TL;DR:
- Saving a file is not equivalent to preserving evidence, and missteps in preservation can undermine investigations. Courts and organizations must follow rigorous processes, including proper identification, integrity, and access controls, to ensure digital evidence remains admissible and trustworthy. Building systemized, documented procedures throughout the evidence lifecycle is essential to prevent chain-of-custody failures and safeguard case integrity.
Saving a file is not the same as preserving evidence. It seems obvious once said aloud, yet this distinction costs legal teams, compliance officers, and private individuals derely every year. A missing log entry, an unrecorded chain of custody, or a timestamp applied in the wrong format can unravel months of investigation and render perfectly valid data inadmissible. Digital evidence preservation is a discipline built on law, technical rigour, and process integrity, and understanding it fully is no longer optional for anyone involved in UK legal proceedings or corporate investigations.
Table of Contents
- Evidence retention in UK legal proceedings
- Digital evidence and corporate compliance: risks and obligations
- Building robust evidence preservation systems
- Technical nuances: forensic standards and preventing evidence compromise
- Proportionality and privacy: preserving evidence for individuals
- What most professionals overlook about evidence preservation
- Expert support for evidence preservation
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Legal duty to retain | Courts and prosecutors mandate the preservation of potentially relevant digital evidence in UK cases. |
| Compliance risks | Failure to preserve can result in severe legal consequences, including contempt in civil litigation and investigations. |
| System integrity | Robust evidence management and audit trails help uphold evidential value for trial and investigation. |
| Technical standards | Accurate logs, precise timestamps, and repeatable forensic methods are key to reliable digital evidence preservation. |
| Balancing privacy | Imaging orders and proportional safeguards are essential for protecting personal data during evidence preservation. |
Evidence retention in UK legal proceedings
In UK criminal proceedings, preservation carries specific statutory weight. Police and prosecutors have clear duties to record and retain all material that may be relevant, preserve exhibits safely from loss or damage, cooperate to enable reasonable defence access, and produce exhibits at trial. These obligations exist because courts and prosecutors rely on retained digital material to prove facts reliably and to enable defence inspection and presentation at trial. Falling short of any one of these obligations creates grounds to challenge the integrity of a prosecution.
For the defence, this matters enormously. The Criminal Procedure and Investigations Act 1996 (CPIA) establishes access and inspection rights that depend on prosecution material having been preserved properly. If original devices have been wiped, modified, or simply mislaid, those rights become hollow. A digital evidence handling guide can help practitioners understand exactly what courts expect at each stage of a case.
“Courts rely on retained exhibits and digital material to prove facts reliably and to enable defence inspection and presentation at trial.” — GOV.UK guidance (CPIA Code)
The risks of incomplete preservation are not theoretical. Exhibits can be damaged during transit. Storage media can degrade. Metadata can be overwritten by routine system processes if no write-blocker is used during acquisition. Each of these outcomes creates a vulnerability that defence counsel can and will exploit. The following summarises what courts typically expect:
| Requirement | What it means in practice |
|---|---|
| Material relevance test | All potentially relevant material must be identified and retained |
| Exhibit integrity | Physical and digital exhibits must be protected from modification |
| Defence access | Retained material must be available for reasonable inspection |
| Trial production | Original or certified copies must be available for court presentation |
Prosecutors and investigators who rely on an evidence preservation overview before beginning a case are far better positioned to meet these standards consistently. And when disputes arise over the reliability of preserved material, expert witnesses in litigation play a central role in explaining technical processes to the court.
Digital evidence and corporate compliance: risks and obligations
The stakes in corporate settings are, if anything, even higher than in criminal proceedings, because the consequences are spread across legal, reputational, and financial dimensions simultaneously. In England and Wales, civil litigation triggers strict discovery and disclosure obligations. Once those obligations arise, every relevant piece of electronically stored information (ESI) must be preserved. Failure to do so carries serious risk.
Failing to preserve ESI after discovery obligations arise can expose parties to serious legal consequences, including contempt of court risk, because messaging apps and deleted data can be treated as documentary material. This is not a theoretical edge case. Courts in England and Wales have sanctioned parties for the destruction of WhatsApp message chains, the deletion of email threads, and the wiping of company devices before inspections took place.
Consider a practical scenario: a senior employee suspected of taking client data to a competitor deletes several months of emails and clears their phone. If the company had a preservation hold in place, those deletions become powerful evidence of consciousness of guilt. Without one, the investigation may stall entirely. The following steps represent a structured approach to corporate preservation compliance:
- Issue a legal hold notice the moment litigation or investigation becomes reasonably foreseeable.
- Identify all custodians who may hold relevant ESI, including personal devices used for work.
- Map all data sources: email servers, cloud storage, messaging platforms, and collaboration tools.
- Suspend automated deletion routines that would otherwise purge relevant data.
- Document every step taken with dates, names, and actions recorded in a centralised log.
Pro Tip: Do not wait for formal legal proceedings to begin before issuing a preservation hold. The obligation to preserve arises when litigation is reasonably anticipated, not when a claim is filed. Acting early is always safer than acting late.
A preservation checklist for UK cases can help compliance teams build this process into their standard operating procedures. The contrast between compliant and non-compliant approaches could not be starker:
| Approach | Outcome |
|---|---|
| Compliant: immediate hold, documented custodians | Consistent disclosure, reduced sanctions risk |
| Non-compliant: no hold, selective deletion | Contempt risk, adverse inference, sanctions |
| Partially compliant: hold issued late | Gaps in disclosure, credibility challenged |
For organisations building internal digital forensics compliance frameworks, understanding these distinctions is the foundation. A forensics handling guide tailored to corporate contexts will make the difference between a defensible disclosure process and a catastrophic one.
Building robust evidence preservation systems
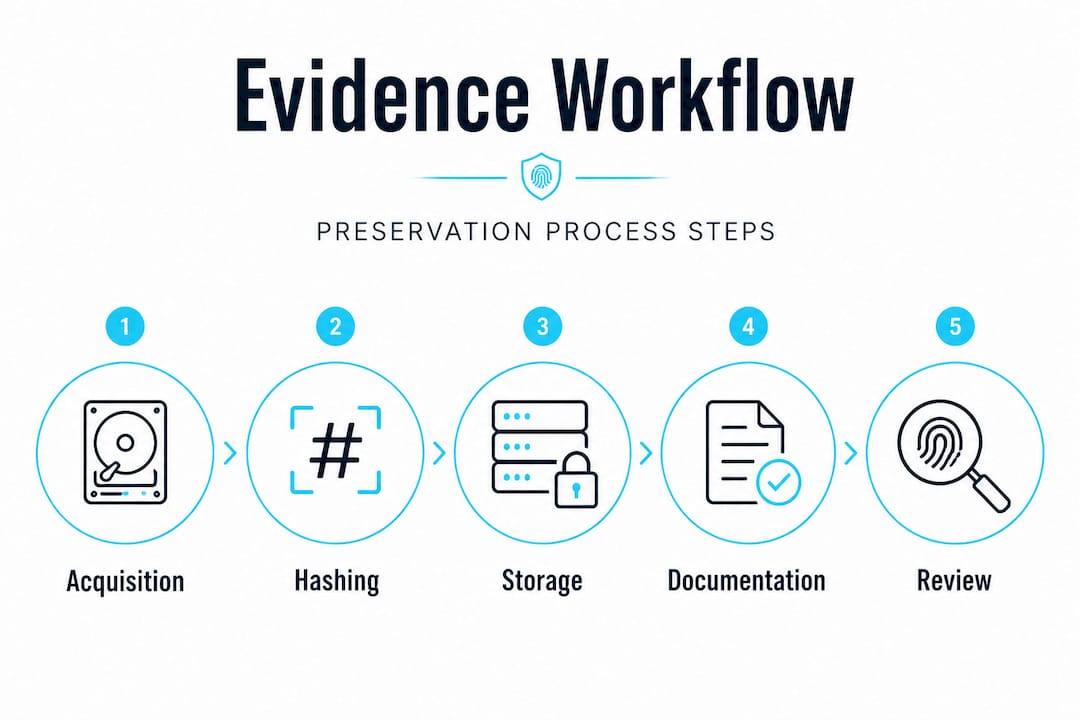
Preservation is not a one-off action. It is a system. NIST SP 1500-33A makes this explicit: evidence handlers should build systems for retention, preservation, integrity, and disposition across the entire evidence lifecycle, enabling repeatable forensic methods that maintain evidential value, not just preventing file deletion. This distinction between saving a file and building a forensic-quality preservation system is where most organisations and individuals go wrong.
The evidence lifecycle has four key stages:
- Acquisition: collecting data in a forensically sound manner, using write-blockers, cryptographic hashing, and documented chain-of-custody records
- Retention: storing data securely with access controls, audit logs, and physical security for any hardware exhibits
- Preservation: maintaining integrity over time through periodic hash verification and protection against environmental or accidental damage
- Disposition: properly disposing of evidence when legal hold obligations expire, with documented destruction certificates
Each stage demands trained handlers, not just competent IT staff. The distinction matters because forensic acquisition requires specialist knowledge of file systems, metadata, and tool validation that general IT personnel rarely possess. Without this, evidence that looks intact may fail admissibility tests during cross-examination.
| Stage | Key control | Risk if missed |
|---|---|---|
| Acquisition | Write-blocker, hash value | Original data modified, inadmissible |
| Retention | Access controls, audit log | Tampering risk, chain-of-custody gap |
| Preservation | Periodic verification | Degradation undetected, integrity lost |
| Disposition | Documented destruction | Unauthorised access after hold expires |
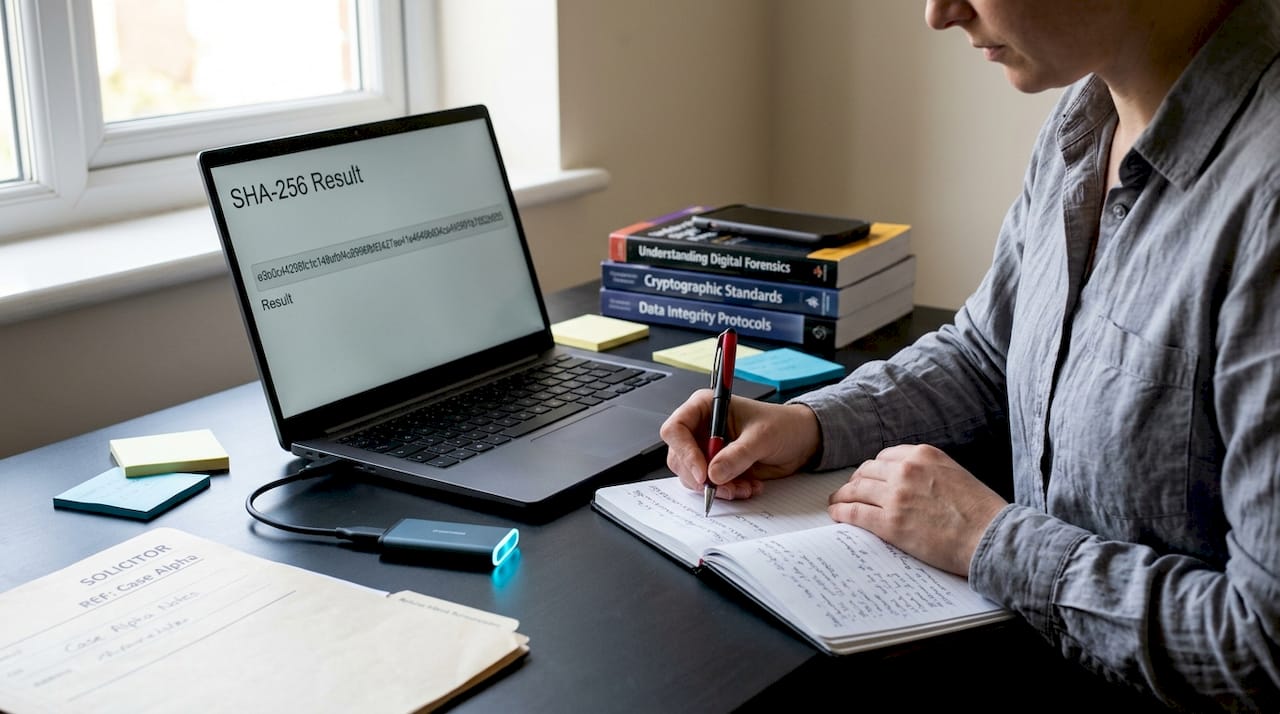
Pro Tip: Always record the SHA-256 or MD5 hash value of acquired forensic images immediately after collection. If the hash changes at any point later, you have proof of tampering or corruption. Courts regard this level of documentation as the baseline for credible forensic work.
Securing digital evidence properly requires more than a locked drawer. It requires a system of documented processes that any trained examiner could replicate and audit. The digital evidence steps required in UK legal cases reflect exactly this kind of rigour.
Technical nuances: forensic standards and preventing evidence compromise
The technical requirements for admissible digital evidence go deeper than most non-specialists realise. NCSC guidance on digital forensics requires logs to be collected in an easily ingestible format for forensic analysis, with ISO 8601 timestamps including milliseconds in UTC. This level of precision matters because digital events often occur within fractions of a second of each other, and reconstructing the sequence of events depends entirely on the accuracy of timestamping.
Consider a data exfiltration case. An employee connects a USB device, copies files, and disconnects within ninety seconds. If your system logs record timestamps only to the nearest second, and if those timestamps are recorded in local time without UTC offset, the sequence of events becomes impossible to establish with certainty. That is enough to create reasonable doubt, or in a civil case, to undermine a damages claim entirely.
Practical technical controls for forensically sound evidence preservation include:
- Write-blockers: prevent any read operation from inadvertently modifying original media
- Forensic imaging tools: create bit-for-bit copies that preserve deleted file remnants and slack space
- Hash verification: use SHA-256 or SHA-512 hashing before and after imaging to confirm integrity
- Secure timestamping: synchronise all system clocks to UTC via NTP and log to millisecond precision
- Machine-readable logs: structured formats (such as JSON or syslog) that allow forensic tools to parse and analyse events programmatically
- Access controls: restrict access to preserved evidence to authorised personnel only, with every access event logged
Pro Tip: If you manage systems that might be subject to investigation, configure your logging infrastructure to write immutable logs to a separate, write-once storage location. Even if an attacker or rogue employee compromises primary systems, the log trail survives intact.
These controls collectively prevent the most common form of evidence compromise: accidental modification. A single write operation to original media, even from booting a device normally, can overwrite file allocation tables, change access timestamps, and contaminate data that would otherwise prove pivotal. The evidence preservation methods used by professional forensic examiners are designed to eliminate this risk entirely. For anyone responsible for electronic evidence handling, these principles are not optional extras; they are the baseline.
Proportionality and privacy: preserving evidence for individuals
For private individuals, evidence preservation raises a different but equally important set of concerns. Preservation can be intrusive. Imaging a personal device or accessing cloud accounts touches on private communications, financial records, and intimate personal data that has nothing to do with the matter at issue. Courts and litigation strategy may use approaches like imaging orders with specific safeguards, where the key is proportionality: preventing concealment or destruction of relevant evidence while protecting private or irrelevant information from unnecessary exposure.
An imaging order, for example, might require a neutral third-party forensic examiner to create a forensic image of a device, with a defined protocol specifying exactly which categories of data can be reviewed, by whom, and under what conditions. This approach balances the legitimate need to preserve evidence against the individual’s right to privacy under Article 8 of the European Convention on Human Rights, which remains part of domestic law under the Human Rights Act 1998.
For individuals facing these situations, the practical guidance is clear:
- Seek legal advice immediately if you receive a preservation order or disclosure request
- Do not attempt to self-collect evidence from your own devices; use a qualified forensic examiner
- Understand that deletion of relevant data after notification of a claim is likely to be treated as destruction of evidence, regardless of intent
- Request that any imaging order includes explicit provisions limiting access to irrelevant personal data
“The key is proportionality and preventing concealment or destruction while protecting private or irrelevant information.” — Pinsent Masons Out-Law
Preserving digital evidence correctly as an individual requires professional support, not just good intentions. Courts expect process and documentation, not just the evidence itself.
What most professionals overlook about evidence preservation
After years of examining cases where digital evidence has failed to support a sound investigation, one pattern stands out above all others: the critical point of failure is almost never a lack of evidence. It is a broken chain of custody.
Investigators, compliance officers, and legal teams sometimes spend enormous resources collecting data, only to find that the handling records are incomplete, the acquisition methodology is undocumented, or the examiner cannot confirm that the original media was never modified. A skilled opposing counsel does not need to prove the evidence was tampered with. They only need to show the chain of custody had gaps.
This is why professional judgement counts more than following checklists. A checklist tells you what to do. Judgement tells you when something is wrong, when a process has been skipped, when a log entry looks inconsistent with the claimed timeline. The UK forensics handling standards that experienced examiners follow are built around this kind of vigilance, not box-ticking.
There is also a dangerous assumption that modern cloud platforms preserve evidence automatically. They do not. Retention policies vary widely. Data may be purged after 30 days. Synchronisation conflicts can overwrite versions. Legal hold features exist on some platforms but must be deliberately activated. Relying on a cloud provider to preserve your evidence without explicit configuration is a serious and surprisingly common mistake.
The most effective organisations and individuals we work with treat evidence preservation as an ongoing operational discipline, not a reaction to crisis. That shift in mindset is what separates cases that succeed from those that fall apart at disclosure.
Expert support for evidence preservation
At Computer Forensics Lab, we support legal professionals, compliance officers, and private clients across the UK in navigating the full complexity of digital evidence preservation. Our digital forensics services cover every stage of the evidence lifecycle, from forensically sound acquisition and secure retention through to court-ready expert witness reporting. Whether you are dealing with an employee misconduct investigation, a civil dispute, or a criminal matter, we ensure that chain of custody is maintained at every step. Explore our digital evidence investigation capabilities or contact our team directly to discuss how forensic investigation expertise can protect the integrity of your case from the outset.
Frequently asked questions
What counts as digital evidence in UK courts?
Digital evidence can include emails, logs, documents, app messages, and deleted data that is relevant to a case, and all of it must be preserved and available for inspection by the defence.
What happens if digital evidence is erased before a trial?
Erasing or destroying digital evidence can lead to court sanctions, a risk of contempt, or adverse inference against your case; messaging apps and deleted data can be treated as documentary material, making their destruction especially serious.
How can individuals ensure their digital evidence is preserved correctly?
Individuals should seek professional forensic support and, where appropriate, request court-approved imaging orders with safeguards to ensure proportionality and proper protection of private, irrelevant information.
What are the best technical practices for preserving digital evidence?
Use write-blockers, forensic imaging tools, and ISO 8601 timestamps in UTC with millisecond precision, verify integrity with hash values, and maintain fully auditable, repeatable chain-of-custody processes.