TL;DR:
- Modern investigative interviewing emphasizes rapport, cognitive techniques, and evidence-based methods for legal robustness.
- Preparation involves thorough evidence review, strategic questioning, and adapting techniques for vulnerable witnesses.
- Using science-based methods like SUE and cognitive interviews increases accuracy and reduces legal liability compared to traditional adversarial approaches.
Digital evidence now shapes the outcome of nearly every serious criminal and civil investigation, yet the interview techniques used to contextualise that evidence have not always kept pace. When a practitioner applies outdated, adversarial questioning to a suspect or witness whose digital footprint has already been mapped, the results can be catastrophic: false confessions, inadmissible statements, and collapsed prosecutions. The gap between what the forensic data shows and what an interview can reliably extract is where cases are won or lost. This article provides legal professionals and law enforcement personnel with advanced, science-backed interviewing techniques designed specifically for digital forensics contexts.
Table of Contents
- Key principles of effective investigative interviewing
- Preparing for digital forensics interviews: Tools and techniques
- Step-by-step guide: Conducting advanced digital forensic interviews
- Adapting interview techniques for vulnerable witnesses and digital evidence
- Quality assurance and post-interview verification in digital investigations
- Why modern science-based interviewing is crucial for legal defensibility
- Expert digital forensics solutions for your investigative needs
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Build rapport first | Establishing trust from the outset is crucial for accurate and defensible interview outcomes. |
| Maximise information with cognitive techniques | Using cognitive interview pillars increases reliable recall by up to 50 percent. |
| Integrate evidence strategically | Applying the SUE method boosts deception detection and streamlines digital fact-checking. |
| Adapt for vulnerable populations | Special protocols and trauma-aware strategies are vital for children and adults with mental health needs. |
| Verify and document | Robust post-interview verification ensures legal defensibility in digital forensics investigations. |
Key principles of effective investigative interviewing
Before a single question is asked, the foundational principles of modern investigative interviewing must be firmly in place. The shift away from accusatorial models towards structured, evidence-informed approaches is not merely an academic preference; it is a practical necessity for producing legally defensible outcomes.
Rapport is the bedrock. Witnesses and suspects who feel psychologically safe provide more detailed, more accurate accounts. Building rapport does not mean being lenient; it means establishing a professional, respectful dynamic that reduces anxiety and encourages disclosure. Simple techniques such as mirroring conversational tone, using the interviewee’s name appropriately, and explaining the interview structure in advance all contribute to a productive environment. Research into legal interview rapport building consistently shows that interviewees who perceive the interviewer as fair are significantly more forthcoming.
Science-based Interviewing (SBI) prioritises rapport-building, cognitive techniques, strategic use of evidence (SUE), and statement-evidence inconsistencies over non-verbal cues for deception detection. This is a critical distinction. Many practitioners still place undue weight on body language as a deception indicator, despite decades of research showing it performs at little better than chance. SBI replaces this unreliable heuristic with structured, evidence-anchored questioning.
| Approach | Method | Reliability | Legal defensibility |
|---|---|---|---|
| Accusatorial (Reid Technique) | Confrontational, assumption of guilt | Low to moderate | High risk |
| PEACE model | Non-accusatorial, structured | High | Strong |
| Science-based Interviewing (SBI) | Rapport, cognitive, SUE | Very high | Very strong |
Aligning your interview practice with digital forensics best practices from the outset ensures that the interview process complements rather than undermines the forensic evidence already gathered.
“The most effective investigative interviews are not interrogations; they are structured conversations guided by evidence, designed to elicit accurate information rather than confirm pre-existing assumptions.”
Pro Tip: Document your rapport-building phase. If a case reaches court, demonstrating that the interviewee was treated fairly and professionally from the outset strengthens the admissibility of any statement obtained.
Preparing for digital forensics interviews: Tools and techniques
With principles in place, proper preparation ensures you have everything needed for a robust interview process. Preparation is where most interviews are actually won or lost, long before the recording begins.
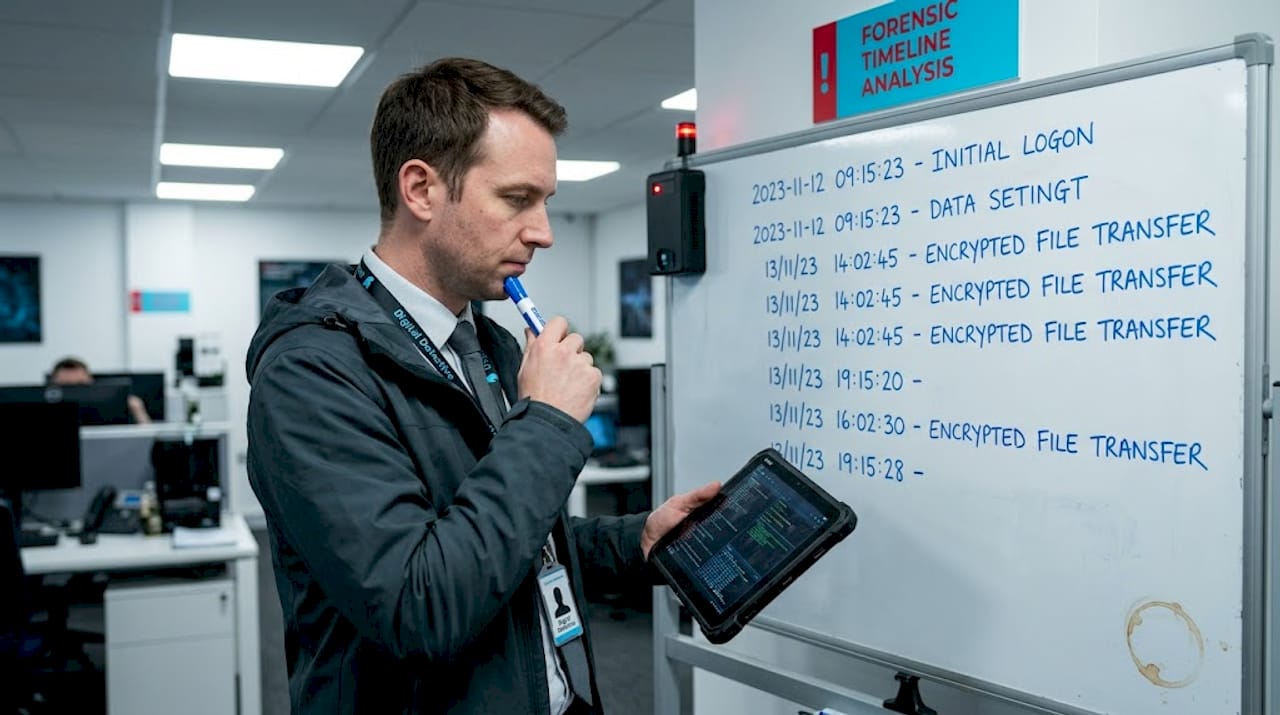
The preparation phase must include a thorough review of all available digital evidence: device logs, metadata, communication records, cloud storage activity, and social media data. Understanding the precise timeline of digital events allows you to construct a questioning framework that probes specific gaps or inconsistencies without revealing your hand prematurely. Legal boundaries must also be confirmed: jurisdiction, applicable legislation, and any special measures required for the interviewee.
Critical preparation steps include:
- Evidence mapping: Catalogue all digital artefacts chronologically before the interview
- Legal review: Confirm admissibility requirements and any applicable cautions
- Objective setting: Define what information the interview must produce and what gaps remain
- Environmental preparation: Ensure the interview room is appropriate, recording equipment is tested, and any interpreters or appropriate adults are briefed
- Briefing the team: All personnel present must understand their role and the questioning strategy
Cognitive Interview (CI) techniques, including context reinstatement, timeline reconstruction, change of perspective, and the instruction to report everything, increase accurate information from witnesses by 40% or more compared to standard methods. These are not soft skills; they are empirically validated tools that should be built into your preparation framework.
| Technique | Application context | Primary benefit |
|---|---|---|
| Context reinstatement | Witness interviews, victim statements | Triggers episodic memory |
| Timeline reconstruction | Complex cybercrime, fraud cases | Establishes sequence of digital events |
| Change of perspective | Witness accounts with gaps | Reveals overlooked details |
| Report everything | All interview types | Reduces selective disclosure |
In a complex cybercrime investigation, for example, asking a witness to mentally return to the moment they first noticed unusual account activity, and to describe the physical environment and their emotional state at the time, can unlock peripheral details that corroborate or contradict digital logs. This is context reinstatement in practice, and it is far more productive than a direct “what happened” question.
Reviewing forensics best practice guidance before each interview ensures your preparation aligns with current procedural standards. Additionally, understanding legal data analysis excellence principles helps you frame questions that directly address the evidentiary gaps your forensic analysis has identified.
Pro Tip: Create a written interview plan that maps each question category to a specific piece of digital evidence or evidential gap. This keeps the interview focused and provides a clear record of your methodology if challenged in court.
Step-by-step guide: Conducting advanced digital forensic interviews
Prepared with the right resources, here is how to execute high-impact interviews that maximise accuracy and legal robustness.
1. Opening and ground rules
Begin by explaining the interview structure, the recording process, and the interviewee’s rights. Establish the expectation that they should tell you everything they can remember, even if it seems irrelevant, and that it is acceptable to say “I don’t know” or “I can’t remember.” This reduces the pressure to confabulate (fill memory gaps with plausible but inaccurate information).
2. Free narrative recall
Invite the interviewee to provide an uninterrupted account of the relevant events. Do not interrupt, prompt, or react visibly. This phase is critical because it establishes a baseline account against which digital evidence can later be compared.
3. Cognitive probing
Using the CI techniques prepared in advance, probe specific elements of the narrative. Ask the interviewee to revisit particular moments, describe sensory details, or consider the sequence of events from a different vantage point. This phase often produces the most forensically valuable detail.
4. Strategic evidence introduction
This is where Strategic Use of Evidence (SUE) becomes decisive. SUE involves early free recall followed by targeted questions without immediate disclosure, achieving 85% deception detection accuracy in trained police officers compared to 56% in untrained officers. Rather than confronting the interviewee with a piece of digital evidence immediately, you first elicit their account of the relevant period, then introduce the evidence to probe inconsistencies. This approach prevents the interviewee from tailoring their story to fit what you already know.
5. Targeted evidence-probing
Once free recall is complete, introduce specific digital artefacts: a timestamp, a deleted file, a communication record. Frame questions around these items without signalling their evidentiary significance. For example: “You mentioned you were not online that evening. Can you help me understand this?” followed by reference to the relevant log.
6. Closing and statement review
Summarise the key points of the account and invite the interviewee to correct or add anything. This is also the moment to conduct an initial statement-evidence consistency check, noting any areas requiring further forensic examination.
In digital forensics contexts, investigative interviews should integrate SUE with digital evidence for consistency checks, avoiding early confrontation to prevent adversarial responses. Understanding internet activity investigative steps is particularly valuable when the digital evidence centres on browsing history, IP logs, or online communications.
| Interviewer type | Deception detection accuracy |
|---|---|
| Trained (SUE method) | 85% |
| Untrained | 56% |
Understanding the role of digital forensic investigators in the broader investigation helps interviewers know precisely which digital artefacts carry the most weight and how to sequence their introduction for maximum effect. Gathering effective evidence collection principles from allied legal disciplines also reinforces procedural rigour.
Pro Tip: Avoid introducing digital evidence before the interviewee has completed their free narrative. Premature disclosure allows a sophisticated interviewee to construct a narrative around what you know rather than what actually happened.
Adapting interview techniques for vulnerable witnesses and digital evidence
Even a textbook-perfect interview needs adjustment for special populations and evidence types. Vulnerable witnesses, including children, individuals with mental health conditions, and those who have experienced trauma, require a fundamentally different approach that balances the need for accurate information with legal and ethical obligations.
Open questions produce more accurate recall, but evidence gaps exist for vulnerable interviewees, particularly those with mental health conditions, where best practices may need adaptation. This is an honest acknowledgement that no single protocol fits every situation.
Protocols such as the NICHD guidelines and ChildFirst model are specifically designed for child witnesses. Both emphasise free recall as the primary mechanism for information gathering, with structured follow-up using non-suggestive, open-ended questions. Trauma-aware questioning recognises that a witness’s disclosure may be non-linear, fragmented, or delayed, and that this does not indicate dishonesty.
Best practices for vulnerable witnesses:
- Use age-appropriate or cognitively appropriate language throughout
- Allow extended pauses without filling silence with prompts
- Avoid closed or leading questions, particularly in the early recall phase
- Introduce an appropriate adult or intermediary where required by law
- Use digital evidence as a gentle anchor rather than a confrontational tool (“I’d like to show you something and ask you about it”) when the interviewee’s account has gaps
- Document any adaptations made and the rationale for them
Digital forensic evidence can play a particularly supportive role when interviewing vulnerable witnesses. For example, device usage logs or message timestamps can provide a concrete timeline that helps a witness with memory difficulties orient themselves without being led. Familiarity with top digital forensics techniques enables interviewers to use this evidence constructively rather than as a blunt instrument.
Quality assurance and post-interview verification in digital investigations
After conducting your interviews, rigorous verification is your final safeguard against flawed evidence and procedural challenges.
The post-interview phase is where the interview’s outputs are tested against the forensic record. Statement-evidence crosschecks involve systematically comparing each claim made during the interview against the available digital artefacts. Discrepancies must be documented, investigated further, or flagged for legal review. This is not about catching people out; it is about ensuring the integrity of the evidentiary record.
Field data confirms the value of this approach. Empirical benchmarks show that CI yields 35 to 50% more accurate witness information, SUE boosts deception detection to 85%, and field studies confirm real-world gains without accuracy loss. These are not laboratory curiosities; they are outcomes replicated across operational settings.
Post-interview quality assurance steps:
- Transcription and review: Produce a verbatim transcript and review against the recording for accuracy
- Statement-evidence mapping: Cross-reference each claim against digital artefacts, noting consistencies and gaps
- Legal documentation: Ensure all procedural requirements are met, including appropriate cautions, consent, and chain of custody records
- Debrief: Conduct a structured debrief with the interview team to identify any procedural deviations
- Follow-up forensic requests: Identify any new forensic questions raised by the interview and commission additional analysis where required
- Expert witness preparation: Where the case will proceed to litigation, prepare a clear account of the interview methodology for inclusion in expert witness reports
The corporate investigation impact of thorough post-interview verification cannot be overstated. In commercial disputes involving employee misconduct or intellectual property theft, a single procedural gap in the interview record can undermine an otherwise strong forensic case.
Why modern science-based interviewing is crucial for legal defensibility
Here is an uncomfortable truth that the legal and law enforcement community has been slow to fully absorb: legacy interrogation methods do not just produce unreliable information, they actively create legal liability.
Accusatorial methods risk false confessions, as seen in cases involving coerced homicide interrogations, and the shift to SBI and PEACE is now recommended for legal defensibility. These are not isolated failures. They are systemic outcomes of a methodology that prioritises confession over accuracy. When a practitioner applies psychological pressure, deception, or confrontation in an interview, they are not just risking a false confession; they are potentially tainting every piece of evidence that follows.
The PEACE model, now standard practice in England and Wales, was developed precisely because the consequences of accusatorial interviewing were too costly to ignore. Yet even within PEACE-trained agencies, the principles are sometimes applied superficially, with interviewers reverting to confrontational habits under pressure. SBI takes this further by grounding every technique in empirical research, making the methodology not just procedurally compliant but scientifically defensible.
From our perspective at Computer Forensics Lab, the most significant shift we have observed in serious investigations is the move towards treating the interview as a forensic instrument in its own right, subject to the same standards of rigour as device examination or data recovery. When you approach an interview with the same methodological discipline you would apply to conducting digital forensics, the quality of the resulting evidence improves markedly.
The practical implication is clear: SBI and cognitive interview techniques are no longer optional enhancements. They are a legal and ethical imperative for any practitioner who wants their interview evidence to withstand scrutiny.
Expert digital forensics solutions for your investigative needs
When your investigation requires more than interview technique alone, specialist forensic support can make the difference between evidence that holds and evidence that collapses. At Computer Forensics Lab, we work alongside legal professionals and law enforcement to provide forensic analysis that directly informs and supports the interview process. Whether you need to understand the digital footprints left across devices and platforms, access our full range of digital forensics services, or commission end-to-end digital forensic investigations with expert witness reporting, our London-based team has the technical depth and legal experience to support your case from evidence collection through to court.
Frequently asked questions
What are the main steps in a science-based investigative interview?
Science-based Interviewing follows a clear sequence: build rapport, elicit free recall through open questions, apply cognitive probing, then introduce evidence strategically to check for statement-evidence inconsistencies. Each step is designed to maximise accuracy while maintaining legal defensibility.
Why avoid adversarial confrontation in digital forensic interviews?
Early confrontation triggers defensive responses that reduce information quality and increase the risk of false admissions. Science-based interviewing demonstrates that non-confrontational approaches combined with SUE produce far more reliable and legally robust outcomes.
How much more information does the cognitive interview produce?
Cognitive Interview techniques consistently produce 35 to 50% more accurate information in field studies compared to standard interview methods, making them one of the most evidence-backed tools available to investigative practitioners.
How do I adapt my approach for vulnerable witnesses?
Use free recall first, avoid leading or suggestive questions, and apply structured protocols such as the NICHD and ChildFirst models that are specifically designed for children and those with additional needs, accounting for trauma’s impact on disclosure patterns.
What is the Strategic Use of Evidence technique?
SUE is a structured method where the interviewer withholds known evidence until after the interviewee’s free recall is complete, then introduces it to probe inconsistencies, significantly improving deception detection accuracy compared to immediate disclosure.