Selecting a computer forensic company for legal or corporate investigations demands careful consideration. The integrity of digital evidence and the credibility of expert testimony can determine case outcomes, making your choice of forensic partner critical. Whether you’re a solicitor preparing for litigation, a security team investigating data breaches, or an individual seeking evidence for personal matters, understanding how to evaluate forensic providers ensures you work with qualified experts who maintain evidential standards. This guide walks you through essential selection criteria, profiles leading UK forensic companies, and provides situational recommendations to help you make informed decisions that protect your interests and strengthen your investigations.
Table of Contents
- Key Criteria For Choosing Computer Forensic Companies In The UK
- Leading Computer Forensic Companies In The UK And Their Services
- Comparing UK Computer Forensic Companies: A Snapshot Of Offerings And Strengths
- Making The Right Choice: Situational Recommendations For Different Needs
- Explore Specialised Digital Forensics Solutions With Computer Forensics Lab
Key takeaways
| Point | Details |
|---|---|
| Accreditation matters | Look for ISO certifications and adherence to national forensic guidelines to ensure evidence admissibility. |
| Chain of custody is critical | Proper documentation of evidence handling from collection to court presentation prevents challenges to integrity. |
| Expertise varies significantly | Companies specialise in different areas such as malware analysis, encryption bypass, or mobile device forensics. |
| Service scope differs | Some firms focus on legal support whilst others prioritise corporate security or private investigations. |
| Transparent communication is essential | Clear reporting, realistic timelines, and honest pricing indicate professional forensic practice. |
Key criteria for choosing computer forensic companies in the UK
Selecting a forensic company requires evaluating technical competence, legal compliance, and operational transparency. These factors directly impact whether your digital evidence withstands scrutiny in court or internal proceedings.
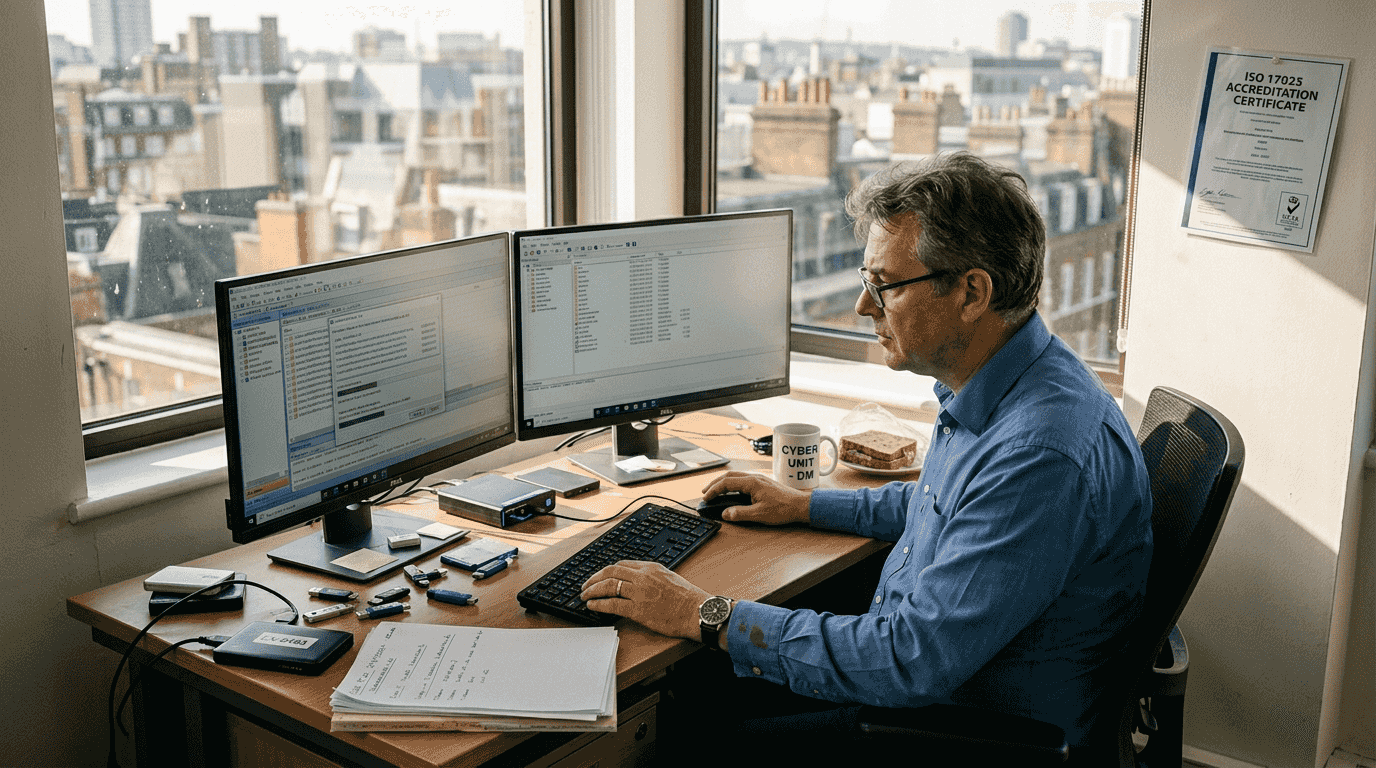
Accreditation provides the foundation for trustworthy forensic work. Companies should hold ISO 17025 certification for testing and calibration laboratories, demonstrating their adherence to international quality standards. Look for membership in professional bodies like the Forensic Science Regulator’s network, which ensures practitioners follow digital forensics best practices 2025 and maintain current knowledge of evolving techniques. The legal admissibility of digital evidence depends on demonstrating integrity throughout the investigation process, making these credentials non-negotiable.
The chain of custody digital evidence documentation separates professional forensic companies from amateur operators. Every action taken with evidence must be recorded, timestamped, and attributed to specific personnel. This creates an unbroken trail from initial seizure through analysis to courtroom presentation. Companies should use tamper-evident packaging, secure storage facilities with access logs, and cryptographic hashing to verify data integrity at each stage. Without meticulous custody records, even technically sound analysis becomes vulnerable to legal challenges.
Technical expertise varies considerably across forensic providers. Assess whether companies possess capabilities relevant to your investigation:
- Encryption and password recovery techniques for secured devices and files
- Malware analysis and reverse engineering for cybersecurity incidents
- Mobile device forensics covering iOS, Android, and legacy systems
- Cloud data acquisition from platforms like Microsoft 365, Google Workspace, and social media
- Network forensics for tracking intrusions and data exfiltration
- File system expertise across Windows, macOS, Linux, and specialised systems
Validated forensic tools form the backbone of credible analysis. Companies should use industry-standard software like EnCase, FTK, or Cellebrite, supplemented by open-source tools when appropriate. More importantly, they must document their methodologies thoroughly, explaining tool selection, configuration settings, and analytical approaches in written reports. This transparency allows independent verification and demonstrates scientific rigour.
Communication quality reveals professionalism. Forensic companies should provide clear timelines, explain technical findings in accessible language, and respond promptly to questions. They should offer detailed written reports suitable for legal proceedings, including methodology sections, findings summaries, and supporting exhibits. Pricing should be transparent, with itemised quotes covering acquisition, analysis, reporting, and potential court testimony.
Pro Tip: Request case studies or references from previous clients in similar industries or case types. Reputable forensic companies can demonstrate relevant experience without breaching confidentiality, giving you confidence in their ability to handle your specific investigation needs.
Leading computer forensic companies in the UK and their services
The UK forensic market includes established firms with distinct specialisations and service approaches. Understanding these differences helps you identify providers aligned with your investigation requirements.
Computer Forensics Lab operates from London, offering comprehensive digital forensic services to legal professionals, corporate clients, and private individuals. Their expertise spans computing devices, mobile phones, social media platforms, and cloud data analysis. They provide expert witness testimony, maintain rigorous chain of custody procedures, and handle cases involving cybercrime, data breaches, employee misconduct, and intellectual property theft. Their involvement in media projects like Discovery+’s ‘999 Murder Calling’ demonstrates their credibility in high-profile investigations. Services include data recovery from damaged devices, malware analysis, penetration testing, and detailed forensic reporting suitable for litigation.
CCL Solutions Group focuses on mobile device forensics and digital investigations, serving law enforcement, government agencies, and private sector clients. They develop proprietary forensic software and provide training programmes for investigators. Their expertise includes smartphone data extraction, application analysis, and deleted data recovery from various mobile platforms.
S-RM (formerly Siemens) delivers corporate digital forensics within broader risk management services. They specialise in internal investigations, regulatory compliance, and cybersecurity incident response. Their target audience includes multinational corporations, financial institutions, and organisations facing complex fraud or data breach scenarios.
Kroll offers global forensic services with UK operations, combining digital forensics with corporate investigations and cybersecurity consulting. They handle large-scale data breaches, intellectual property theft, and litigation support for corporate clients and law firms.
Stroz Friedberg (part of Aon) provides digital forensics alongside cyber risk consulting. They serve legal teams with eDiscovery services, forensic analysis, and expert testimony in complex commercial disputes.
The document provides National Guidance for Streamlined Forensic Reporting, ensuring UK forensic companies follow standardised procedures for evidence documentation and court presentation. This framework supports consistency across providers and reinforces the importance of selecting companies familiar with these requirements.
Service offerings typically include:
- Evidence acquisition from computers, servers, and storage devices
- Mobile device forensics covering smartphones and tablets
- Network intrusion investigations and log analysis
- Email and communication analysis across platforms
- Data recovery from damaged or deliberately wiped devices
- Expert witness testimony and court report preparation
- Training and consultancy for internal investigation teams
These companies serve overlapping but distinct markets. Digital forensics services for legal professionals emphasise court-admissible evidence and expert testimony, whilst corporate-focused providers prioritise rapid incident response and business continuity. Private investigation firms cater to individuals needing evidence for family law matters, employment disputes, or personal security concerns. Understanding these nuances helps you select providers with relevant experience in your investigation type.
Comparing UK computer forensic companies: a snapshot of offerings and strengths
Direct comparison reveals how forensic companies differ in capabilities, pricing structures, and service focus. This snapshot helps you evaluate options against your specific requirements.
| Company | Expertise Areas | Turnaround Time | Pricing Transparency | Legal Experience |
|---|---|---|---|---|
| Computer Forensics Lab | Mobile, cloud, malware, general computing | Standard to expedited options | Itemised quotes available | Extensive court testimony |
| CCL Solutions | Mobile devices, app analysis | Variable by case complexity | Contact for quotes | Strong law enforcement focus |
| S-RM | Corporate investigations, compliance | Flexible for urgent cases | Enterprise pricing | Regulatory and internal matters |
| Kroll | Large-scale breaches, IP theft | Scalable resources | Customised proposals | Global litigation support |
| Stroz Friedberg | eDiscovery, commercial disputes | Project-based timelines | Engagement-specific | Expert witness network |
Evaluating strengths and limitations helps refine your selection:
- Specialist mobile forensics companies excel at extracting data from encrypted smartphones but may lack expertise in network intrusion analysis
- Large multinational firms offer global resources and 24/7 availability but often charge premium rates unsuitable for smaller investigations
- Boutique forensic labs provide personalised service and flexible pricing but may have limited capacity for urgent, large-scale cases
- Corporate-focused providers understand business contexts and regulatory requirements but may lack courtroom testimony experience
- Law enforcement-oriented companies possess deep technical expertise but might not prioritise commercial client communication standards
A common pitfall is the failure to properly document the chain of custody, which can render evidence inadmissible in court. This underscores why selecting companies with proven legal experience matters more than technical capabilities alone. The most sophisticated analysis becomes worthless if procedural lapses compromise evidence integrity.
Pro Tip: Request sample reports during the selection process. Quality forensic reports include clear methodology sections, detailed findings with supporting screenshots, and conclusions written for non-technical audiences. Companies confident in their work readily provide anonymised examples demonstrating their reporting standards and attention to detail.
Consider these practical factors:
- Geographic location affects response times for evidence collection and in-person consultations
- Industry specialisation indicates familiarity with sector-specific technologies and regulatory requirements
- Tool diversity suggests adaptability when primary methods encounter obstacles
- Staff qualifications and certifications reflect ongoing professional development
- Insurance coverage protects against potential errors or data breaches during handling
Balancing technical expertise, legal compliance, and practical considerations ensures you select a forensic partner capable of delivering credible evidence that withstands scrutiny. Review top digital forensics techniques to understand methodologies companies should employ, and consult chain of custody tips evidence resources to verify providers follow proper procedures throughout investigations.
Making the right choice: situational recommendations for different needs
Different investigation contexts demand tailored approaches to selecting forensic companies. Your priorities shift based on whether you’re pursuing litigation, investigating security incidents, or gathering personal evidence.
Legal professionals require forensic companies with proven courtroom experience and meticulous documentation practices. Prioritise providers who regularly testify as expert witnesses, understand rules of evidence, and produce reports meeting judicial standards. Their analysts should withstand cross-examination and explain technical findings clearly to judges and juries. Verify they maintain professional indemnity insurance and follow Law Society guidelines for expert witnesses. Timeline reliability matters critically when court dates approach, so assess their capacity to meet deadlines without compromising quality. Digital forensics corporate investigations often intersect with legal proceedings, making courtroom credibility essential even for internal matters that might escalate to litigation.
Corporate security teams need rapid response capabilities and business-focused communication. Select companies offering 24/7 availability for breach incidents, understanding that delayed forensic response allows attackers to cover tracks and increases damage. They should integrate smoothly with your IT department, respecting operational constraints whilst preserving evidence. Look for expertise in malware analysis, network forensics, and threat intelligence correlation. Their reports should support both technical remediation and executive briefings, translating findings into business risk language. Consider retainer arrangements providing priority access during emergencies.
Private individuals face unique challenges balancing cost constraints with evidence quality needs. Focus on companies offering transparent pricing for straightforward cases like recovering deleted messages or proving device tampering. They should explain legal limitations of private investigations and guide you toward admissible evidence collection methods. Compassionate communication matters when handling sensitive personal matters like infidelity or harassment cases. Verify they maintain strict confidentiality and secure data handling for private client information.
Follow these steps to evaluate forensic company fit:
- Define your investigation scope, including device types, data volumes, and legal context requiring analysis.
- Shortlist companies with relevant expertise, checking certifications, case studies, and client testimonials.
- Request initial consultations to assess communication quality, technical understanding, and proposed methodologies.
- Compare detailed quotes covering all phases from evidence acquisition through final reporting and potential testimony.
- Verify insurance coverage, professional memberships, and complaint handling procedures before engagement.
- Establish clear communication protocols, progress reporting schedules, and escalation procedures for urgent matters.
Expert-level nuances include understanding the intricacies of different file systems, the ability to bypass encryption, and the ability to analyse complex malware.
These technical capabilities separate competent forensic analysts from exceptional ones. During consultations, ask specific questions about their experience with encryption types relevant to your case, their success rates recovering data from damaged devices, and their familiarity with the specific applications or platforms central to your investigation. Generic answers suggesting they handle “all types” of forensics may indicate superficial expertise rather than deep specialisation.
Match company strengths to investigation priorities. Intellectual property theft cases benefit from analysts experienced in source code comparison and metadata analysis. Employment disputes require expertise in email forensics and application usage tracking. Cybersecurity incidents demand rapid malware analysis and network intrusion detection. Family law matters need sensitivity alongside technical proficiency in recovering communication histories.
Consider long-term relationships for organisations with ongoing forensic needs. Retainer arrangements provide cost predictability, priority response, and analysts familiar with your systems and security posture. They can conduct proactive assessments identifying vulnerabilities before incidents occur, shifting from reactive investigation to preventative security.
Review how to conduct digital forensics guide resources to understand proper investigation workflows, helping you evaluate whether prospective companies follow best practices. This knowledge empowers informed discussions during selection, ensuring you choose partners committed to evidence integrity and professional standards.
Explore specialised digital forensics solutions with Computer Forensics Lab
Computer Forensics Lab provides comprehensive digital forensics services tailored to legal professionals, corporate security teams, and private clients across the UK. Our London-based experts combine technical excellence with rigorous evidential standards, ensuring your investigations produce court-admissible evidence and actionable intelligence. We maintain strict chain of custody protocols, use validated forensic tools, and deliver detailed reports suitable for litigation or internal proceedings. Whether you’re investigating data breaches, employee misconduct, intellectual property theft, or personal matters requiring digital evidence, our team brings proven expertise across computing devices, mobile platforms, cloud services, and network forensics. Explore our step by step evidence collection digital investigations guide for practical insights, or review digital forensics data resources to understand how digital footprints support investigations. Contact us to discuss your specific forensic needs and discover how our expertise strengthens your case outcomes.
Frequently asked questions
What qualifications should a computer forensic company have?
Look for ISO 17025 accreditation, membership in professional forensic bodies, and adherence to national guidelines like those published by the Forensic Science Regulator. Staff should hold relevant certifications such as EnCE, GCFA, or CCE, demonstrating technical competence and ongoing professional development. Review digital forensics best practices to understand standards reputable companies follow.
How do forensic companies ensure data integrity during investigations?
They create forensic images using write-blocking hardware, generate cryptographic hashes to verify data hasn’t changed, and maintain detailed chain of custody logs documenting every action. All analysis occurs on copies, preserving original evidence in secure storage with access controls and environmental monitoring. Consult chain of custody digital evidence resources for detailed procedures.
What types of investigations benefit most from computer forensic services?
Legal disputes involving electronic evidence, cybersecurity incidents like data breaches or ransomware attacks, fraud investigations requiring financial record analysis, and intellectual property theft cases all benefit significantly. Employee misconduct investigations, family law matters involving digital communication, and regulatory compliance audits also frequently require forensic expertise. Explore corporate forensic investigations for business-specific applications.
How long does a typical forensic investigation take?
Timelines vary from days for straightforward mobile device analysis to months for complex multi-device investigations involving terabytes of data. Factors include data volume, encryption complexity, device condition, and analysis depth required. Urgent cases can receive expedited service, though this typically incurs premium pricing. Discuss timeline expectations during initial consultations to ensure alignment with your case deadlines.
What should I prepare before engaging a forensic company?
Document your investigation objectives, identify all devices and accounts requiring examination, and gather any relevant passwords or access credentials. Preserve devices in their current state, avoiding further use that might overwrite evidence. Prepare a timeline of relevant events and list specific questions you need answered. This preparation enables forensic analysts to develop targeted investigation plans and provide accurate cost estimates.
Recommended
- How To Choose A Digital Forensics Company | Computer Forensics Lab | Digital Forensics Services
- Complete Guide to Computer Forensics Services in the UK
- Computer forensics guide: digital evidence handling UK
- Corporate Forensics Investigations For UK Companies | Computer Forensics Lab | Digital Forensics Services