In March 2025, Capita suffered a cyberattack that compromised personal data belonging to 6.6 million individuals, resulting in a £14 million ICO penalty. This incident demonstrates how the absence of robust digital forensics capabilities can lead to catastrophic financial and reputational damage. Many UK business leaders still perceive digital forensics as a reactive measure, deployed only after a breach occurs. However, in 2026, digital forensics serves as both a proactive defence mechanism and a critical response tool. This article explains why integrating digital forensics into your business strategy is essential for cyber incident response, regulatory compliance, and long-term operational resilience.
Table of Contents
- Understanding Digital Forensics And Its Role In Business
- Financial And Legal Consequences Of Neglecting Digital Forensics
- Challenges Uk Businesses Face In Implementing Effective Digital Forensics
- Practical Steps For Uk Businesses To Integrate Digital Forensics Effectively
- Discover Reliable Digital Forensics Solutions
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Rapid breach response | Digital forensics enables swift incident detection and containment, minimising data loss and meeting GDPR reporting deadlines. |
| Compliance protection | Forensic capabilities help businesses avoid regulatory fines that can reach 4% of global turnover under UK GDPR. |
| Cost reduction | Forensic readiness lowers investigation expenses by up to 30% and reduces overall incident impact. |
| Resource challenges | National staffing shortages and forensic backlogs create delays that businesses must address proactively. |
| Proactive value | Digital forensics is not merely post-breach investigation; it strengthens defences and informs security strategy. |
Understanding digital forensics and its role in business
Digital forensics involves the systematic collection, preservation, and analysis of digital evidence from computing devices, mobile phones, cloud platforms, and networks. This discipline serves two distinct but interconnected functions for businesses. Reactive forensics investigates incidents after they occur, uncovering how breaches happened and identifying perpetrators. Proactive forensic readiness prepares organisations to respond swiftly when incidents arise, reducing damage and investigation costs.
Businesses deploy digital forensics across multiple scenarios. Corporate fraud and misconduct investigations rely on forensic analysis to trace financial irregularities and employee malfeasance. Data breach investigations determine the scope of compromised information and identify vulnerabilities. Legal disputes require forensic evidence to support claims related to intellectual property theft, contract violations, or employment disputes. Each application demands rigorous methodology to ensure evidence integrity and admissibility.
Forensic readiness transforms digital forensics from a reactive expense into a strategic asset. Organisations with established forensic capabilities can preserve volatile data immediately, maintain chain of custody documentation, and respond to incidents within regulatory timeframes. This preparedness reduces the window of opportunity for attackers and limits the spread of compromised data.
Many decision makers mistakenly view digital forensics as relevant only after a breach has been discovered. This misconception leads to delayed responses, lost evidence, and increased regulatory penalties. In reality, forensic readiness encompasses policy development, staff training, logging configurations, and incident response planning. These proactive measures enable businesses to pivot quickly when threats materialise.
Key forensic applications for businesses:
- Detecting insider threats through user activity analysis
- Investigating ransomware attacks to determine entry points
- Supporting litigation with admissible digital evidence
- Analysing malware to understand attack vectors
- Recovering deleted or encrypted data for business continuity
Pro Tip: Implement automated logging for critical systems now, before an incident occurs. Volatile data can be lost within minutes if not captured immediately, rendering investigations incomplete and compliance efforts futile.
Financial and legal consequences of neglecting digital forensics
The Capita breach illustrates the severe financial impact of inadequate digital forensics capabilities. The £14 million ICO fine followed an investigation that revealed deficiencies in security measures and incident response. Beyond regulatory penalties, Capita faced substantial costs for breach notification, credit monitoring services, legal fees, and remediation efforts. The reputational damage eroded client confidence and triggered contract reviews across its customer base.
UK GDPR imposes strict obligations on organisations experiencing personal data breaches. Controllers must report certain breaches within 72 hours of becoming aware of them, with penalties reaching up to 4% of annual global turnover for non-compliance. Without forensic capabilities, businesses struggle to assess breach scope, identify affected individuals, and meet reporting deadlines. This regulatory framework makes digital forensics essential for legal compliance, not optional.
| Cost Category | Without Digital Forensics | With Forensic Readiness |
|---|---|---|
| Investigation duration | 4-6 months | 2-3 months |
| Evidence collection | Incomplete, delayed | Systematic, timely |
| Regulatory fines | High risk (up to 4% turnover) | Reduced risk through compliance |
| Operational disruption | Extended downtime | Faster recovery |
| Legal exposure | Increased litigation costs | Defensible evidence chain |
Personal data at risk during breaches includes names, addresses, financial information, and identification numbers. Special category data such as health records, biometric data, and criminal history carries heightened protection requirements under UK GDPR. Breaches involving special category data trigger more severe regulatory scrutiny and higher potential fines. Businesses handling such information must implement robust forensic capabilities to demonstrate accountability and due diligence.
Pro Tip: Early incident detection through forensic monitoring reduces the volume of compromised data. Studies show that organisations detecting breaches within the first 30 days experience significantly lower financial impact than those with prolonged exposure.
“Digital forensics provides value far beyond evidence collection. It enables organisations to understand attack patterns, strengthen defences, and demonstrate regulatory compliance. Without these capabilities, businesses operate blindly in an increasingly hostile threat landscape.”
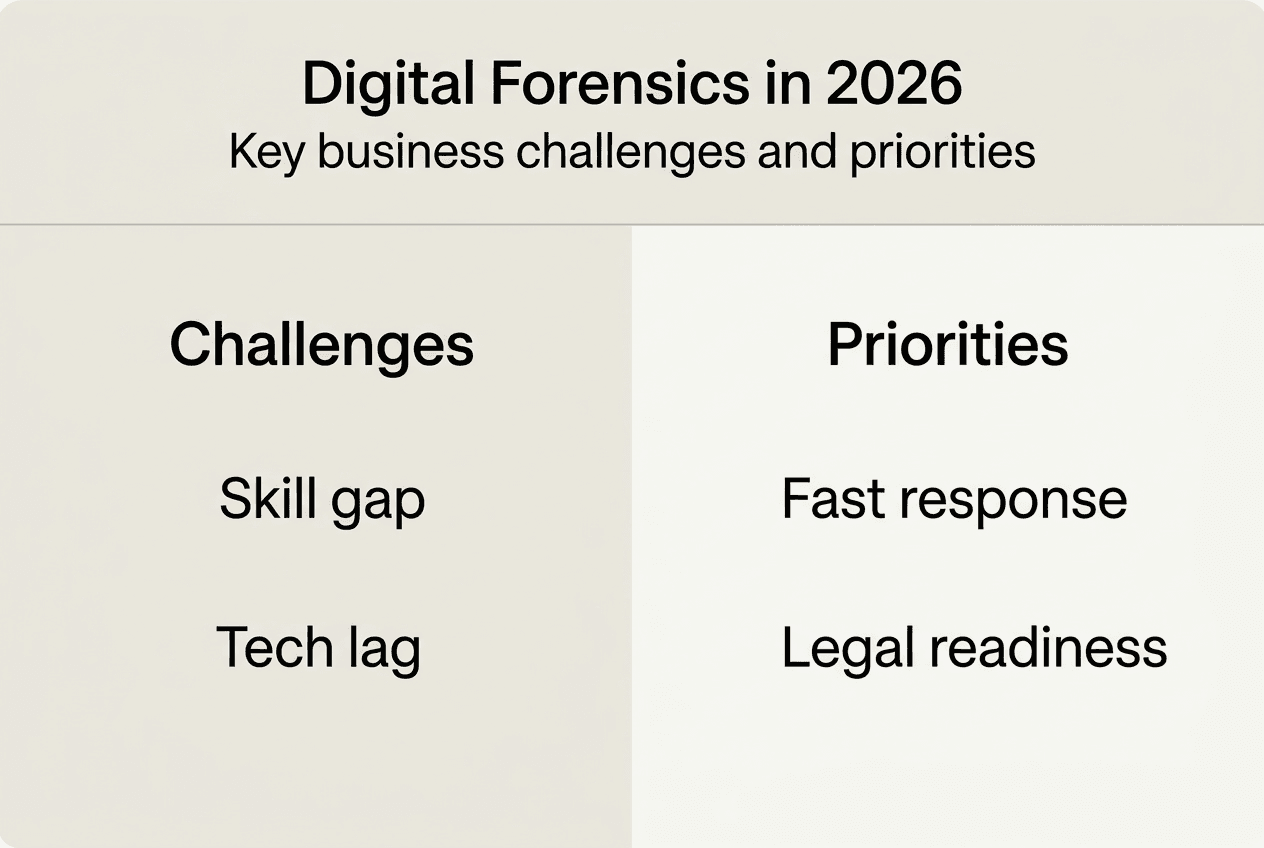
Challenges UK businesses face in implementing effective digital forensics
Digital forensics teams across the UK face overwhelming workloads and staffing shortages that impede timely investigations. Police forces report varying backlogs, with some waiting months to analyse seized devices. This resource constraint extends beyond law enforcement, affecting private sector organisations that struggle to recruit qualified forensic analysts. The skills gap creates delays in incident response, allowing threats to persist and damage to accumulate.
Technological evolution compounds these challenges. Forensic tools lag behind as attackers adopt encryption, cloud platforms, and sophisticated malware. Analysts must continuously update their expertise to handle emerging storage formats, operating systems, and communication applications. This constant adaptation requires investment in training and tools that many organisations cannot sustain.
Forensic backlogs create uneven access to investigative resources across UK regions. Businesses in areas with overburdened forensic services face longer wait times for evidence analysis, delaying legal proceedings and regulatory responses. This disparity places organisations at risk of non-compliance through no fault of their own, highlighting the need for corporate investigation capabilities independent of public sector resources.
Common forensic challenges organisations encounter:
- Insufficient budget allocation for forensic tools and training
- Lack of documented incident response procedures
- Poor logging configurations that fail to capture critical evidence
- Inadequate chain of custody protocols
- Limited understanding of forensic requirements among senior leadership
- Difficulty retaining skilled forensic analysts due to competitive market
Strategies to mitigate forensic implementation challenges:
- Partner with specialist forensic providers to access expertise without maintaining full in-house teams.
- Establish forensic readiness policies that define roles, responsibilities, and escalation procedures before incidents occur.
- Invest in automated forensic tools that reduce manual analysis time and capture evidence continuously.
- Conduct regular tabletop exercises to test incident response plans and identify gaps in forensic capabilities.
- Allocate dedicated budget for forensic training and tool updates to keep pace with technological change.
- Implement centralised logging systems that aggregate data from across the IT environment for efficient analysis.
“The forensic resource crisis demands urgent attention. Businesses cannot afford to wait for public sector capacity to expand. Proactive investment in forensic readiness and strategic partnerships with specialist providers are essential for maintaining operational resilience and regulatory compliance.”
Practical steps for UK businesses to integrate digital forensics effectively
Forensic readiness establishes the policies, procedures, and technical controls needed to respond effectively when incidents occur. This framework enables organisations to collect evidence systematically, maintain its integrity, and minimise investigation costs. Research indicates that forensic readiness reduces investigation costs by 30% compared to reactive approaches. The investment in preparation pays dividends through faster recovery, reduced regulatory exposure, and stronger legal positioning.
| Aspect | Forensic Readiness | Reactive Forensics |
|---|---|---|
| Evidence collection | Pre-configured, automated | Manual, delayed |
| Investigation timeline | Days to weeks | Weeks to months |
| Cost efficiency | Lower per incident | Higher due to urgency |
| Regulatory compliance | Proactive demonstration | Reactive scramble |
| Business disruption | Minimised through planning | Extended through uncertainty |
Incident response plans must integrate digital forensics at every stage. Initial detection triggers evidence preservation protocols that capture volatile memory, network traffic, and system logs before they disappear. Containment procedures isolate affected systems while maintaining forensic integrity. Analysis phases leverage forensic tools to determine breach scope, identify attack vectors, and assess data exposure. Recovery incorporates forensic findings to remediate vulnerabilities and prevent recurrence.
Essential components of forensic-ready incident response:
- Designated forensic lead with authority to preserve evidence and coordinate investigations
- Pre-approved legal and forensic service providers for rapid engagement
- Evidence handling procedures that maintain chain of custody documentation
- Communication protocols that balance transparency with legal privilege
- Post-incident review processes that capture lessons learned and update defences
Pro Tip: Volatile data preservation must occur within minutes of incident discovery. Configure automated tools to capture memory dumps and network connections immediately, as 60% of volatile data can be lost if not preserved promptly.
Selecting forensic service providers requires careful evaluation of technical capabilities, industry experience, and regulatory knowledge. Look for providers with relevant certifications, proven methodologies, and experience handling cases similar to your business context. Establish relationships before incidents occur, negotiating retainer agreements that guarantee rapid response when needed. This preparation eliminates delays associated with procurement processes during crises.
Compliance checkpoints linked to forensic readiness:
- Data protection impact assessments that identify forensic requirements
- Breach notification procedures aligned with UK GDPR timelines
- Records of processing activities that document evidence handling
- Staff training programmes covering forensic evidence preservation
- Regular audits of logging configurations and retention policies
Businesses should view professional digital forensics services as strategic partners rather than vendors. Effective collaboration requires clear communication about business priorities, risk tolerance, and regulatory obligations. Providers should offer guidance on forensic readiness, conduct regular capability assessments, and support continuous improvement. This partnership model ensures forensic capabilities evolve alongside cyber incident response needs and emerging threats.
Discover reliable digital forensics solutions
Navigating the complex landscape of cyber threats and regulatory requirements demands expertise and proven methodologies. Computer Forensics Lab provides digital forensics services tailored to UK businesses facing data breaches, corporate investigations, and compliance challenges. Our team delivers rapid digital forensic investigations that uncover critical evidence whilst maintaining chain of custody standards required for legal proceedings. We help organisations develop forensic readiness frameworks, respond to incidents within regulatory timeframes, and strengthen defences against evolving threats. Explore how our digital forensics data solutions can protect your business from the financial and reputational consequences of inadequate incident response.
Frequently asked questions
Why is digital forensics crucial for timely breach response?
Digital forensics provides the rapid, accurate insights needed to contain incidents within UK GDPR’s 72-hour reporting deadline. Without forensic capabilities, businesses struggle to assess breach scope and identify affected individuals, risking regulatory penalties.
How does forensic readiness reduce investigation costs?
Forensic readiness establishes pre-configured systems and documented procedures that enable efficient evidence collection. This preparation reduces investigation costs by 30% compared to reactive approaches that require urgent resource mobilisation.
What types of cyber incidents benefit most from forensic analysis?
Data breaches, insider threats, corporate fraud, ransomware attacks, and malware infections all require forensic analysis for clarity. Each incident type demands systematic evidence collection to determine scope, identify perpetrators, and support remediation efforts.
How do digital forensic backlogs affect businesses?
Backlogs delay incident resolution, increasing potential damage and regulatory risks. Businesses waiting for overburdened public sector resources face extended exposure to threats and may miss compliance deadlines for breach notification.
Can digital forensics prevent future cyber threats?
Yes, forensic analysis uncovers attack methods, identifies vulnerabilities, and reveals patterns that inform stronger defences. Organisations that integrate forensic findings into security strategies reduce the likelihood and impact of subsequent incidents.