-ready digital investigations.

Digital evidence in court shapes criminal cases; learn about admissibility standards, legal frameworks, types, risks, and defence strategies for lawyers.

Legal considerations for digital forensics—explore UK requirements, chain of custody, privacy laws, admissibility, investigator duties and common risks.

Social media forensics demystified: core principles, key forensic processes, legal standards, privacy concerns, and risks for legal professionals.

Digital forensics trends 2025 for legal and cyber investigations: AI automation, cloud challenges, deepfake detection, and evolving legal standards explained.
Digital evidence preservation for legal and forensic cases. Learn types of digital evidence, chain of custody essentials, common errors, and compliance steps.

Mobile forensics in court for defence—evidence types, the legal process, expert reporting, risks, and compliance for robust legal strategies.

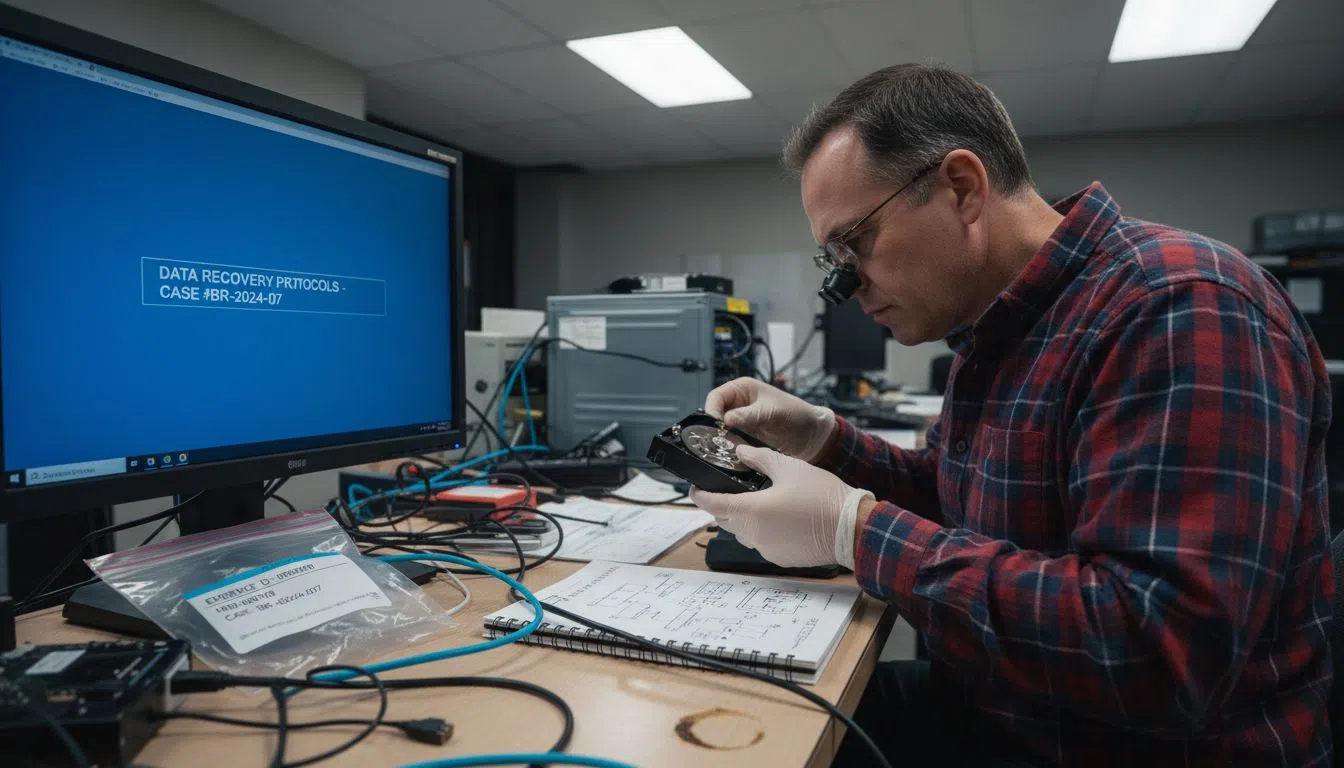
Explore 7 essential data recovery best practices 2025 for legal experts and IT managers to boost cybersecurity and litigation success across the UK.

Documenting forensic process safeguards digital evidence, ensures court admissibility, and supports chain of custody. Explore risks, UK standards, and real cases.

Discover 7 top data recovery techniques for legal cases. Learn step-by-step methods essential for criminal defence attorneys protecting digital evidence.

Discover a 7-step social media investigation checklist for digital forensics professionals. Enhance case preparation with actionable tips for legal success.

Explore 7 essential cloud forensics best practices tailored for legal digital forensics professionals. Gain practical tips for secure and effective cloud evidence collection.

Benefits of forensic data analysis: discover types, techniques, legal impact, risk management, and how it supports criminal defence in London.

Learn the step-by-step process for creating expert witness reports focused on digital forensic evidence and ensure your reports are thorough, defensible, and court-ready.

Data recovery 2025 for legal forensics—explore types, forensic methods, legal standards, risks, and chain of custody best practices worldwide.

Discover 7 essential mobile device investigation tips for forensics. Learn practical methods to enhance digital evidence collection and case outcomes effectively.

Electronic disclosure in legal cases clarified. Learn key types, processes, legal obligations, and challenges for digital evidence in UK litigation.
Learn how to preserve chain of custody with step-by-step methods for securing, documenting, transferring, and validating digital evidence in legal cases.

Challenges in cloud forensics impact legal and cybercrime investigations. Explore data acquisition obstacles, legal frameworks, evidence integrity, and provider cooperation.

Discover a digital forensics checklist with 7 key steps designed to guide legal professionals in London through evidence collection and best practices.

Discover a step-by-step guide on social media evidence collection for litigation. Ensure robust preparation, precise capture, and secure validation for legal professionals.
Social media forensics for legal cases, covering evidence extraction, forensic analysis procedures, UK legal frameworks, and chain of custody best practices.

Discover the advantages of cloud forensics for legal professionals. Learn how it enhances evidence collection, preserves integrity, and supports UK court compliance.

Master step by step forensic analysis with our guide for legal and corporate cases. Learn every stage from setup to reporting for reliable outcomes.

Master the cloud data forensics workflow using a detailed, step-by-step guide for legal investigations, ensuring evidence integrity and successful case outcomes.

Digital evidence is vital for legal defence, covering types, core challenges, UK law, chain of custody, and risks for criminal cases in London.

Digital forensics in business supports legal compliance, incident response, and evidence management. Learn its key types, processes, and legal obligations.

Digital forensics terminology is vital for legal professionals. Understand evidence types, core processes, legal standards, and risks in UK practice.
Learn the decisive role of forensics in legal cases. Explore forensic types, legal standards, chain of custody, expert witness reports, and risks.

Mobile device data extraction explained for forensics: methods, types, legal standards, risks, and admissibility for investigations in London and worldwide.

Forensic report: definition, types, legal standards and risks. Explore key digital forensic techniques and expert witness insights for UK cases.

Learn how to gather forensic evidence step by step, from planning and collection to maintaining chain of custody and validating digital findings.

Why conduct cyber investigations for law firms and corporates: Key threats, legal duties, evidence value, and risk management essentials explained.

Discover the real benefits of mobile forensics, including legal admissibility, evidence recovery, key methods, risks, and practical usage.
Discover the role of forensic analysis in court—covering digital evidence types, admissibility, chain of custody, expert witnesses, and legal reliability for defence attorneys.

Discover the vital role of forensics in cybersecurity, from digital evidence collection to legal compliance, expert witness reports, and risk mitigation.

Data recovery explained with expert forensics—covering methods, types, legal standards, risks, and handling digital evidence for law professionals.

Why use digital forensics: Learn how evidence is uncovered, its importance in legal cases, compliance with the law, and ways it prevents risks.

Discover 7 digital forensics best practices for 2025 to enhance evidence handling, data integrity, and investigations for legal and business professionals.

Role of forensic consultants in litigation, types of services, legal requirements, and expert witness duties for legal and corporate clients.