TL;DR:
- Forensic imaging creates an exact, verified bit-for-bit copy of digital devices for court use.
- Proper process includes documentation, write-blocking, hash verification, and chain of custody.
- Using validated tools and following best practices ensures evidence admissibility and integrity.
Many legal professionals and investigators assume that copying a hard drive is straightforward, much like duplicating any ordinary file. That assumption can destroy a case. True forensic imaging is a precise, court-ready process that creates a verified, bit-for-bit replica of a digital storage device, preserving every fragment of data exactly as it existed at the time of seizure. According to SWGDE best practices, forensic imaging preserves digital evidence integrity far beyond what standard copying achieves. This guide covers definitions, the step-by-step process, legal implications, and practical tools to help you handle digital evidence correctly from the outset.
Table of Contents
- What is forensic imaging?
- The forensic imaging process: step by step
- Forensic imaging vs standard copying: why it matters in court
- Tools and best practices for effective forensic imaging
- Why context matters: not all forensic imaging is equal
- Need help with forensic imaging or digital evidence collection?
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Forensic imaging defined | It is a verified bit-by-bit copy of digital storage made for legal integrity. |
| Legal chain of custody | Documentation, validation, and hash verification are vital for court acceptance. |
| Specialised tools required | Court-accepted tools and verified procedures protect admissibility in investigations. |
| Context of terminology | Forensic imaging may mean different things; clarity is critical in legal matters. |
What is forensic imaging?
Forensic imaging, in the context of digital investigations, means creating an exact, bit-for-bit duplicate of a digital storage device, whether that is a hard drive, USB stick, mobile phone memory, or solid-state drive. Every single bit of data is copied, including deleted files, unallocated space, and hidden partitions that ordinary copying would miss entirely.
This is fundamentally different from dragging and dropping files or using standard backup software. When you copy files conventionally, the operating system modifies metadata such as access timestamps. That modification alone can render evidence inadmissible. A forensically sound image captures the entire storage medium without altering a single bit, and that integrity is then verified mathematically.
The key features that distinguish forensic imaging from ordinary copying include:
- Bit-for-bit duplication: Every sector of the storage device is copied, not just visible files
- Write-blocking: Hardware or software write blockers prevent any data being written to the original device during acquisition
- Hash verification: Cryptographic hash values (typically MD5 or SHA-256) confirm the copy is identical to the original
- Chain of custody documentation: Every action taken is recorded, timestamped, and signed
- Court-accepted formats: Images are saved in formats such as E01 or DD that are recognised by forensic analysis tools
It is worth noting that the term “forensic imaging” occasionally appears in medical and radiological contexts, referring to X-rays or MRI scans used in post-mortem examinations. As SWGDE clarifies, radiological forensic imaging is an entirely separate discipline. In digital investigations, the term always refers to bit-for-bit disk imaging.
Pro Tip: When briefing counsel or presenting evidence to a court, always specify “digital forensic imaging” to avoid any ambiguity with medical imaging terminology. Precision in language reflects precision in practice.
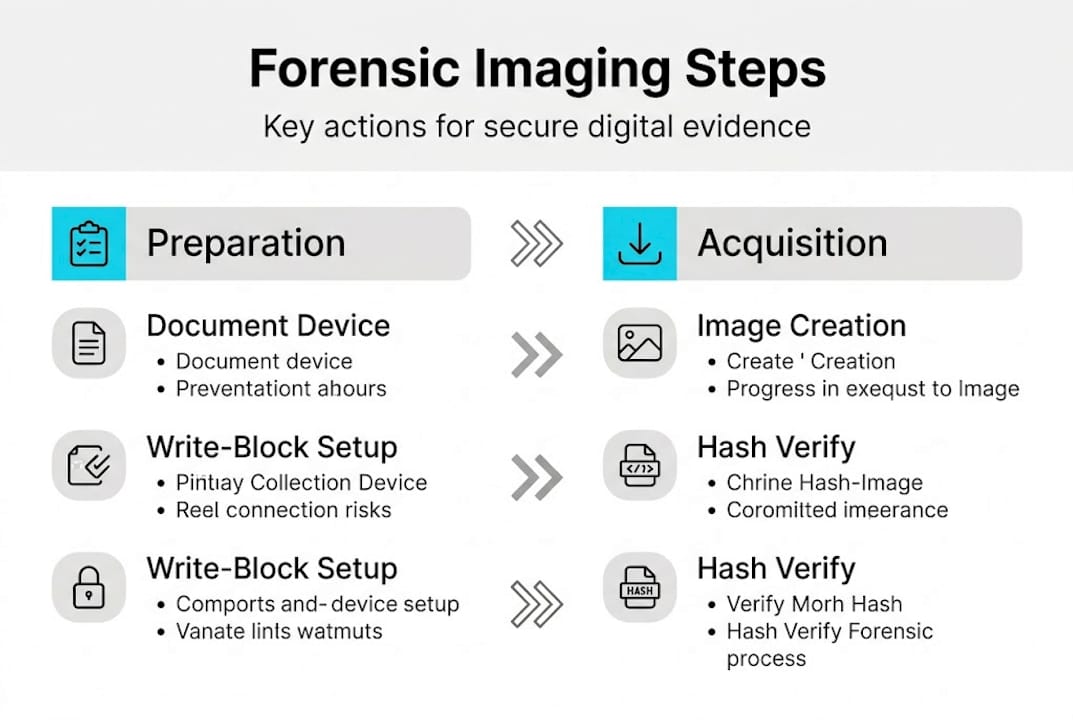
The forensic imaging process: step by step
Understanding the definition sets the stage for exploring how forensic imaging is done in real-life investigations. The process is methodical by design because any deviation can compromise the entire evidential chain.
- Preparation and documentation: Before touching the device, record its make, model, serial number, and physical condition. Photograph it. Note the environment, date, time, and the identity of everyone present. This forms the foundation of your digital evidence chain of custody.
- Attach a write blocker: Connect a validated hardware write blocker between the original device and the imaging workstation. This prevents any data being written to the source drive, which is a non-negotiable step.
- Select a validated imaging tool: Use court-accepted software such as FTK Imager or EnCase. These tools are validated, widely recognised, and produce output formats accepted in UK legal proceedings.
- Acquire the forensic image: Run the imaging software to create a complete sector-by-sector copy. Depending on drive size, this can take minutes or several hours. Do not interrupt the process.
- Generate and record hash values: Once acquisition is complete, the tool generates a hash value for both the original device and the image. These must match precisely.
- Verify and document: Compare hash values and record the result formally. Store the image on secure, forensically clean media and update your digital evidence preservation log.
“SWGDE best practices mandate chain of custody documentation, validated tools, and hash verification as the minimum standard for any forensic acquisition.”
Hashing is not a formality. As forensic acquisition principles confirm, a verified hash ensures a 100% bit-match, making the forensic image defensible under cross-examination. Without it, opposing counsel has grounds to challenge the entire dataset.
Pro Tip: Always generate hash values twice using two different algorithms, such as MD5 and SHA-256, simultaneously. If one algorithm is ever successfully challenged in court, the second provides independent corroboration.
Forensic imaging vs standard copying: why it matters in court
Having outlined the imaging process, it is important to understand why forensic-grade imaging is non-negotiable for court-bound evidence. The legal risks of standard copying are significant and often underestimated.
When a file is copied using Windows Explorer or macOS Finder, the operating system automatically updates the “last accessed” timestamp on the original. Metadata changes. File attributes shift. In some cases, the copy itself may not include hidden files, system files, or data in unallocated sectors. That missing data could be the very evidence you need.
| Feature | Forensic imaging | Standard copying |
|---|---|---|
| Bit-for-bit accuracy | Yes | No |
| Metadata preservation | Yes | No |
| Deleted file recovery | Yes | No |
| Hash verification | Yes | No |
| Write-blocked acquisition | Yes | No |
| Court admissibility (UK) | Reliable | Unreliable |
| Chain of custody support | Yes | No |
The legal standards governing safeguarding digital evidence in the UK require that evidence be collected and preserved in a manner that can withstand scrutiny. Key requirements include:
- Evidence must be collected without alteration
- The collection method must be repeatable and verifiable
- A complete audit trail must accompany the evidence
- Tools used must be validated and accepted by the courts
As SWGDE best practices confirm, only properly imaged, validated, and hash-verified evidence is reliably admissible in UK courts. Understanding the chain of custody importance is not optional for any professional handling digital evidence.
The consequences of getting this wrong are severe. Evidence obtained through standard copying has been excluded in UK proceedings, not because the data was fabricated, but because its integrity could not be proven. That is a preventable failure.
Tools and best practices for effective forensic imaging
With the differences made clear, being properly equipped and compliant is the next critical step. The right tools, used correctly, are what separate admissible evidence from inadmissible data.
| Tool | Developer | Validation status |
|---|---|---|
| FTK Imager | Exterro (formerly AccessData) | Court-accepted, widely validated |
| EnCase Forensic | OpenText | Court-accepted, industry standard |
| dd / dcfldd | Open source | Accepted with proper documentation |
| Guymager | Open source | Accepted in many jurisdictions |
| Cellebrite UFED | Cellebrite | Accepted for mobile device imaging |
As forensic acquisition principles confirm, FTK Imager and EnCase are considered court-accepted standards in the UK, and their use is strongly recommended where available. Choosing an unvalidated tool introduces unnecessary risk.
Beyond tool selection, best practices for forensic imaging include:
- Always use write blockers: Hardware write blockers are preferred over software equivalents for maximum reliability
- Document everything in real time: Notes made after the fact are far more vulnerable to challenge than contemporaneous records
- Store images on verified clean media: Confirm destination drives are forensically wiped before use
- Maintain access controls: Limit who can access the forensic image and log every instance of access
Common pitfalls that undermine forensic imaging include using consumer-grade software, failing to document the imaging environment, skipping hash verification, and neglecting to update tool validation records. Reviewing key forensic imaging tools and their current validation status should be part of every practitioner’s routine.
Pro Tip: Always update your tool validation procedures in line with current SWGDE guidance. Courts increasingly scrutinise whether the version of the tool used was the validated version at the time of acquisition, not just whether the tool itself is generally accepted.
Why context matters: not all forensic imaging is equal
Procedures and tools matter enormously, but there is a subtler issue that experienced practitioners must confront: the word “forensic imaging” does not mean the same thing to everyone in a courtroom.
We have seen cases where confusion between digital forensic imaging and radiological forensic imaging has caused unnecessary delays and credibility challenges. As SWGDE highlights, radiological forensic imaging focuses on medical and photogrammetric evidence, an entirely separate discipline with different standards, different practitioners, and different evidentiary frameworks. When a legal professional uses the term loosely, it creates openings for challenge.
Beyond terminology, there is a broader principle at work. Not every forensic image is created equal, even within digital investigations. An image acquired without a write blocker, or verified with only one hash algorithm, or documented inconsistently, is technically a forensic image but practically a liability. The rigour of the process determines the robustness of the evidence.
Our view, formed through years of casework, is that the most dangerous assumption in digital forensics is that following the steps is enough. The steps must be followed correctly, completely, and in a manner that can be explained clearly to a judge or jury. Compliance is not a checklist. It is a discipline.
Need help with forensic imaging or digital evidence collection?
If you are managing a case where digital evidence must hold up in court, the margin for error is zero. At Computer Forensics Lab, we provide court-ready forensic imaging and digital forensics services for legal professionals, law enforcement, and corporate clients across the UK. Our team follows SWGDE-compliant protocols, uses validated tools, and produces expert witness reports that withstand cross-examination. Whether you need a single device imaged or support for a complex multi-device investigation, we are equipped to assist. Understanding how digital forensics data is collected and preserved is the first step. Taking action with qualified experts is the next.
Frequently asked questions
How is forensic imaging different from making a normal copy?
Forensic imaging creates a verified, bit-for-bit copy using write-blocking and hash verification for a true match, whereas normal copying alters metadata and cannot confirm data completeness for court purposes.
What are the main steps in the forensic imaging process?
The critical steps are device documentation, write-blocked acquisition using validated tools, hash generation, and formal recording of the chain of custody, all of which SWGDE mandates as minimum standards.
Which forensic imaging tools are accepted in UK courts?
FTK Imager and EnCase are the most widely recognised court-accepted imaging tools in the UK, with verified hash outputs ensuring a 100% bit-match.
Does forensic imaging ever refer to medical scans?
In specialist medical and post-mortem contexts, yes, but for legal and cyber investigations the term refers exclusively to digital disk imaging, as SWGDE clarifies when distinguishing radiological from digital forensic imaging.