A single overlooked gap in documenting how digital evidence moved from a suspect’s laptop to the courtroom can render months of investigative work inadmissible. In UK legal proceedings, digital evidence features in over 90% of criminal investigations, yet chain of custody failures remain a leading cause of challenges to admissibility. Digital chain of custody is the systematic process that tracks every interaction with electronic evidence, from initial seizure through forensic analysis to presentation in court. This guide clarifies what digital chain of custody entails, explains the UK legal framework governing it, examines key preservation steps and emerging technologies, addresses common challenges like cloud data and AI manipulation, and provides actionable best practices to ensure your digital evidence withstands judicial scrutiny.
Table of Contents
- Key takeaways
- Understanding digital chain of custody in UK legal contexts
- Key steps and technologies in preserving digital evidence integrity
- Challenges and evolving solutions in managing digital chain of custody
- Best practices for legal professionals to ensure admissibility of digital evidence
- Discover expert digital forensics services
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Digital chain of custody | A systematic record of how electronic evidence is collected, transferred, stored, analysed and presented to protect integrity and admissibility. |
| Contemporaneous records | Records must be created at the time of each action rather than reconstructed later. |
| UK legal framework | PACE 1984 and CPIA 1996 govern digital evidence handling, including lawful seizure and integrity obligations. |
| Emerging tech potential | Blockchain and related technologies can enhance audit trails and data integrity when implemented to support admissibility. |
Understanding digital chain of custody in UK legal contexts
Digital chain of custody refers to the chronological documentation of how electronic evidence is collected, preserved, transferred, stored, analysed, and presented in legal proceedings. Unlike physical evidence that can be sealed in a bag and stored on a shelf, digital data exists on volatile media that can be altered remotely, copied without trace, or corrupted through improper handling. Courts require proof that the evidence presented is identical to what was originally seized and that no unauthorised modifications occurred.
The UK legal framework governing digital evidence handling centres on several statutes. The Police and Criminal Evidence Act 1984 (PACE) establishes powers for lawful seizure of digital devices and sets standards for evidence handling by law enforcement. The Criminal Procedure and Investigations Act 1996 (CPIA) mandates disclosure obligations and requires investigators to maintain integrity throughout the investigation process. The Criminal Procedure Rules and Civil Procedure Rules further specify how digital evidence must be authenticated and presented in respective proceedings.
UK courts scrutinise chain of custody rigorously because any break in the documented trail creates reasonable doubt about evidence integrity. A defence barrister can challenge admissibility by demonstrating that evidence could have been tampered with, altered, or contaminated during an undocumented period. Judges may exclude evidence entirely if the prosecution or claimant cannot prove an unbroken chain with contemporaneous records of every person who accessed the evidence, when they accessed it, what actions they performed, and how the evidence was secured between handling stages.
Digital chain of custody systematically documents handling, transfer, storage, and analysis to ensure integrity and admissibility under UK legal frameworks like PACE 1984 and CPIA 1996. This documentation must be contemporaneous, meaning records are created at the time of each action rather than retrospectively reconstructed. The difference between digital and physical evidence handling lies in the ease with which electronic data can be modified without visible signs. A document file can be edited, a timestamp altered, or metadata stripped in seconds, whereas physical evidence typically shows visible signs of tampering.
Common misconceptions include believing that simply taking a photograph of a device screen constitutes proper evidence collection, or that copying files to a USB drive preserves their integrity. Neither approach maintains chain of custody because they fail to document the process, verify data integrity through cryptographic means, or prevent subsequent alteration. Legal professionals must understand that understanding chain of custody procedures requires technical precision and meticulous documentation from the moment evidence is identified.
Key steps and technologies in preserving digital evidence integrity
Maintaining digital chain of custody involves sequential stages, each requiring specific technical practices and documentation. The process begins with identification and collection, where investigators must identify relevant digital devices or data sources under lawful authority. PACE authorises seizure powers for law enforcement, whilst civil litigators rely on disclosure orders or search and seizure orders. Immediate isolation of devices is critical. Mobile phones should be placed in Faraday bags to block network signals, preventing remote wiping or data modification.
Forensic imaging creates an exact bit-for-bit copy of storage media without altering the original. Investigators use hardware write-blockers that prevent any data from being written to the source device during the copying process. This ensures the original evidence remains pristine. The forensic image, not the original device, is then used for analysis. Key mechanics include identification with legal authority, forensic imaging, tamper-evident packaging, hash value generation, logging handlers and dates, secure storage, and validation via audit trails and hash comparisons.
Hash value generation provides cryptographic verification of data integrity. A hash function processes the entire dataset and produces a unique alphanumeric string. If even a single bit changes, the hash value changes completely. Investigators calculate hash values immediately after collection and again before analysis, presentation, or any transfer. Matching hash values prove the data has not been altered. Common algorithms include SHA-256 and MD5, though SHA-256 is preferred for its stronger collision resistance.
Transportation and storage require secure, controlled conditions. Tamper-evident bags or containers seal physical devices, showing visible signs if opened. Digital evidence should be stored in secure facilities with restricted access, environmental controls to prevent degradation, and logging systems that record every entry and exit. Each person who handles evidence must be documented with their name, role, purpose of access, date, time, and location. This creates an unbroken audit trail.
| Stage | Key technology | Documentation required |
|---|---|---|
| Collection | Faraday bags, legal seizure authority | Device description, location, date, time, seizing officer |
| Imaging | Write-blockers, forensic software | Hash values, imaging tool used, operator name, date |
| Storage | Secure facilities, tamper-evident seals | Access logs, environmental conditions, custodian details |
| Analysis | Validated forensic tools | Analyst name, methods used, findings, date |
| Presentation | Verified copies, hash validation | Chain of custody logs, expert witness reports |
Pro Tip: Always isolate devices immediately in Faraday bags to prevent remote tampering. A suspect with network access can remotely wipe a phone or trigger encryption, destroying evidence before it can be secured. Isolation must occur within seconds of seizure.
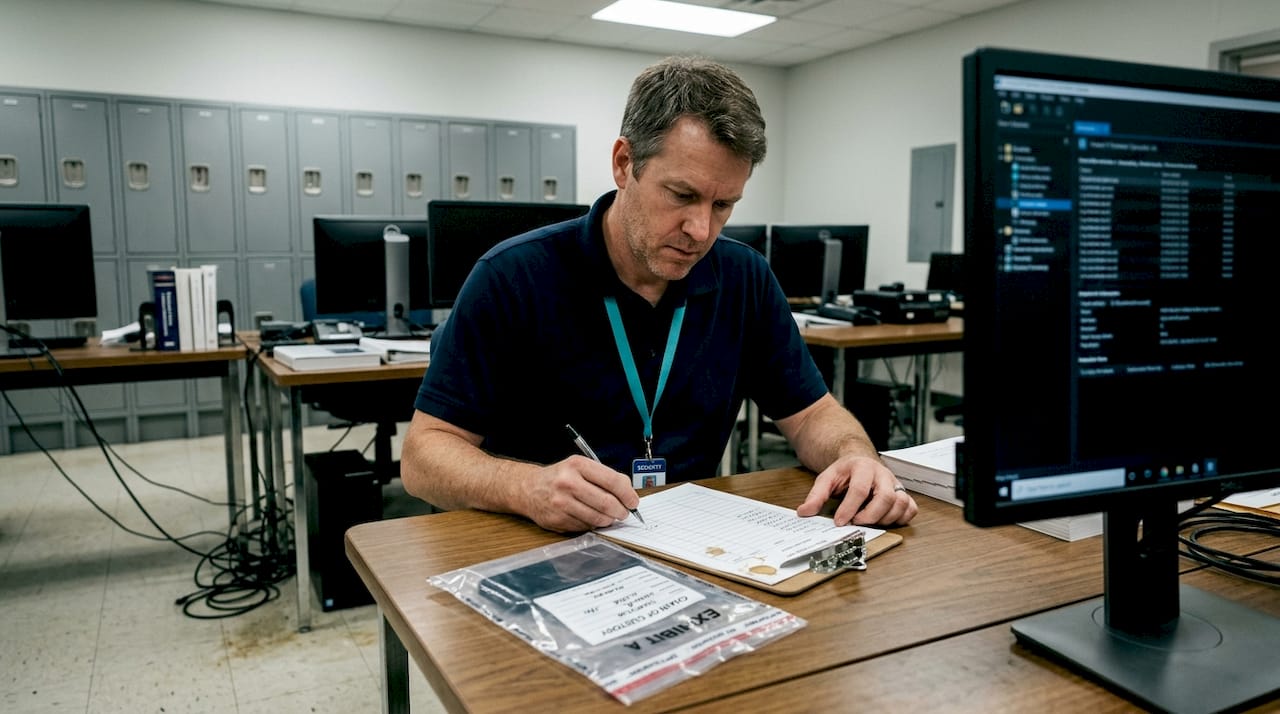
The forensic imaging process legal evidence requires validated tools and documented procedures. Forensic software must be tested and verified to ensure it does not alter source data. Analysts should maintain detailed notes of every command executed, every file examined, and every finding discovered. These notes become part of the chain of custody record and may be scrutinised during cross-examination. Chain of custody tips evidence emphasise that documentation quality often matters more than technical sophistication.
Challenges and evolving solutions in managing digital chain of custody
Digital evidence presents complexities that traditional physical evidence does not. Cloud storage introduces multi-jurisdictional challenges because data may reside on servers in multiple countries, each with different legal frameworks governing access and disclosure. A UK investigator seeking evidence stored on servers in Ireland, the United States, and Singapore must navigate conflicting data protection laws, mutual legal assistance treaties, and service provider policies. Maintaining chain of custody becomes difficult when third parties control access and can modify or delete data without notice.
Volatile memory poses another challenge. Data in RAM, running processes, and network connections exist only whilst a device is powered on. Shutting down a computer to seize it destroys this evidence. Live forensic acquisition captures volatile data before powering down, but this introduces risk of alteration. Every action taken on a live system changes some data, creating tension between preserving volatile evidence and maintaining an unaltered state.
AI-generated content and deepfakes challenge authenticity verification. Challenges include multi-jurisdictional cloud data, volatile evidence like RAM, deepfakes, metadata loss, and human error. A manipulated video or fabricated document may appear genuine, and traditional hash verification only confirms the file has not changed since collection, not whether it was authentic originally. Courts increasingly require expert testimony on digital authenticity, examining metadata, compression artefacts, and consistency with known device characteristics.
The Wagatha Christie case illustrated how deletion and spoliation impact credibility. Coleen Rooney’s legal team argued that Rebekah Vardy’s deletion of WhatsApp messages and loss of evidence from a dropped phone into the North Sea damaged the integrity of the digital record. Whilst the case proceeded, the gaps in evidence chain affected witness credibility and required extensive forensic effort to recover what remained.
Emerging technologies offer solutions. ISO/IEC 27037 standards, blockchain tamper-proof logs, and cryptographic hashes provide promising improvements but require training and legal acceptance. Blockchain creates immutable audit trails where each evidence handling event is recorded in a distributed ledger that cannot be altered retroactively. Every transfer, access, or analysis action is timestamped and cryptographically linked to previous entries. This provides stronger assurance than paper logs or centralised databases that can be modified.
| Approach | Advantages | Disadvantages |
|---|---|---|
| Traditional paper logs | Familiar to courts, simple to implement | Easily lost, altered, or incomplete; no real-time verification |
| Digital logging systems | Automated timestamps, searchable records, reduced human error | Requires training, potential technical failures, may be challenged as unfamiliar |
| Blockchain audit trails | Immutable records, distributed verification, tamper-proof | Legal acceptance uncertain, requires infrastructure investment, complexity |
Pro Tip: Practitioners should prioritise continuous validation and use of digital timestamping over paper records. Automated systems reduce gaps caused by forgotten entries and provide precise timestamps that paper logs cannot match. However, ensure any digital system used is itself forensically sound and maintains its own integrity records.
Why document digital evidence becomes even more critical as evidence types diversify. Social media posts, encrypted messaging apps, and Internet of Things devices each present unique preservation challenges. Legal professionals must work closely with forensic experts who understand both the technical requirements and the legal standards. Legal considerations digital forensics UK include ensuring compliance with data protection regulations whilst preserving evidence, a balance that requires careful planning and documentation.
Best practices for legal professionals to ensure admissibility of digital evidence
Legal professionals must adopt rigorous practices to ensure digital evidence withstands admissibility challenges. The foundation is impeccable, contemporaneous documentation for each handling stage. Every person who touches evidence, physically or digitally, must be recorded with their name, role, date, time, location, and purpose of access. These records should be created immediately, not reconstructed later from memory. Courts can detect retrospective documentation through inconsistencies and gaps.
Training is essential. Personnel handling digital evidence must understand forensic principles, chain of custody requirements, and the specific procedures your organisation employs. This includes legal teams, investigators, IT staff, and administrative personnel who transport or store evidence. Regular training updates ensure awareness of evolving standards and technologies.
Tamper-evident packaging and cryptographic verification should be standard practice. Physical devices go into tamper-evident bags immediately upon seizure, with seals photographed and documented. Hash values are calculated at collection, before and after any transfer, before analysis, and before court presentation. Any hash mismatch triggers immediate investigation to determine whether alteration occurred and whether the evidence remains usable.
Digital systems with barcoding, timestamps, and audit trails provide superior reliability compared to paper logs. Barcode scanners can automatically log evidence movements between locations, reducing manual entry errors. Timestamps are precise to the second, eliminating ambiguity about sequence of events. Audit trails capture every access attempt, successful or failed, creating a complete picture of evidence handling.
Regular audits and reconciliations detect documentation gaps or metadata inconsistencies before they become courtroom problems. Periodic reviews of chain of custody records identify missing entries, unauthorised access, or procedural deviations. Addressing these proactively prevents evidence exclusion. Any gap or undocumented access in chain of custody can lead to evidence exclusion; UK courts require strict proof of unbroken, documented integrity.
Pro Tip: Immediate isolation of digital devices upon collection and retention of forensic copies can be decisive in admissibility challenges. If opposing counsel questions whether evidence was altered, you can demonstrate that the original device was isolated within seconds of seizure, preventing any network access or remote modification. Forensic copies made with write-blockers and verified through hash values prove the analysed data matches the original exactly.
Legal professionals should engage forensic experts early in cases involving digital evidence. Experts can advise on collection methods, identify potential evidence sources, and ensure proper preservation. Their involvement from the outset prevents costly mistakes that compromise evidence integrity. Digital forensics UK courts recognise expert testimony as essential for authenticating complex digital evidence and explaining technical processes to judges and juries.
Maintaining detailed forensic reports is equally important. Reports should document every step of the forensic process, every tool used, every finding discovered, and every conclusion reached. These reports become part of the evidence record and must withstand cross-examination. Clear, comprehensive reporting demonstrates professionalism and builds confidence in the evidence’s reliability. The electronic evidence handling guide UK professionals 2026 provides detailed frameworks for structuring forensic reports that meet UK court expectations.
Discover expert digital forensics services
Navigating the complexities of digital chain of custody requires specialised expertise and resources that many legal teams lack in-house. Computer Forensics Lab offers comprehensive digital forensics services tailored to UK legal proceedings, ensuring your digital evidence meets the highest standards of integrity and admissibility. Our London-based team provides forensic imaging, secure evidence handling, cryptographic verification, and detailed chain of custody documentation that withstands judicial scrutiny. We conduct digital forensic investigations across devices, cloud platforms, and social media, recovering and preserving evidence whilst maintaining unbroken audit trails. Our expert witness reports clearly explain technical findings to courts, and our involvement in high-profile cases demonstrates our credibility. Whether you need immediate evidence preservation or comprehensive analysis, our services support litigation, criminal defence, and corporate investigations. Explore how digital forensics data expertise can strengthen your cases.
Frequently asked questions
What is digital chain of custody in forensic investigations?
Digital chain of custody is the documented process tracking digital evidence from initial seizure through collection, preservation, analysis, storage, and presentation in court. It records every person who handled the evidence, every action taken, and every transfer between locations to ensure integrity and admissibility. UK legal frameworks including PACE 1984 and CPIA 1996 require this documentation to prove evidence has not been altered or tampered with. Without an unbroken chain, courts may exclude evidence entirely.
How does hash value generation protect evidence integrity?
Hash values are unique digital fingerprints created by processing data through cryptographic algorithms. If even one bit of data changes, the hash value changes completely, making alteration immediately detectable. Forensic investigators calculate hash values at collection and recalculate them before analysis and court presentation. Matching hash values prove the evidence remains identical to what was originally seized, providing verifiable proof of integrity that courts can trust.
What are common challenges when handling cloud-based digital evidence?
Cloud evidence presents multi-jurisdictional complexities because data may reside on servers in multiple countries with conflicting legal frameworks. Investigators must navigate data protection laws, mutual legal assistance treaties, and service provider policies to access evidence lawfully. The volatility of cloud data means providers can modify or delete information without notice, and reliance on third parties complicates maintaining direct chain of custody. These factors make cloud evidence preservation significantly more difficult than traditional local storage.
Can blockchain improve digital chain of custody in legal cases?
Blockchain technology creates immutable audit trails where each evidence handling event is recorded in a distributed ledger that cannot be altered retroactively. This provides stronger assurance than paper logs or centralised databases that can be modified. However, blockchain’s use in legal proceedings requires broader standardisation and judicial acceptance. Courts must recognise blockchain records as reliable, and practitioners need training to implement and explain the technology effectively. Whilst promising, blockchain adoption in chain of custody remains in early stages.