Every London digital forensics investigator knows the frustration of staring at a seized device that remains stubbornly unreadable. Encryption transforms evidence from accessible files into mathematical puzzles, complicating the legal and technical process of proving a cybercrime case. Understanding the strengths of algorithms like Advanced Encryption Standard (AES) and recognising the barriers they pose is crucial for gathering admissible evidence. This guide offers practical solutions for handling encrypted data, bridging the gap between technical obstacles and legal requirements.
Table of Contents
- Encryption Explained For Digital Forensics
- Types Of Encryption
- Why Encryption Complicates Investigations
- Encryption And Legal Authority
- Types Of Encryption Encountered In Investigations
- Symmetric Encryption
- Asymmetric Encryption
- Hybrid Systems
- Decryption Techniques And Forensic Tools
- Password Recovery Techniques
- Key Extraction From Memory
- Forensic Tools For Encrypted Evidence
- Brute Force And Dictionary Attacks
- Documentation And Legal Standards
- Legal Protocols And Evidentiary Standards
- Challenges For Investigators And Defence Strategies
Key Takeaways
| Point | Details |
|---|---|
| Understanding Encryption Types | Familiarise yourself with symmetric and asymmetric encryption methods to effectively navigate challenges in digital investigations. |
| Legal Authority and Documentation | Ensure you understand the legal framework around decryption and maintain thorough documentation to support your findings in court. |
| Challenges in Evidence Recovery | Be prepared for obstacles in accessing encrypted data, including time constraints and jurisdictional issues that could impede investigations. |
| Complementing Encrypted Evidence | Use unencrypted evidence to support your case, recognising that encrypted data alone may not suffice in legal proceedings. |
Encryption Explained for Digital Forensics
Encryption is the process of transforming readable data, called plaintext, into scrambled, unreadable information, called ciphertext, using mathematical algorithms and keys. In your daily work as a digital forensics investigator in London, you’ll encounter this repeatedly, whether examining seized devices, intercepted communications, or cloud storage accounts related to cybercrime cases.
When suspects encrypt their devices, emails, or files, they’re essentially locking away potential evidence behind mathematical barriers. Understanding how these barriers work helps you navigate the legal and technical complexities you face during investigations. The difference between recognising what you’re dealing with and remaining baffled by it often determines whether a case moves forward or stalls.
Types of Encryption
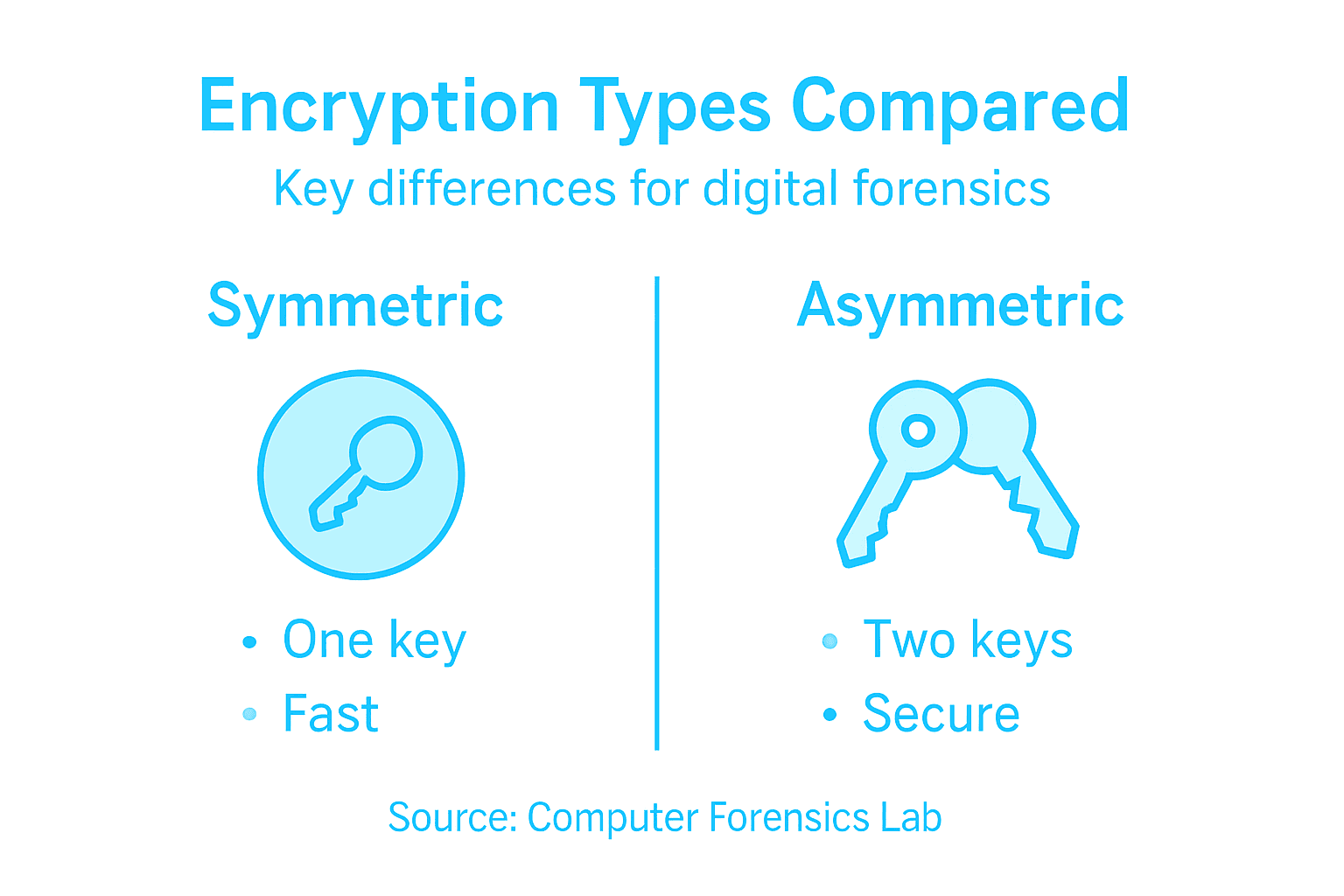
Two main encryption methods dominate digital forensics investigations:
-
Symmetric encryption (private-key encryption) uses a single shared key to both encrypt and decrypt data. Both parties must possess the same key. AES (Advanced Encryption Standard) is the current standard used by government agencies and organisations worldwide.
-
Asymmetric encryption (public-key encryption) uses two mathematically related keys: a public key for encrypting data and a private key for decrypting it. This method powers email encryption, secure messaging apps, and digital signatures.
Cryptographic algorithms and their foundational principles determine how effectively data remains protected during investigations.
Why Encryption Complicates Investigations
Encryption presents genuine obstacles. When you seize a suspect’s laptop encrypted with BitLocker or a mobile phone protected by iOS encryption, the device physically exists in your possession, but the data remains inaccessible without the correct key or passphrase.
This creates a fundamental problem:
- The data exists on the device
- You can verify it’s there through forensic imaging
- You cannot access it without the encryption key
- The suspect may refuse to provide the key
You’re left holding evidence you cannot read. Unlike traditional crime scenes where physical objects tell a story, encrypted data tells nothing unless unlocked.
Encryption doesn’t erase evidence—it simply hides it behind mathematics until the proper key appears.
Encryption and Legal Authority
The legal landscape around encryption differs significantly from other investigative tools. Your ability to compel decryption depends on legislation that varies by jurisdiction and case type.
Key legal distinctions:
- Production orders may compel suspects to provide encryption keys voluntarily
- Search warrants authorise device seizure but not necessarily key disclosure
- Regulatory frameworks differ between corporate investigations and criminal cases
- International cases introduce additional complications regarding cross-border data access
When conducting investigations involving protected communications, understanding e-discovery processes and legal requirements ensures you maintain proper chain of custody and admissibility standards throughout your analysis.
Pro tip: Document every encryption method, algorithm, and key-related finding in your forensic report with precise technical terminology—vague descriptions undermine credibility in court.
Types of Encryption Encountered in Investigations
During your investigations, you’ll encounter several encryption types protecting evidence. Each operates differently, presents distinct challenges, and requires different approaches. Recognising what you’re facing is your first step toward developing a strategy for accessing protected data or presenting findings to legal teams.
The encryption methods you encounter fall broadly into two categories based on how their keys function. Understanding this distinction shapes how you’ll approach evidence recovery and documentation in your London-based digital forensics work.
Symmetric Encryption
Symmetric encryption uses a single shared key for both encrypting and decrypting data. The same key that locks the data also unlocks it. This simplicity makes it fast and efficient, which is why it’s the standard for protecting data stored on devices.
Advanced Encryption Standard (AES) represents the modern benchmark in symmetric encryption. Government agencies, financial institutions, and operating systems worldwide use AES as their default protection method.
Common symmetric encryption you’ll encounter:
- AES with 128-bit, 192-bit, or 256-bit keys (stronger keys mean longer decryption times)
- BitLocker on Windows devices using AES encryption
- FileVault 2 on Apple macOS systems
- DES and 3DES (older methods, increasingly rare but still present in legacy systems)
The challenge: if a suspect refuses to provide the key or passphrase, accessing AES-encrypted data requires computational power that remains impractical with current technology.
Symmetric encryption’s greatest strength—using one key for speed—becomes your greatest obstacle when that single key remains hidden.
Asymmetric Encryption
Asymmetric encryption uses two mathematically linked keys: a public key for encrypting and a private key for decrypting. The public key can be shared openly, but the private key remains secret. This method powers secure communications and digital signatures across email systems, messaging platforms, and web encryption.
Modern cryptographic systems like RSA and ECC dominate asymmetric implementations. You’ll encounter these protecting email accounts, encrypted messaging applications, and certificate-based authentication systems.
Typical asymmetric encryption scenarios:
- PGP/GPG encrypted email communications
- Signal, WhatsApp, Telegram using end-to-end encryption
- HTTPS/TLS protecting web traffic
- Digital certificates authenticating identities
Asymmetric encryption creates a different investigation problem: even with the public key, you cannot decrypt communications without the private key. The suspect’s private key sits securely on their device or in their memory alone.
Hybrid Systems
Many modern applications combine both methods. A system might use asymmetric encryption to exchange a symmetric key, then use that symmetric key for faster bulk data encryption. This gives you speed plus security.
When you seize a device using hybrid encryption, decryption depends on whether you can obtain the symmetric key exchange or the user’s private key material stored on the device itself.
To clarify the practical distinctions between encryption methods, here’s a concise comparison:
| Attribute | Symmetric Encryption | Asymmetric Encryption | Hybrid Systems |
|---|---|---|---|
| Key Usage | Single shared key | Public/private key pair | Both key types combined |
| Typical Applications | Disk encryption, storage | Secure email, digital ID | Messaging, cloud storage |
| Speed | Fast and efficient | Slower, computationally intensive | Fast for bulk data, secure for exchange |
| Forensic Challenge | Need one hidden key | Private key must be obtained | Multiple steps to access data |
Pro tip: When documenting encrypted evidence, note the specific algorithm, key size, and implementation method in your forensic report—prosecutors need this technical precision when discussing encryption strength with legal experts.
Decryption Techniques and Forensic Tools
Once you’ve identified encrypted evidence, your next challenge is accessing it. You have three realistic paths: obtaining the passphrase voluntarily, using forensic software to recover keys or bypass encryption, or cracking the encryption through brute force—each with different legal, practical, and time constraints.
Most investigations won’t crack military-grade encryption. Instead, you’ll use specialised forensic tools designed to work with encrypted systems, recover unencrypted data fragments, or extract key material from device memory.
Password Recovery Techniques
Password recovery exploits weaknesses in how users create and store passphrases rather than breaking encryption itself. People choose predictable passwords, reuse credentials across systems, and sometimes leave password hints visible.
Common recovery methods include:
- Examining browser caches and autofill databases for saved passwords
- Analysing password managers and their stored credentials
- Recovering deleted password reset emails from archive folders
- Checking Windows credential managers and Keychain systems
- Reviewing device recovery keys or backup passphrases written down
This approach often succeeds where cryptanalysis fails. I’ve recovered access to encrypted devices simply by finding a Post-it note containing the password, or discovering the user relied on their birthday as the encryption key.
Password recovery works because humans, not mathematics, represent the weakest link in encryption security.
Key Extraction from Memory
When a device is powered on and actively decrypted, the encryption key exists somewhere in the system’s RAM memory. Digital forensics tools can capture this live memory before shutdown, then analyse the memory dump for key material.
This technique requires:
- Maintaining device power without triggering security features
- Extracting RAM contents using specialised hardware or software
- Analysing memory dumps for encryption key signatures
- Using recovered keys to access encrypted partitions
Memory extraction succeeds best on powered-on devices before evidence gets encrypted at rest. Once a device powers down, the key typically vanishes from RAM, closing this access method.
Forensic Tools for Encrypted Evidence
Specialised forensic software tools and techniques designed for encrypted evidence analysis include capabilities for disk imaging, memory extraction, password cracking, and metadata recovery from encrypted containers.
Standard forensic tools in UK investigations include:
- EnCase and FTK for comprehensive disk analysis and encrypted volume recognition
- Magnet AXIOM for multi-device evidence collection and mobile phone analysis
- Kali Linux for penetration testing and password cracking workflows
- Volatility for memory analysis and key extraction from RAM dumps
- WinHex for hex editing and sector-level data recovery
These tools don’t typically break modern encryption. Instead, they help you recover unencrypted data, identify encryption implementations, document security configurations, and sometimes extract key material from system memory or configuration files.
To assist investigators in selecting forensic tools, here is a summary of tool categories and their core functions:
| Tool Category | Primary Function | Typical Usage |
|---|---|---|
| Disk Imaging Software | Acquire bit-for-bit copy | Physical device evidence |
| Memory Analysis Tools | Extract volatile RAM data | Key retrieval from live memory |
| Password Recovery Tools | Identify user credentials | Access encrypted files |
| Metadata Readers | Analyse file and device metadata | Supplement investigation |
Brute Force and Dictionary Attacks
Brute force attacks systematically try every possible password combination. With modern encryption, this remains impractical for strong passphrases but succeeds against weak ones.
Tools like Hashcat and John the Ripper accelerate these attacks using GPU computing power, but time requirements grow exponentially with password strength. A 6-character password might crack in hours. A 12-character random passphrase could require centuries.
Brute force remains viable only when users create weak passphrases—which happens far more often than security professionals expect.
Documentation and Legal Standards
When documenting your decryption process for court, precision matters. You must clearly separate:
- What encryption exists and its technical specifications
- Which decryption methods you attempted and why
- What succeeded or failed and timeframes involved
- Whether the suspect provided access voluntarily or through legal process
- How recovered evidence maintains chain of custody
Pro tip: Maintain detailed logs of every decryption attempt, including timestamps, tools used, and results—this documentation protects your findings from defence scrutiny and demonstrates rigorous investigative procedure.
Legal Protocols and Evidentiary Standards
Encryption complicates evidence handling, but it doesn’t exempt you from legal requirements. Courts in England and Wales demand rigorous protocols for acquiring, preserving, and presenting encrypted evidence. A single procedural failure can render months of investigation inadmissible in court, regardless of what the data reveals.
Your investigation’s legal foundation rests on three pillars: proper authority to access evidence, maintaining chain of custody throughout handling, and documenting every step transparently.
Chain of Custody and Evidence Integrity
Chain of custody documents every person who touches evidence, when they touched it, and what they did with it. For encrypted evidence, this becomes critical because you’re handling protected data that nobody should be able to modify undetected.
Essential chain of custody elements:
- Initial seizure documented with date, time, location, and officer names
- Device serial numbers, IMEI codes, or identifying marks recorded
- Transfer logs whenever evidence changes hands
- Storage conditions and security measures noted
- Analysis activities recorded with timestamps and results
- Final disposition documented clearly
When dealing with encrypted devices, you must demonstrate that evidence remained unmodified from seizure through analysis. This is harder with encrypted data because you cannot verify contents without the key, which is precisely why documentation becomes your proof.
Chain of custody proves evidence integrity when the data itself remains unreadable—documentation becomes your only guarantee nothing changed.
Legal Authority and Compulsion Powers
Your authority to demand decryption differs dramatically based on the investigation type. Criminal cases, corporate investigations, and civil litigation each carry different legal frameworks.
Key distinctions:
- Regulation of Investigatory Powers Act 2000 allows compulsion of encryption keys in criminal investigations with proper judicial approval
- Computer Misuse Act 1990 addresses unauthorised access during decryption attempts
- Data Protection Act 2018 restricts how you handle personal data even when legally seized
- Common law and case precedent govern what courts accept regarding encryption evidence
When you lack legal authority to compel decryption, you document the encryption’s existence, technical specifications, and your unsuccessful decryption attempts. This becomes admissible evidence that encrypted data existed, even if unread.
International Standards and Best Practices
Proper identification, collection, acquisition, and preservation procedures ensure your evidence meets international legal standards. These standards apply even within UK investigations because courts often reference them when questioning forensic methodology.
Critical procedures include:
- Identifying encrypted evidence before handling
- Collecting evidence using proper legal process
- Acquiring forensic images without altering original devices
- Preserving evidence in secure, controlled environments
- Documenting analysis without modifying data
Documentation Standards
Your forensic report must explain encryption findings in language a judge understands. Technical precision matters, but clarity takes precedence. Courts need to grasp what encryption exists, why it prevents access, and what you attempted to overcome it.
Required report elements:
- Technical specifications of encryption encountered
- Authority obtained to access evidence
- Decryption methods attempted and results
- Unencrypted evidence recovered
- Timeframes for attempted decryption
- Professional opinion on encryption strength
Defence solicitors will scrutinise your documentation. Vague statements like “the device was encrypted” invite challenge. Precise statements like “the device used AES-256 encryption with NIST-approved implementation” withstand expert testimony.
Pro tip: Create your forensic report whilst conducting analysis, not afterwards—contemporaneous notes prevent memory gaps and demonstrate rigorous procedure to defence teams and prosecutors alike.
Challenges for Investigators and Defence Strategies
Encryption creates genuine operational obstacles that extend beyond technical barriers. You face time constraints, legal limitations, and increasingly sophisticated defence tactics that exploit encryption’s legitimacy. Understanding these challenges helps you develop realistic strategies rather than pursuing dead ends that waste investigative resources.
Defence solicitors now routinely challenge encryption evidence, questioning methodology, suggesting alternative explanations, and demanding proof that encrypted data actually contained relevant information. You must anticipate these challenges during your investigation, not after prosecution begins.
Operational and Time Constraints
Decryption takes time. Brute force attacks on strong passphrases can require months or years of computational effort. Meanwhile, investigations operate under pressure to charge suspects, gather additional evidence, and move cases forward.
You face competing pressures:
- Suspects remain in custody only temporarily whilst investigations progress
- Evidence degrades or becomes irrelevant if cases delay too long
- Resources allocated to one investigation deplete budgets for others
- Public expectations demand swift prosecution outcomes
- Cloud storage providers delete data after extended inactivity periods
Sometimes you must make strategic choices: pursue encrypted evidence now and delay other investigative leads, or prioritise unencrypted evidence that advances the case immediately. Experienced investigators know when encryption isn’t worth the effort.
Time pressure transforms encryption from a technical obstacle into a strategic decision about investigative priority.
Cloud Storage and Jurisdictional Complications
Cloud encryption creates unique challenges. Data stored on Google Drive, OneDrive, or iCloud remains encrypted at rest, but you lack physical device access to extract keys from memory. Challenges with encrypted data in cloud environments include data volatility, jurisdictional boundaries, and technical limitations that complicate standard forensic procedures.
Cloud-specific obstacles:
- Data may exist in multiple jurisdictions simultaneously
- Encryption happens at service provider level, not user device level
- Providers may delete data before investigation completes
- International legal frameworks restrict cross-border access
- Accounts protected by two-factor authentication require additional compulsion
You cannot seize cloud evidence like physical devices. Instead, you must navigate service provider cooperation, legal frameworks in multiple countries, and encryption implemented by organisations rather than suspects.
Defence Strategies and Challenges
Defence solicitors now employ encryption as a strategic advantage. They argue that encrypted evidence proves nothing without access, question whether data existed before encryption, and suggest suspects encrypted devices for legitimate privacy reasons unrelated to crimes.
Common defence tactics include:
- Challenging your authority to access encrypted devices
- Questioning whether decryption methods violated legal protocols
- Arguing encrypted data could contain innocent information
- Demanding you prove decrypted content matches original data
- Suggesting alternative explanations for encrypted data
Your forensic report must anticipate these challenges. Document your methodology, explain why decryption attempts succeeded or failed, prove chain of custody remained intact, and distinguish between encrypted evidence and recovered evidence.
Building Defensible Cases Despite Encryption
Don’t rely solely on encrypted evidence. Pursue corroborating unencrypted data: emails outside encrypted containers, deleted files in unencrypted partitions, metadata from encrypted files, communications on social media platforms, and financial records. Encrypted evidence supports cases; it rarely forms the entire foundation.
Strategic approaches include:
- Prioritising unencrypted evidence first
- Documenting encryption’s existence separately from investigative findings
- Building cases around metadata and circumstantial evidence
- Using decrypted evidence to corroborate rather than prove
- Identifying patterns across multiple evidence sources
Pro tip: When encryption blocks access, shift investigation focus to surrounding evidence—metadata, communications patterns, financial activity, and device behaviour often reveal more than encrypted containers would anyway.
Overcome Encryption Challenges with Expert Digital Forensics Support
Facing encrypted evidence can feel like confronting an impenetrable barrier. The article highlights critical obstacles such as navigating legal authority to compel decryption, preserving chain of custody, and managing complex technical encryption types like AES and asymmetric keys. These challenges demand not only technical expertise but also a precise understanding of legal protocols to maintain evidence integrity and ensure admissibility in court. If you are struggling with encrypted devices or data protected by advanced algorithms, recognising the weakest links such as password recovery or memory extraction is essential to advancing your investigation.
At Computer Forensics Lab, we specialise in tackling these exact hurdles. Our expert team provides comprehensive digital investigations by combining advanced forensic techniques and strict adherence to legal standards. Whether you need help with extracting evidence from mobile devices, cloud accounts, or encrypted storage, our proven track record supports law enforcement and legal professionals alike. Explore our detailed guidance on handling electronic evidence and gain visual insights through our informative infographics to better understand encryption implications. Don’t let encryption stall your case. Visit us now at Computer Forensics Lab to secure expert assistance that transforms complex encryption barriers into actionable evidence.
Frequently Asked Questions
What is encryption and how does it affect digital forensics investigations?
Encryption is the process of converting readable data (plaintext) into unreadable data (ciphertext) using mathematical algorithms and keys. In digital forensics, encryption can complicate investigations by making crucial evidence inaccessible without the correct decryption key or passphrase.
What are the main types of encryption encountered in investigations?
The primary types of encryption are symmetric encryption, which uses a single shared key for both encryption and decryption (e.g., AES), and asymmetric encryption, which utilises a public key for encryption and a private key for decryption. Additionally, hybrid systems combine both types for enhanced security and performance.
How can digital forensic investigators access encrypted data?
Investigators can attempt to access encrypted data through several methods, including obtaining the encryption key voluntarily, utilizing specialised forensic tools to recover keys or bypass encryption, or employing password recovery techniques. Sometimes, extracting keys from live system memory is also possible if the device is powered on.
What legal considerations must be taken into account when handling encrypted evidence?
Investigators must adhere to legal protocols such as maintaining chain of custody, securing proper authority to access evidence, and documenting every step of the process. The legal landscape around encryption can vary, affecting the ability to compel suspects to provide decryption keys, depending on the specific laws applicable to the investigation.