Digital forensic investigations in the UK demand precision, rigorous methodology, and strict adherence to legal standards. One misstep in evidence handling can invalidate months of work and jeopardise criminal prosecutions or civil litigation outcomes. For legal professionals, forensic investigators, and law enforcement agencies, understanding the structured steps of digital forensic investigation is essential to secure admissible evidence and build defensible cases. This guide outlines the complete workflow from initial preparation through final courtroom presentation, addressing both technical requirements and legal compliance.
Table of Contents
- Preparation: Setting The Foundation For Forensic Investigation
- Execution: Step-By-Step Process Of Forensic Data Collection And Analysis
- Verification And Reporting: Ensuring Accuracy And Legal Readiness
- Common Challenges And Best Practices In Forensic Investigations
- Explore Expert Digital Forensic Services For Your Investigations
Key takeaways
| Point | Details |
|---|---|
| Systematic approach protects evidence | Following proper forensic investigation steps maintains chain of custody and ensures admissibility in UK courts. |
| Technical and legal compliance are inseparable | Each phase requires both forensic expertise and adherence to UK legal frameworks including PACE and GDPR. |
| Documentation is paramount | Comprehensive records at every step defend against challenges to evidence integrity during cross-examination. |
| Professional expertise prevents costly errors | Complex digital environments and evolving technologies demand specialist knowledge to avoid evidence contamination. |
Preparation: setting the foundation for forensic investigation
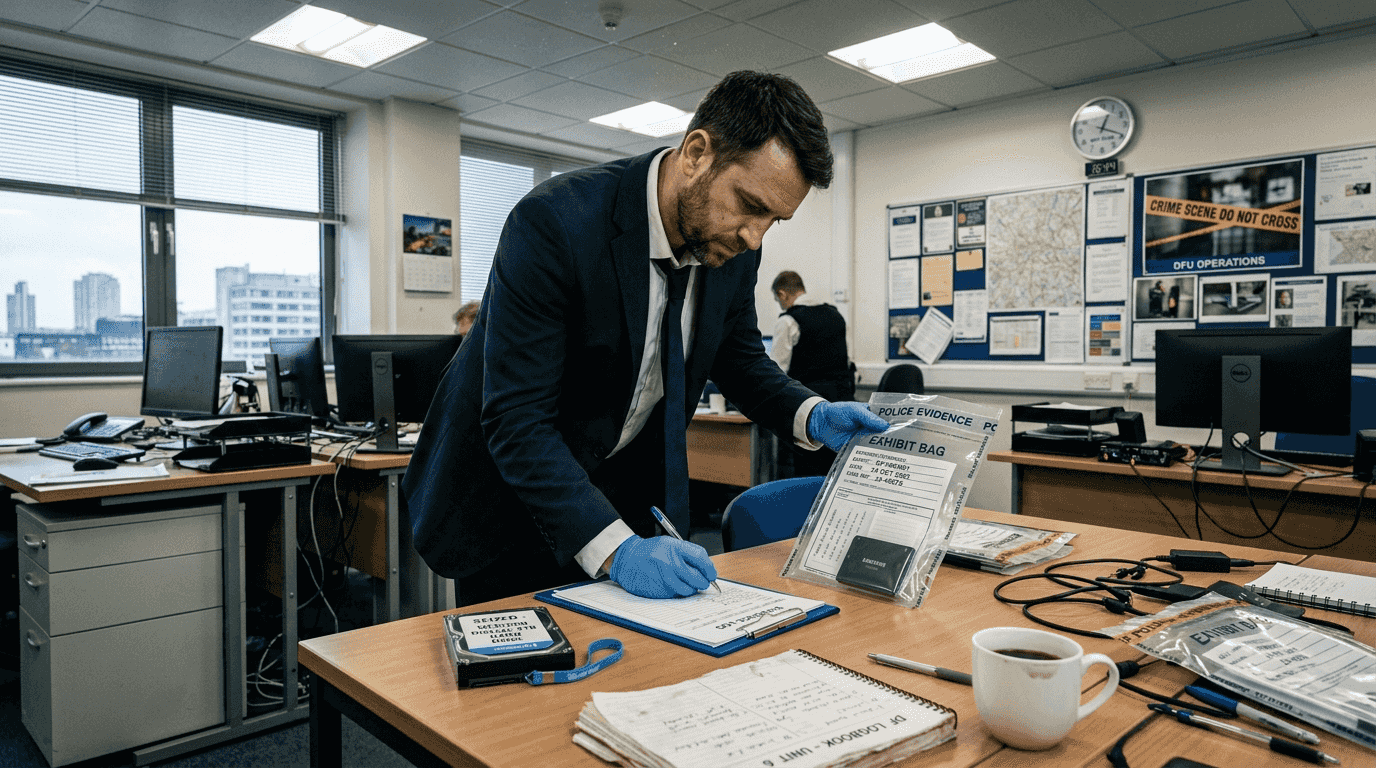
Before touching any digital device or data source, investigators must establish robust groundwork. The preparation phase determines whether evidence collected will withstand legal scrutiny or become inadmissible due to procedural failures.
Understanding legal frameworks forms the cornerstone of preparation. UK investigators operate within the Police and Criminal Evidence Act 1984 (PACE), Computer Misuse Act 1990, and Data Protection Act 2018. You must identify which statutory powers authorise evidence seizure for your specific case type. Civil cases may require different consent mechanisms than criminal investigations, whilst GDPR compliance affects how personal data is handled throughout the investigation.
Technical preparation involves assembling specialised forensic tools and validated software. Write blockers prevent accidental data modification during acquisition. Forensic imaging tools like FTK Imager or EnCase create bit-for-bit copies of storage media. Hash verification utilities generate cryptographic fingerprints proving data authenticity. Your forensic workstation should be forensically clean, air-gapped where necessary, and configured with licensed, court-accepted software versions.
Establishing chain of custody protocols before evidence collection begins is non-negotiable. Create documentation templates that capture who handled evidence, when, where, and why at every transfer point. Chain of custody forms should include unique evidence identifiers, timestamps, storage locations, and handler signatures. This paperwork trail becomes your defence when opposing counsel questions evidence integrity.
Pro tip: Create a pre-investigation checklist covering legal authorisations, technical tool verification, and stakeholder coordination to ensure nothing is overlooked under time pressure.
Defining investigation scope prevents resource waste and focuses efforts on relevant evidence sources. Identify target devices (computers, mobile phones, servers, cloud accounts), timeframes for investigation, and specific data types sought. Coordinate with legal counsel to understand disclosure obligations and with law enforcement if criminal proceedings run parallel to civil matters.
| Preparation element | Key actions | Legal consideration |
|---|---|---|
| Legal compliance | Obtain warrants, consents, or court orders | Ensure PACE and GDPR compliance |
| Technical setup | Validate tools, prepare forensic workstation | Use court-accepted software versions |
| Documentation | Create chain of custody templates | Maintain audit trail for court |
| Scope definition | Identify devices, timeframes, data types | Align with legal strategy and disclosure |
Secure your forensic work environment physically and digitally. Evidence storage rooms require access controls, environmental monitoring (temperature, humidity), and intrusion detection. Digital security includes encrypted storage, role-based access permissions, and comprehensive logging of all evidence interactions. These measures protect forensic evidence integrity and demonstrate professional standards to courts.
Execution: step-by-step process of forensic data collection and analysis
Once preparation is complete, the core investigative work begins. This phase transforms raw digital devices into analysed evidence ready for legal proceedings. Each step must be meticulously documented and technically sound.
Step 1: Forensic imaging with write protection. Connect target devices to write blockers, hardware devices that permit read-only access whilst preventing any data modification. Create forensic images (exact bit-for-bit copies) of storage media using validated tools. Image the entire physical drive, not just accessible partitions, to capture deleted files, slack space, and hidden partitions. Document the imaging process with photographs, equipment serial numbers, and start/end timestamps.
Step 2: Verify data integrity through cryptographic hashing. Immediately after imaging, generate hash values (MD5, SHA-256) for both the original media and forensic copy. These cryptographic fingerprints prove the copy matches the original exactly. Document hash values in your evidence log. Re-verify hashes before analysis begins and again before presenting evidence in court. Any hash mismatch indicates potential tampering or corruption.
Step 3: Analyse forensic images for relevant artefacts. Load forensic images into analysis software (Autopsy, X-Ways, Cellebrite for mobile devices). Search for evidence matching your investigation scope: deleted files, browser history, email communications, application data, system logs. Automated keyword searches accelerate the process, but manual examination often uncovers context that algorithms miss. Document every search parameter, filter applied, and artefact discovered with screenshots and notes.
Step 4: Document findings comprehensively. Record each piece of evidence with precise metadata: file path, creation/modification timestamps, hash value, content description, and relevance to the investigation. Create a findings matrix linking digital artefacts to investigation questions. Screenshot relevant data with visible metadata. Your documentation should enable another examiner to independently verify your conclusions.
Step 5: Balance manual and automated analysis methods. Both approaches offer distinct advantages in forensic data analysis.
| Analysis method | Advantages | Disadvantages |
|---|---|---|
| Manual examination | Identifies context and relationships, understands nuanced evidence | Time-consuming, risk of human oversight on large datasets |
| Automated tools | Processes vast data volumes quickly, consistent methodology | May miss context, requires validation of results, potential false positives |
| Hybrid approach | Combines speed with contextual understanding | Requires expertise in both manual techniques and tool operation |
Pro tip: Always validate automated search results manually before including them in your evidence report, as false positives can undermine credibility during cross-examination.
Contamination risks threaten evidence validity at multiple points. Never analyse evidence on the original device. Avoid using personal or investigative computers for evidence storage. Document your forensic environment configuration to prove isolation from contamination sources. Maintain separate evidence handling for different cases to prevent cross-contamination. These precautions protect your work from challenges during digital evidence collection procedures.
Timestamp everything. Modern digital forensics involves hundreds of discrete actions, from initial evidence seizure through final analysis. Each action should appear in your case log with precise date, time, actor, and purpose. This granular documentation demonstrates thoroughness and creates an unassailable audit trail.
Verification and reporting: ensuring accuracy and legal readiness
After analysis concludes, verification and reporting transform raw findings into courtroom-ready evidence. This phase subjects your work to rigorous quality control and packages results for legal consumption.
Cross-verification validates findings through independent methods. If automated tools identified deleted emails, manually examine file structures to confirm. If timeline analysis suggests specific user actions, corroborate with system logs and registry entries. Peer review by another qualified examiner adds another verification layer, particularly for complex or high-stakes cases. This redundancy catches errors and strengthens your position when challenged.
Chain of custody documentation reaches its culmination during verification. Audit every evidence transfer, storage location change, and analysis action. Your chain of custody log should show continuous, documented control from initial seizure through courtroom presentation. Gaps or inconsistencies invite challenges to evidence admissibility. Complete your documentation with final verification signatures confirming evidence remained unaltered throughout the investigation.
Forensic reports must communicate technical findings to non-technical legal audiences whilst maintaining scientific rigour. Structure reports with an executive summary, detailed methodology section, findings with supporting evidence, and conclusions. Avoid jargon without explanation. Include screenshots, data tables, and timeline visualisations to illustrate key points. Methodology descriptions should be sufficiently detailed that another examiner could reproduce your work.
“The forensic report is your advocate when you cannot be present. It must speak clearly, defend its conclusions with evidence, and withstand hostile cross-examination.”
Understand courtroom requirements before finalising your report. UK courts expect expert witnesses to comply with Criminal Procedure Rules Part 19 for criminal cases or Civil Procedure Rules Part 35 for civil matters. Your report must state your qualifications, declare any conflicts of interest, and acknowledge the limits of your conclusions. Overstatement invites successful challenges. Measured, evidence-based conclusions enhance credibility.
Common reporting mistakes undermine otherwise solid investigations. Avoid opinion without supporting evidence. Never extrapolate beyond what data actually shows. Do not omit exculpatory evidence (findings that contradict your hypothesis). Ensure all referenced exhibits are properly labelled and attached. Proofread meticulously, as errors suggest carelessness that opposing counsel will exploit.
Prepare for expert testimony by reviewing your entire case file. Anticipate cross-examination questions about methodology, tool reliability, and alternative interpretations. Practice explaining technical concepts in plain language. Understand that your role is to assist the court impartially, not to advocate for the instructing party. This objectivity, combined with thorough preparation, establishes you as a credible expert whose forensic analysis withstands judicial scrutiny.
Common challenges and best practices in forensic investigations
Even experienced investigators encounter obstacles that threaten evidence recovery or legal compliance. Recognising these challenges early and applying proven solutions protects investigation outcomes.
Technical challenges frequently centre on data accessibility. Modern encryption (FileVault, BitLocker, full-disk encryption) renders data unreadable without credentials. Solutions include obtaining passwords through legal compulsion, exploiting weak encryption implementations, or accessing data whilst the device remains powered and unlocked. Data corruption from physical damage, logical file system errors, or partial deletion complicates recovery. Specialised recovery tools and techniques may salvage fragments, but you must document uncertainty about completeness.
Legal challenges test your understanding of applicable statutes and procedural requirements. Obtaining search warrants or production orders requires demonstrating reasonable grounds and necessity. Privacy concerns, particularly under GDPR, limit what data you may collect and retain. Cross-border investigations encounter jurisdictional complexities and mutual legal assistance treaty delays. Engaging legal counsel early helps navigate these obstacles whilst maintaining evidence admissibility.
Human errors pose perhaps the greatest risk to forensic investigations. Documentation lapses create chain of custody gaps. Improper evidence handling contaminates data. Confirmation bias leads investigators to overlook contradictory evidence. Mitigation strategies include standardised operating procedures, checklists for critical steps, and peer review of findings before finalising reports.
Pro tip: Before powering down any device, photograph the screen and check for full-disk encryption indicators, as shutting down may permanently lock access to unencrypted data.
Best practices from experienced practitioners improve investigation efficiency and defensibility:
- Double-check hash values at every evidence transfer point, not just initial imaging and final verification.
- Maintain contemporaneous notes during analysis rather than reconstructing documentation later from memory.
- Photograph evidence in situ before collection, documenting surrounding context and connections.
- Use multiple forensic tools for critical findings, as tool bugs or limitations occasionally produce incorrect results.
- Communicate regularly with instructing solicitors or case officers to align forensic work with evolving legal strategies.
Continuing professional development keeps investigators current with technology evolution and legal changes. Attend specialised training in mobile forensics, cloud investigations, or cryptocurrency tracing. Pursue certifications like EnCE, GIAC, or CCE to demonstrate expertise. Engage with professional bodies such as the Chartered Society of Forensic Sciences. Technology advances rapidly; yesterday’s best practices may be inadequate for tomorrow’s digital forensics challenges.
Explore expert digital forensic services for your investigations
Navigating the complexities of digital forensic investigations requires specialised expertise, validated tools, and deep understanding of UK legal requirements. When cases demand absolute precision and courtroom credibility, professional support ensures nothing is overlooked.
Computer Forensics Lab provides comprehensive digital forensic investigation services tailored for UK law enforcement, legal professionals, and forensic experts. Our London-based team combines technical mastery with extensive courtroom experience, delivering expert witness reports that withstand rigorous cross-examination. From initial evidence collection through final testimony, we maintain chain of custody and apply court-accepted methodologies that protect evidence integrity.
Whether you require mobile device forensics, cloud data analysis, or complex data recovery, our digital forensics services cover the full spectrum of modern investigative needs. We understand the pressures legal professionals face and deliver results that support successful case outcomes.
Frequently asked questions
What are the key steps in forensic investigation?
Forensic investigations follow a systematic workflow: preparation (legal compliance, tool validation, scope definition), acquisition (forensic imaging with write protection), preservation (hash verification, secure storage), analysis (examining data for relevant artefacts), and reporting (documenting findings in court-ready format). Each step builds upon the previous one to maintain evidence integrity. Skipping or rushing any phase risks evidence inadmissibility or investigative failure.
How do forensic investigators ensure evidence integrity?
Investigators maintain evidence integrity through comprehensive chain of custody documentation recording every person who handled evidence, when, and why. Write blockers prevent accidental modification during imaging. Cryptographic hash values (MD5, SHA-256) prove forensic copies match originals exactly. Secure storage with access controls and audit logs prevents tampering. Regular hash re-verification throughout the investigation detects any unauthorised changes immediately.
What are common challenges in digital forensic investigations?
Encrypted or physically damaged storage media often blocks access to critical evidence, requiring specialised recovery techniques or legal compulsion for credentials. Privacy laws like GDPR restrict what personal data investigators may collect and retain, particularly in civil matters. Human error during evidence handling, such as documentation lapses or improper imaging procedures, can invalidate otherwise solid investigative work. Technical complexity and rapidly evolving technology demand continuous professional development.
Can forensic reports be used in UK courts?
Properly prepared forensic reports are admissible as expert evidence in UK criminal and civil proceedings. Reports must comply with Criminal Procedure Rules Part 19 or Civil Procedure Rules Part 35, stating the expert’s qualifications, methodology, and conclusions supported by evidence. Expert testimony typically accompanies reports to explain technical findings and respond to cross-examination. Courts expect objectivity, transparency, and adherence to recognised forensic standards throughout the investigation process.