Mobile phone evidence is fragile and easily compromised without strict forensic protocols. Legal professionals across the UK must understand both technical and procedural aspects to preserve data properly whilst maintaining court admissibility. This guide details best practice mobile forensics steps compliant with UK standards, ensuring reliable evidence collection for litigation and criminal investigations.
Table of Contents
- Prerequisites: Legal And Technical Essentials Before You Start
- Step 1: Forensic Preparation And Tool Validation
- Step 2: Device Isolation And Data Acquisition Protocols
- Step 3: Data Analysis Procedures For Evidential Relevance
- Step 4: Chain Of Custody And Documentation Standards
- Step 5: Common Mistakes, Troubleshooting, And Corrective Actions
- Step 6: Expected Timelines, Costs, And Outcomes
- Enhance Your Legal Investigations With Expert Digital Forensics
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Legal authorisation | Obtain explicit legal authorisation or written consent before examination to ensure evidence admissibility in UK courts. |
| Device isolation | Effective device isolation using Faraday bags prevents data loss through remote wiping in up to 30% of cases. |
| Chain of custody | Maintaining meticulous chain of custody with tamper-evident seals mandatory in 100% of forensic cases ensures court admissibility. |
| Validated tools | Use only court-approved forensic imaging software and write-blockers to prevent data alteration during acquisition. |
| Timeline expectations | Examinations typically require 3 to 7 days with costs ranging between £1,000 and £3,000 per device examined. |
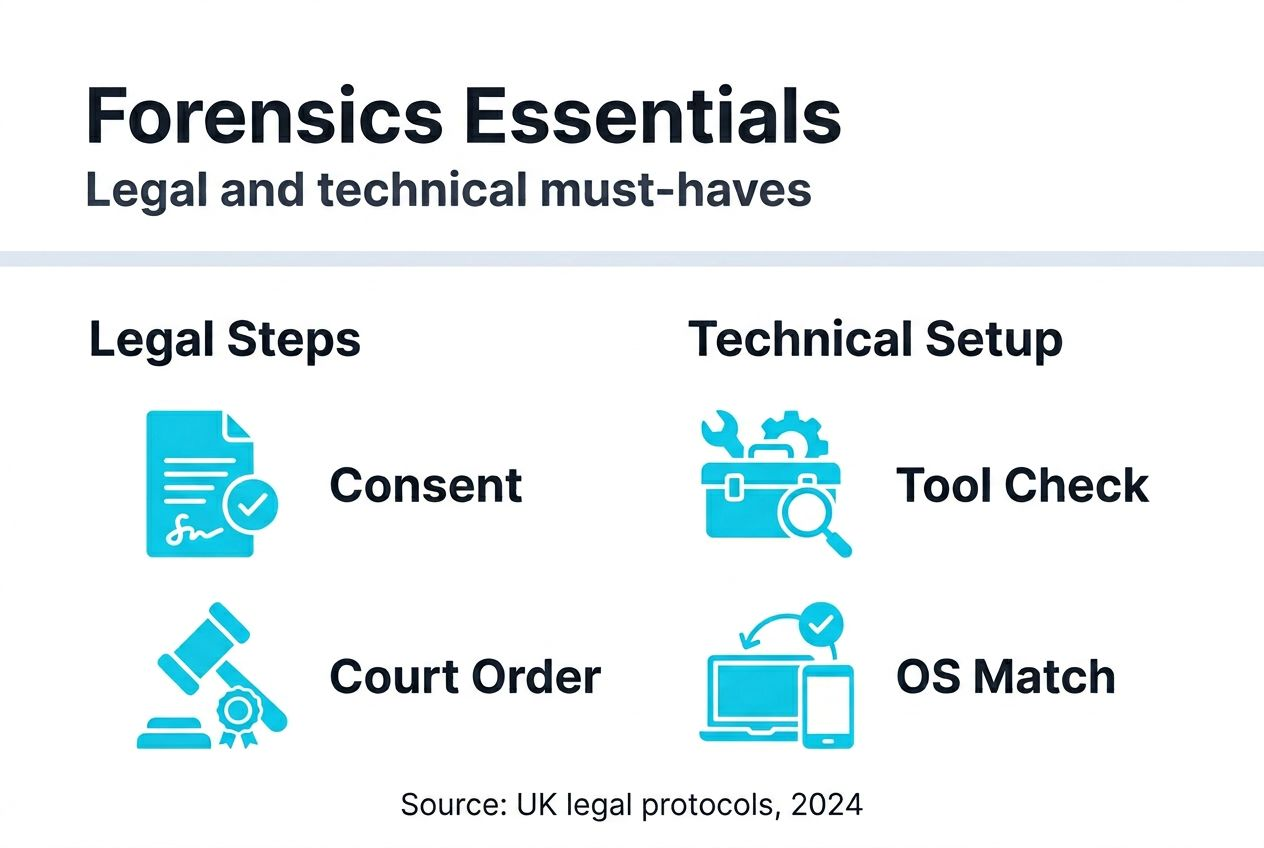
Prerequisites: legal and technical essentials before you start
Before commencing any mobile phone forensic examination, legal professionals must establish both legal authority and technical readiness. Proper preparation ensures lawful, ethical, and technically sound investigations that withstand court scrutiny.
Obtain explicit legal authorisation or written consent before examination. Evidence collected without proper authority faces inadmissibility challenges in UK courts. Understanding legal considerations in UK forensics is essential for maintaining compliance with data privacy laws and forensic ethics.
Prepare and assemble validated forensic hardware and software before handling any device:
- Court-approved forensic imaging tools compatible with target mobile operating systems
- Validated write-blockers and forensic imaging software for bit-for-bit data duplication
- Faraday bags for immediate device isolation from wireless signals
- Encrypted storage devices for secure data transfer and preservation
- Comprehensive documentation templates for chain of custody recording
Ensure compatibility between forensic tools and target mobile OS versions, whether Android or iOS. Version mismatches can result in failed extractions or incomplete data recovery. Testing tools in controlled environments before live cases prevents technical failures during critical investigations.
Pro Tip: Maintain a forensic toolkit checklist and verify all equipment functionality weekly to avoid delays when time-sensitive examinations arise.
Step 1: forensic preparation and tool validation
Assembling and validating forensic tools before handling any mobile device establishes the foundation for data integrity throughout the examination process. Thorough preparation prevents contamination and ensures reliable, court-admissible evidence.
Use only court-approved forensic imaging software that creates accurate bit-for-bit copies of mobile data. These tools must be regularly updated to maintain compatibility with evolving mobile operating systems and security features. Software validation through independent testing organisations provides credibility in legal proceedings.
Employ write-blockers rigorously during all data acquisition phases. These devices prevent any modification to original evidence whilst allowing forensic examiners to read and copy data. Validated write-blockers ensure zero data modification during extraction processes.
Test compatibility of forensic tools with specific mobile OS versions before commencing examinations:
- Verify tool certification for target Android versions (13, 14, 15)
- Confirm iOS compatibility with latest security updates
- Document all tool version numbers and validation dates
- Maintain logs of successful test acquisitions in controlled environments
Prepare controlled, secure forensic environments to prevent contamination or external interference. Dedicated examination rooms with restricted access, electromagnetic shielding, and climate control protect evidence integrity. Physical security measures complement technical safeguards.
Pro Tip: Create standardised validation reports for each forensic tool, documenting test results, accuracy metrics, and compatibility confirmations for court presentation.
Explore comprehensive mobile device forensics guidance for detailed tool selection and validation procedures tailored to UK legal requirements.
Step 2: device isolation and data acquisition protocols
Immediate device securing prevents data loss whilst proper acquisition techniques ensure forensic reliability. These protocols form the critical bridge between evidence seizure and analysis.
Place seized devices immediately in Faraday bags to block all wireless signals. Remote wiping commands, incoming messages, or network synchronisation can alter or destroy evidence within seconds. Failing to isolate devices immediately results in data loss in up to 30% of cases.
Document device condition thoroughly upon seizure. Comprehensive recording includes high-resolution photographs showing physical state, screen condition, battery level, and any visible damage. Written logs must capture device make, model, IMEI numbers, and operational status at time of seizure.
Choose the appropriate acquisition method based on case requirements and device characteristics:
- Assess case complexity and required data depth
- Select logical extraction for rapid access to active data and communication records
- Deploy physical extraction for comprehensive recovery including deleted files and system data
- Implement advanced techniques for encrypted or locked devices requiring specialised tools
- Cross-verify extraction results using multiple forensic platforms
| Acquisition Method | Data Scope | Typical Duration | Best Use Cases |
|---|---|---|---|
| Logical extraction | Active files, messages, contacts | 2-4 hours | Straightforward cases requiring quick access to communications |
| Physical extraction | Full device image, deleted data, system files | 6-12 hours | Complex investigations requiring comprehensive data recovery |
| Advanced recovery | Encrypted data, locked devices, damaged hardware | 24-72 hours | High-value cases with technical obstacles or evidence destruction attempts |
Cross-verify extraction results by deploying multiple forensic tools in parallel. Different platforms may recover varying data sets due to algorithm differences and compatibility variations. Comparing outputs ensures comprehensive data capture and identifies potential gaps.
Pro Tip: Maintain devices in aeroplane mode if Faraday bags are unavailable, though this provides inferior protection compared to proper electromagnetic shielding.
Detailed mobile device analysis steps provide additional protocols for complex acquisition scenarios.
Step 3: data analysis procedures for evidential relevance
Raw extracted data requires systematic analysis to identify legally relevant evidence and establish reliability for court presentation. Meticulous interpretation separates meaningful findings from digital noise.
Analyse communication logs comprehensively to reconstruct timelines and establish evidential patterns. Instant messaging applications, SMS records, email correspondence, and call histories reveal relationships, intentions, and sequences of events. GPS metadata and timestamp analysis corroborate physical locations and temporal frameworks critical to legal arguments.
Use multiple forensic software solutions in parallel to cross-verify artefacts and interpretations. Different analysis platforms employ varying algorithms and recovery techniques, potentially revealing evidence missed by single-tool approaches. Concordance between multiple tools strengthens reliability and defensibility of findings.
Search for deleted, encrypted, or fragmented data through specialised recovery procedures:
- Deploy carving techniques to recover deleted files from unallocated storage space
- Apply decryption tools to protected data stores where legally authorised
- Reconstruct fragmented records scattered across device memory
- Analyse application-specific databases for hidden or archived communications
Maintaining tamper-evident evidence bags and secure lab environments significantly reduces contamination risks during analysis phases. Controlled access and environmental monitoring protect evidence integrity throughout examination processes.
Compile detailed findings including data origins, recovery methods, and reliability assessments. Documentation must explain technical procedures in plain language suitable for legal professionals without forensic expertise. Clear reporting bridges the gap between technical analysis and courtroom presentation.
Comprehensive mobile device analysis guidance supports thorough evidence interpretation and reporting standards.
Step 4: chain of custody and documentation standards
Maintaining unbroken chain of custody from seizure through court presentation ensures evidence admissibility and withstands defence challenges. Documentation rigor separates professional forensics from amateur investigations.
Record every individual who handles evidence with precise timestamps and descriptions of actions taken. Chain of custody logs must capture date, time, person, purpose, and location for each transfer or examination event. Gaps or ambiguities in custody records provide grounds for evidence exclusion.
Use tamper-evident bags for physical storage of devices and extracted data media. These specialised containers display visible signs of unauthorised access attempts. Secure, controlled storage environments with restricted access, surveillance monitoring, and environmental controls protect evidence from physical and digital threats.
Maintain both physical and digital detailed logs throughout the forensic process:
- Photographic documentation of device condition at each handling stage
- Written notes describing examination procedures and observations
- Digital audit trails from forensic software showing all actions performed
- Witness signatures confirming transfers and storage events
Documentation must be clear, uninterrupted, and audit-ready to withstand court scrutiny. Tamper-evident seals are mandatory in 100% of forensic cases to ensure evidence integrity meets legal standards. Any break in custody or inadequate documentation invites admissibility challenges.
Pro Tip: Implement digital timestamping and cryptographic hashing of evidence files to provide mathematical proof of data integrity throughout storage and analysis phases.
Detailed chain of custody preservation protocols ensure compliance with UK legal requirements and international forensic standards.
Step 5: common mistakes, troubleshooting, and corrective actions
Recognising frequent errors in mobile phone forensics enables legal professionals to avoid evidence compromise and implement corrective measures when problems arise. Prevention and early detection protect case outcomes.
Neglecting immediate device isolation remains a critical error. Data loss occurs in up to 30% of cases when devices remain connected to networks. Remote wiping commands or synchronisation events can destroy evidence within seconds. Always deploy Faraday bags immediately upon seizure.
Inadequate chain of custody documentation jeopardises evidence admissibility:
- Missing timestamps or handler signatures create exploitable gaps
- Vague action descriptions fail to establish proper handling
- Incomplete transfer records suggest potential tampering opportunities
- Absence of photographic evidence weakens integrity claims
Employing non-validated forensic tools risks data corruption and legal challenges. Courts increasingly scrutinise tool reliability and validation status. Only use accredited hardware and software with documented testing and certification. Unvalidated tools produce questionable results that defence experts can easily discredit.
Failing to obtain prior legal authorisation before analysis risks evidence exclusion and potential legal liability. Written consent from device owners or valid court orders must precede any forensic examination. Proceeding without authorisation violates privacy laws and professional ethics.
Pro Tip: Implement pre-examination checklists covering authorisation verification, tool validation confirmation, and isolation protocol completion to prevent procedural errors.
Explore mobile device investigation tips for additional troubleshooting guidance and error prevention strategies.
Step 6: expected timelines, costs, and outcomes
Realistic expectations regarding investigation duration, financial investment, and typical results enable effective case planning and client communication. Understanding forensic economics supports informed decision making.
Typical forensic examinations require 3 to 7 days depending on complexity, device condition, and extraction methods deployed. Simple logical extractions of cooperative devices may complete within 48 hours. Complex physical extractions involving damaged hardware, encryption, or extensive data volumes can extend beyond one week.
Costs in UK forensic laboratories typically range between £1,000 and £3,000 per device examined. Pricing variation reflects case complexity, urgency requirements, and specialised techniques necessary for particular devices or data types.
| Service Component | Typical Cost Range | Duration |
|---|---|---|
| Initial consultation and case assessment | £200-£400 | 1-2 hours |
| Logical data extraction | £800-£1,200 | 1-2 days |
| Physical data extraction | £1,500-£2,500 | 3-5 days |
| Advanced recovery (encrypted/damaged devices) | £2,000-£4,000 | 5-10 days |
| Expert witness report preparation | £500-£1,000 | 2-3 days |
| Court testimony (per day) | £1,200-£2,000 | As required |
Most recoverable data includes call logs, SMS and MMS messages, instant messaging application data, email correspondence, browsing history, GPS location metadata, photographs, videos, and application-specific content. Deleted data recovery success depends on time elapsed since deletion and subsequent device usage.
Proper forensic processes ensure evidence withstands legal scrutiny in UK courts. Adherence to established protocols, validated tools, and comprehensive documentation creates defensible evidence that survives cross-examination and admissibility challenges.
Understand the full benefits of mobile forensics for litigation support and investigation success.
Enhance your legal investigations with expert digital forensics
Navigating mobile phone forensics requires specialised expertise, validated tools, and strict adherence to UK legal standards. Our team specialises in court-admissible mobile phone forensic analysis supporting litigation, criminal investigations, and regulatory compliance matters.
We employ only validated forensic tools, maintain rigorous chain of custody protocols, and deliver comprehensive expert reports tailored for legal proceedings. Our London-based laboratory provides secure examination environments and experienced analysts familiar with UK evidentiary requirements.
Explore our comprehensive digital forensics services, specialised mobile phone forensics capabilities, and digital evidence solutions designed for legal professionals requiring reliable, defensible evidence.
Frequently asked questions
What legal authorisations are needed for mobile phone forensic examinations in the UK?
Written consent from the device owner or a valid court order is required before forensic examination begins. This ensures compliance with UK legal authorisation requirements and protects evidence admissibility. Proceeding without proper authority violates data privacy laws and risks evidence exclusion.
How can remote wiping risks be prevented after seizing a mobile device?
Place the device immediately in a Faraday bag to block all wireless signals, preventing remote wiping or interference. Document seizure details meticulously to maintain evidence integrity. Proper device isolation techniques are essential for preserving volatile digital evidence.
What are the primary differences between logical and physical data extraction in mobile forensics?
Logical extraction captures active, accessible data quickly but may miss deleted or hidden files. Physical extraction retrieves a complete bit-for-bit copy, including deleted and fragmented data, though requiring more time and technical complexity. Choose methods based on case requirements and evidential needs, as detailed in logical versus physical extraction guidance.
How should legal professionals maintain chain of custody to ensure evidence is admissible?
Record every transfer and handling event with time-stamped logs and photographic evidence. Use tamper-evident bags and secure storage facilities to prevent contamination or alteration. Comprehensive chain of custody maintenance protocols ensure evidence withstands courtroom scrutiny and admissibility challenges.