Many legal and corporate security professionals believe that simply collecting digital data is sufficient for investigation purposes. This misconception has led to countless cases where critical electronic evidence became inadmissible in UK courts due to improper handling procedures. With 89% of criminal investigations now involving some form of digital evidence, understanding proper collection, preservation, and chain of custody protocols has become essential for successful legal outcomes in 2026. This comprehensive guide equips UK legal professionals, corporate security teams, and law enforcement agencies with the knowledge to handle electronic evidence correctly, maintain its integrity throughout investigations, and ensure admissibility in court proceedings.
Table of Contents
- Understanding Electronic Evidence And Its Legal Importance
- Best Practices For Collecting And Preserving Electronic Evidence
- Ensuring Chain Of Custody And Documentation Throughout Investigations
- Applying Forensic Analysis Techniques And Legal Compliance In 2026
- Enhance Your Digital Investigations With Expert Forensic Services
Key takeaways
| Point | Details |
|---|---|
| Chain of custody | Documenting every handler and transfer protects evidence integrity and ensures court admissibility |
| Forensic imaging | Creating exact copies preserves original data without alteration, enabling safe analysis |
| Legal compliance | Following UK frameworks like PACE 1984 ensures evidence meets procedural standards |
| Specialist expertise | Certified forensic professionals strengthen investigation outcomes through proven methodologies |
| Continuous adaptation | Digital forensic best practices evolve rapidly, requiring ongoing training and updated protocols |
Understanding electronic evidence and its legal importance
Electronic evidence encompasses any data stored or transmitted in digital form that may prove relevant to legal proceedings, investigations, or corporate security matters. Digital footprints everywhere include information from computers, mobile devices, cloud services, and network systems. This evidence type has grown exponentially in importance as virtually every aspect of modern business and personal activity generates digital traces.
The UK legal system increasingly relies on electronic evidence across criminal prosecutions, civil litigation, employment disputes, and regulatory investigations. Courts now regularly encounter cases where emails, text messages, social media posts, financial transactions, and system logs form the cornerstone of legal arguments. The challenge lies not in the availability of digital data but in its proper collection and presentation to meet stringent admissibility standards.
Several characteristics make electronic evidence particularly complex:
- Volatility: Data can be altered, deleted, or overwritten easily, sometimes automatically
- Volume: Modern devices contain enormous amounts of information requiring specialised analysis
- Technical complexity: Understanding file systems, metadata, and digital artefacts demands expertise
- Fragility: Improper handling can inadvertently modify timestamps, file attributes, or content
UK legal standards governing electronic evidence derive from the Police and Criminal Evidence Act 1984, Criminal Procedure Rules, and Civil Procedure Rules. These frameworks establish requirements for authenticity, reliability, and proper handling procedures. Evidence that fails to meet these standards faces exclusion from proceedings, potentially undermining entire cases regardless of its substantive value.
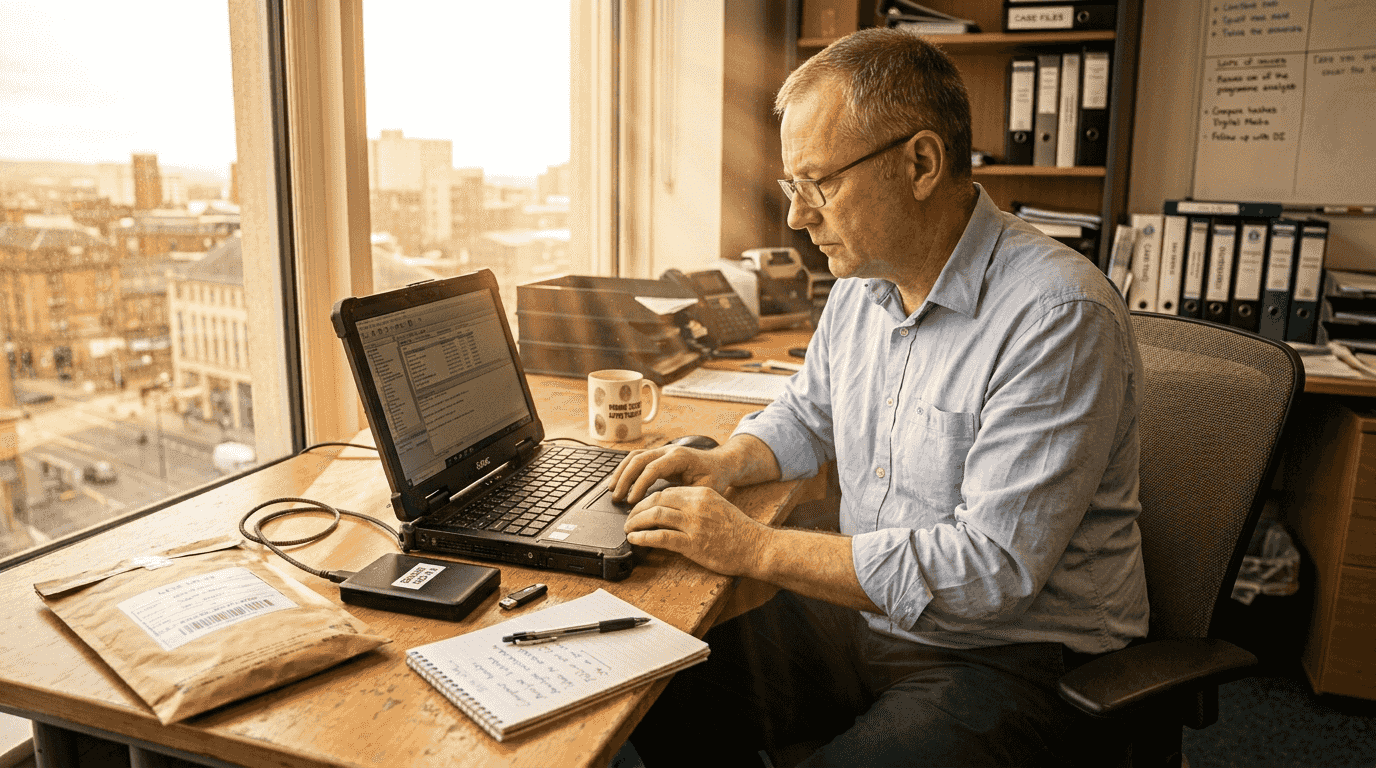
Specialised digital forensics services play a crucial role in managing these complexities. Forensic experts employ scientifically validated methodologies to collect, preserve, analyse, and present electronic evidence whilst maintaining its integrity. Their involvement often proves decisive in establishing the credibility and admissibility of digital materials in legal contexts.
Best practices for collecting and preserving electronic evidence
Proper evidence collection begins before any device is touched. Professionals must document the scene thoroughly, photograph device positions and connections, and note any visible information on screens. This initial documentation establishes context and helps reconstruct the original state if questions arise later.
The collection protocol varies by device type but follows consistent principles:
- Isolate the device from networks to prevent remote wiping or data modification
- Document the device’s power state and preserve it when possible
- Use write blockers to prevent any modifications during imaging
- Create forensic images using certified tools that generate hash values
- Verify image integrity through cryptographic hashing
- Package devices in anti-static bags with tamper-evident seals
- Transport using secure containers that protect against physical and environmental damage
Maintaining an unbroken chain of custody is essential to protect digital evidence integrity and admissibility in court. Every person who handles evidence must be documented, along with dates, times, purposes, and locations. This meticulous record keeping demonstrates that evidence remained secure and unaltered throughout the investigation.
Forensic imaging represents the gold standard for evidence preservation. Rather than examining original devices directly, investigators create bit-by-bit copies that capture every sector of storage media, including deleted files and unallocated space. These images allow comprehensive analysis whilst the original device remains secured and unmodified. Modern forensic imaging tools generate cryptographic hash values that mathematically prove the copy’s accuracy and detect any subsequent alterations.
Storage requirements demand careful attention. Evidence must be kept in climate-controlled environments with restricted access, ideally in locked evidence rooms or safes. Digital media is particularly sensitive to magnetic fields, temperature extremes, and humidity. Proper digital evidence preservation methods include using Faraday bags for mobile devices to block wireless signals and maintaining redundant copies stored in separate locations.
Pro Tip: Always use certified forensic tools rather than standard copying utilities, as forensic tools preserve metadata and create verifiable hash values that standard software cannot provide, significantly strengthening evidence credibility in legal proceedings.
Ensuring chain of custody and documentation throughout investigations
Chain of custody refers to the chronological documentation showing the seizure, custody, control, transfer, analysis, and disposition of evidence. In electronic evidence handling, this concept becomes particularly critical because digital data’s invisible nature makes unauthorised access or modification difficult to detect without proper safeguards.
UK courts scrutinise chain of custody documentation intensely. Any gap or inconsistency can raise reasonable doubt about evidence integrity, potentially leading to exclusion. The legal principle underlying this requirement is straightforward: evidence must be demonstrably the same material collected at the scene, unaltered and uncontaminated by subsequent handling.
Key elements of effective chain of custody management include:
- Unique identification: Each piece of evidence receives a distinctive identifier linking it to case documentation
- Access controls: Physical and digital access limited to authorised personnel with documented justification
- Transfer logs: Detailed records of every custody change, including sender, receiver, date, time, and purpose
- Storage security: Evidence maintained in secure facilities with environmental monitoring and intrusion detection
- Audit trails: Regular reviews ensuring documentation completeness and identifying any discrepancies
A robust chain of custody tracking system typically captures the following information:
| Field | Purpose | Example |
|---|---|---|
| Evidence ID | Unique identifier | CF-2026-0847-MOB |
| Description | Item details | iPhone 14 Pro, black, IMEI 358426094732156 |
| Custodian | Current holder | DS Sarah Mitchell, Metropolitan Police |
| Location | Storage details | Evidence Room 3, Locker 47B |
| Transfer date | Custody change | 15 March 2026, 14:32 GMT |
| Purpose | Reason for transfer | Forensic examination |
| Condition | Physical state | Sealed in anti-static bag, tamper seal intact |
Documenting every person who handles digital evidence and every transfer is fundamental for a secure chain of custody. This documentation must be contemporaneous, meaning recorded at the time of each action rather than reconstructed later. Retrospective documentation lacks credibility and invites challenges from opposing counsel.
Common challenges in maintaining chain of custody include personnel changes during long investigations, evidence transfers between agencies, and temporary removals for court presentations. Each scenario requires careful planning and documentation. When evidence moves between organisations, both parties must sign transfer documents confirming the item’s condition and ensuring continuous accountability.
Pro Tip: Implement standardised digital tracking systems using barcode or RFID technology to minimise human error in documentation, automatically timestamp all transfers, and generate comprehensive audit trails that demonstrate meticulous evidence handling to courts and regulatory bodies.
Modern chain of custody tracking solutions integrate with case management systems, providing real-time visibility into evidence location and status. These systems alert supervisors to approaching storage deadlines, flag unusual access patterns, and generate court-ready custody reports. Investing in such technology demonstrates organisational commitment to evidence integrity and reduces the administrative burden on investigation teams.
Applying forensic analysis techniques and legal compliance in 2026
Forensic examination of electronic evidence follows a structured methodology designed to extract relevant information whilst maintaining scientific rigour and legal admissibility. The process typically progresses through distinct phases: acquisition, examination, analysis, and reporting. Each phase employs specific techniques and generates documentation that collectively demonstrates the reliability of findings.
Forensic imaging and data recovery are critical to extracting usable evidence without altering source data. Acquisition creates working copies that investigators can examine using various tools without risk to the original. This approach aligns with the fundamental forensic principle of preservation: original evidence must remain pristine and available for independent verification.
Examination involves systematically processing acquired data to identify items of potential relevance. Forensic software can recover deleted files, extract metadata, analyse internet history, decrypt protected documents, and reconstruct user activities. Advanced techniques include timeline analysis, which correlates events across multiple data sources to establish sequences of actions, and keyword searching, which identifies communications or documents containing specific terms.
Different forensic techniques suit particular investigation needs:
| Technique | Best for | Limitations |
|---|---|---|
| File carving | Recovering deleted or fragmented files | May produce incomplete or corrupted results |
| Memory analysis | Capturing volatile data like passwords and running processes | Requires immediate action before device power loss |
| Network forensics | Investigating data breaches and unauthorised access | Demands significant storage for packet capture data |
| Mobile forensics | Extracting messages, location data, and app information | Encryption and security features may block access |
| Cloud forensics | Analysing remotely stored data and SaaS applications | Jurisdictional issues and service provider cooperation needed |
UK legal standards significantly influence forensic methodology. The Criminal Procedure Rules require disclosure of all material that might reasonably be considered capable of undermining the prosecution case or assisting the defence. This obligation means forensic examiners must conduct thorough, unbiased examinations rather than selectively seeking incriminating evidence. Documentation must demonstrate that examinations followed scientifically accepted procedures and that conclusions are supported by objective findings.
Expert witness testimony often proves crucial in electronic evidence cases. Forensic specialists must explain technical concepts to judges and juries in accessible language whilst maintaining scientific accuracy. Effective expert witnesses combine deep technical knowledge with communication skills, helping courts understand how evidence was obtained, what it demonstrates, and why conclusions are reliable. Their credibility depends on qualifications, experience, adherence to professional standards, and transparent methodology.
Collaboration between forensic data analysis specialists and legal teams enhances case outcomes significantly. Early involvement of forensic experts helps legal professionals understand what evidence might exist, how to preserve it properly, and what analysis could support their case theory. Regular communication ensures examinations focus on legally relevant questions and that findings are presented in formats courts can readily understand and apply.
Best practices for this collaboration include:
- Pre-examination conferences to clarify investigation objectives and legal requirements
- Interim reporting to inform ongoing legal strategy and identify additional examination needs
- Joint preparation for expert testimony, ensuring technical explanations align with legal arguments
- Coordination on disclosure obligations, identifying all material requiring production to opposing parties
The role of forensic consultant reviewing digital evidence extends beyond technical analysis to strategic case support. Experienced consultants can assess the strength of digital evidence, identify weaknesses in opposing evidence, and recommend additional investigative steps. Their involvement often proves decisive in complex cases where electronic evidence forms the primary basis for legal claims or defences.
Enhance your digital investigations with expert forensic services
Navigating the complexities of electronic evidence handling requires specialised expertise that many legal and corporate security teams lack in-house. Computer Forensics Lab provides comprehensive digital forensics services tailored specifically for UK legal professionals, law enforcement agencies, and corporate investigators. Our certified forensic consultants bring decades of combined experience in evidence collection, preservation, analysis, and court presentation, ensuring your digital evidence meets the highest standards for admissibility and persuasiveness. From initial device seizure through expert witness testimony, we support every phase of digital forensic investigations with proven methodologies and meticulous documentation. Understanding how forensic consultants impact legal outcomes can transform your approach to cases involving electronic evidence, providing the technical foundation and credibility essential for successful prosecution or defence in 2026’s increasingly digital legal landscape.
FAQ
What is the chain of custody and why is it crucial?
Chain of custody documents every person who handles evidence, along with dates, times, locations, and purposes of each transfer. This meticulous record keeping proves that evidence remained secure and unaltered from collection through court presentation. Without an unbroken chain of custody digital evidence faces potential exclusion from legal proceedings, as courts cannot verify its integrity and authenticity.
How can forensic imaging protect original electronic evidence?
Forensic imaging creates exact bit-by-bit copies of storage media, capturing all data including deleted files and unallocated space without modifying the original device. Investigators analyse these images whilst the original remains secured and pristine, available for independent verification. This approach prevents accidental alterations during examination and allows multiple experts to review identical copies, ensuring forensic imaging legal evidence maintains its integrity throughout investigations.
What legal frameworks apply to handling electronic evidence in the UK?
The Police and Criminal Evidence Act 1984 establishes fundamental requirements for evidence collection, handling, and admissibility in criminal proceedings. Criminal Procedure Rules and Civil Procedure Rules further specify disclosure obligations, expert evidence standards, and procedural fairness requirements. These frameworks mandate that electronic evidence be obtained lawfully, handled properly to prevent contamination, and presented with sufficient authentication to demonstrate reliability and relevance to the matters in dispute.
When should organisations involve forensic specialists in investigations?
Organisations should engage forensic specialists immediately upon suspecting incidents requiring electronic evidence collection, ideally before any devices are touched. Early involvement ensures proper preservation procedures, prevents inadvertent evidence destruction, and establishes robust chain of custody from the outset. Forensic experts can also advise on legal requirements, assess what evidence might exist, and develop examination strategies aligned with investigation objectives, significantly improving outcomes compared to retroactive involvement after evidence has been compromised.